NSW agencies struggle with security basics

For those with an interest in information security, who would like a sobering read to take the edge off the holiday cheer, the Report on Internal Controls and Governance 2017 from the Audit Office of New South Wales fits the bill.
Released prior to Christmas, the report details the extent to which NSW government agencies are struggling to fulfil the basics of security, which is even more concerning given the agencies commonly handle personal citizen data.
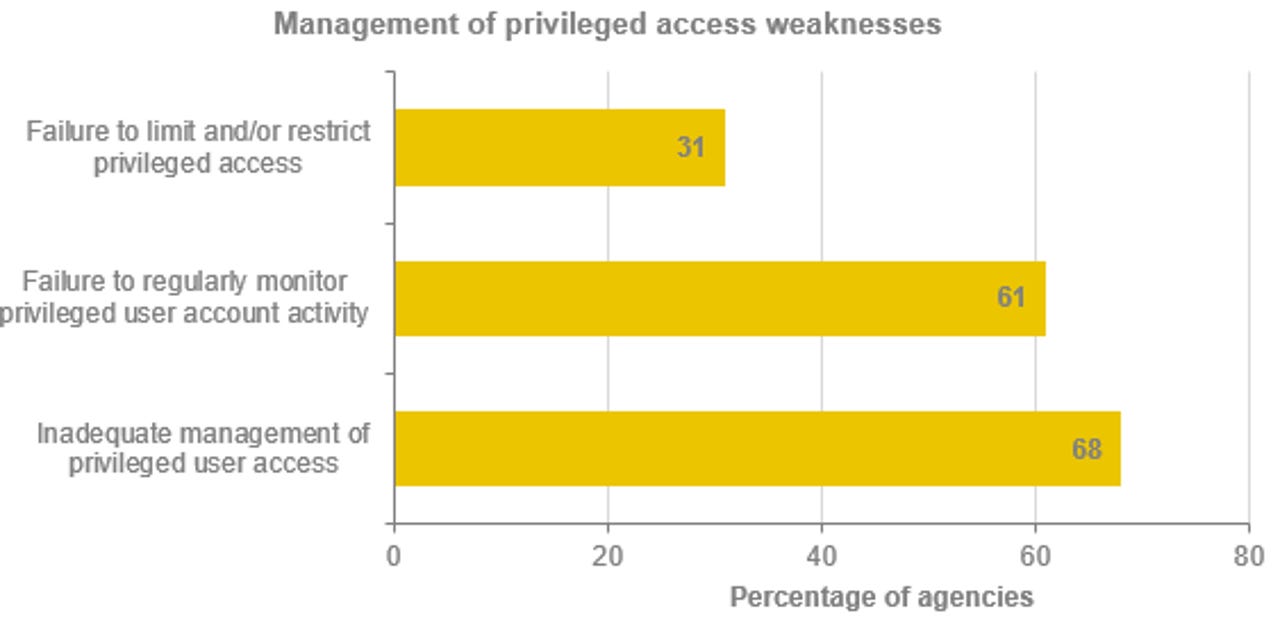
"Most agencies do not sufficiently monitor or restrict privileged access to their systems and some do not enforce password controls," the report states.
The audit office found 68 percent of agencies did not "adequately manage" who has access to systems.
"We found that one agency had 37 privileged user accounts, including 33 that were dormant," the office said. "The agency had no formal process to create, modify or deactivate privileged users."
During the year, the office said the NSW government agencies it looked at experienced 8,503 cyber attacks, a significant absolute increase on the 1,558 attacks reported last year and 603 attacks a year prior. However, there are a pair of caveats: Two agencies reported 7000-odd attacks between them; and there is no common definition of "cyber attack" within the agencies.
"The extent of the cyber security threat is unknown because agencies define a 'cyber attack' differently," the report said.
"As there are different approaches to what agencies record and report, and agencies apply different definitions for a 'cyber attack', the number and nature of cyber attacks is unknown."
To solve its definition problem, NSW would do well to follow the lead of the federal government, which is in the process of creating its Cyber Security Lexicon. Australia does not need conflicting cyber definitions moved up from the agencies, to a level where states potentially have their own unique definitions and Canberra has yet another one.
Parts of the report make for truly head-scratching moments: 5 percent of agencies "do not consider that cyber attacks pose a risk at all"; one agency does not regularly update its anti-virus signatures; and one agency last tested its disaster recovery plan four years ago.
The report found 13 percent of agencies did not maintain a complete inventory of IT systems, the same percentage did not have a disaster recovery plan in place for all critical systems, and 11 percent failed to "adequately identify" critical systems and business functions.
It also found 14 percent of agencies that use shared services, fail to have a service level agreement (SLA) in place. Of those that do have a SLA, 84 percent do not spell out penalties for underperformance, 60 percent fail to detail what controls the service provider must maintain, 20 percent do not have performance targets.
"IT control deficiencies were the most common source of internal control issues in our 2016-17 audits of NSW agencies," NSW Auditor-General Margaret Crawford said in a statement.
For a state that is pushing digital initiatives with gusto, it should be concerning that a number of agencies are failing to pass the equivalent of a security 101 course.
And the alarms should really ring when you take into account that of the authorities able to access Australia's metadata retention systems, four fall under the Audit Office's remit: NSW Police; NSW Crime Commission; NSW Independent Commission Against Corruption; and NSW Police Integrity Commission.
Finally, in case the idea of the federal government doing better on the security 101 takes hold, at the time of writing, the site of the Australian Commission on Safety and Quality in Health Care has been inaccessible without making a security exemption in your browser thanks to an SSL certificate that expired on December 22.
Related Coverage
NSW government launches DigitalNSW platform and data marketplace
DigitalNSW acts as a recording tool for government agencies and their projects, while D Marketplace allows citizens to download multiple datasets on one site.
NSW government begins digital driver's licence trial in Dubbo
The New South Wales government plans to follow up the digital driver's licence trial with a statewide rollout by next year.
Service NSW wants to share technology for cross-border service delivery
Service NSW's acting CEO told ZDNet that the organisation should be opening its technology to the rest of the country to assist in citizen service delivery.
NSW Police targeting shows the ethical dangers of secret algorithms
Once the unknown and unaccountable process decides you're a potential future criminal, simply wearing the 'wrong' clothes and sitting in the 'wrong' train carriage can attract police attention.
NSW Department of Justice transforms back end with ServiceNow
The state's justice department has turned to ServiceNow to transform its IT and back-office service management as part of its leap into digital service delivery.