Despite security risks, older Windows versions plague thousands of businesses

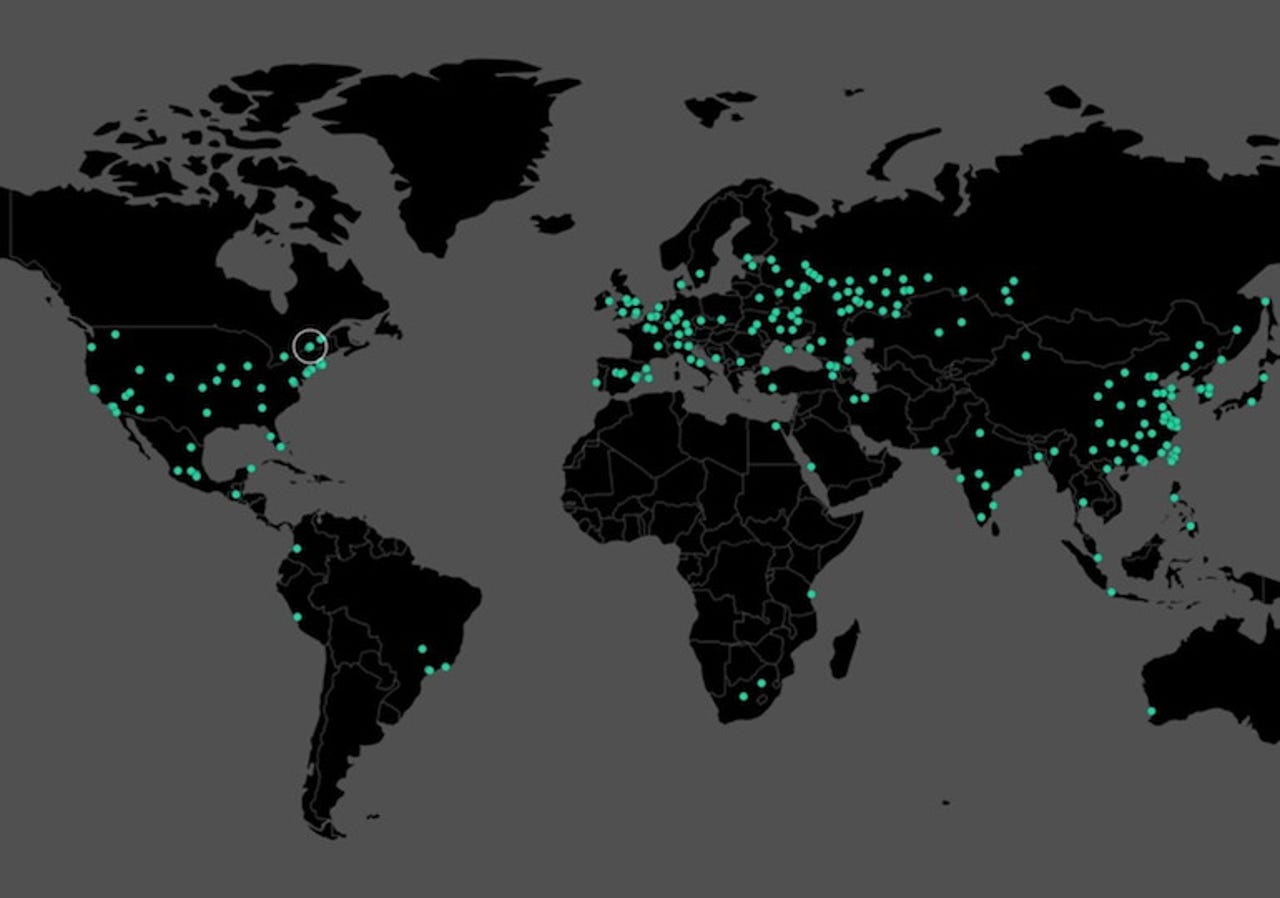
A map showing where WannaCry ransomware was installed. (Image: MalwareTech)
After the global cyberattacks on Friday that infected hundreds of thousands of computer with the WannaCry ransomware, the blame game has begun.
Who was behind the attack? How did the NSA lose control of its hacking tools used as part of this huge ransomware attack? Should we blame Microsoft for not patching older versions of Windows that were left vulnerable to the attack?
As it happens, thousands of businesses may only have themselves to blame.
According to recently released data from IT networking site Spiceworks, about half of all businesses still have at least one computer running Windows XP, despite the aging operating system losing Microsoft security support after more than a decade since its release in early-2014.
That means for over three years, these machines haven't been patched with the latest security updates, including the fix released in March that could've prevented machines from getting infected. (Following the outbreak, Microsoft released a rare, emergency out-of-support patch.)
Granted, some companies will have more machines running Windows XP and Vista, which lost support earlier this year, than others. Some businesses may rely on the aging operating system for their entire fleet of computers, whereas others may rely on one or two machines running custom-built machines, like MRI or X-ray scanners in hospitals, for example, which aren't always connected to the internet, making them less vulnerable to malware and ransomware.
The data shows that newer operating systems that were patched prior to last week's ransomware attacks, including Windows 7 and Windows 10, make up a 83 percent share of all business computers.
But despite the risks, Windows XP and Vista still take up a 15 percent share across the corporate world -- representing hundreds of thousands of computers.
It's worth noting that not one single set of data offers a perfectly accurate figure of how many devices are vulnerable to these kinds of mass ransomware events or other kinds of cyberattacks. Spiceworks, which has a commercial stake in the security space, says it uses inventory data to see computers that may be networked but not connected to the internet. Other sources rely on different methodologies, such as the US government's own digital analytics service, which bases its data on visitors directly accessing government sites. It said just over 1 percent of all visitors in the past three months were running Windows XP or Vista.
The question remains: for all the benefits that software updates provide, why the apathy?
"Many companies subscribe to the theory that if it's 'not broke, don't fix it,' especially those that aren't prioritizing IT," said Peter Tsai, a senior technology analyst at Spiceworks. "As a result, many IT departments lack the resources and budget needed to upgrade to newer operating systems like Windows 10. It takes time to upgrade all systems in an organization and train end users on the new features and functionality."
In all, just over half of all businesses say that there's no need to update because the current system still works. Others cite IT pressures and lack of time, investments, or budget constraints.
Those barriers can translate into real losses. Take what happened with last week's cyberattack. Dozens of hospitals around the UK were affected, with some forced to turn patients away. But unlike NHS trusts and hospitals in England and Scotland which suffered significantly at the hands of the ransomware attack late last week, NHS Wales wasn't affected by the ransomware attack at all, a feat largely attributed to the fact the health system recently updated its entire network.
"Now more than ever, it's critical for IT professionals to make a business case for more resources," said Tsai.
If this ransomware attack has proven anything, investing in security isn't just a good idea, it's mission critical.