Police arrest Mariposa botnet masters, 12M+ hosts compromised
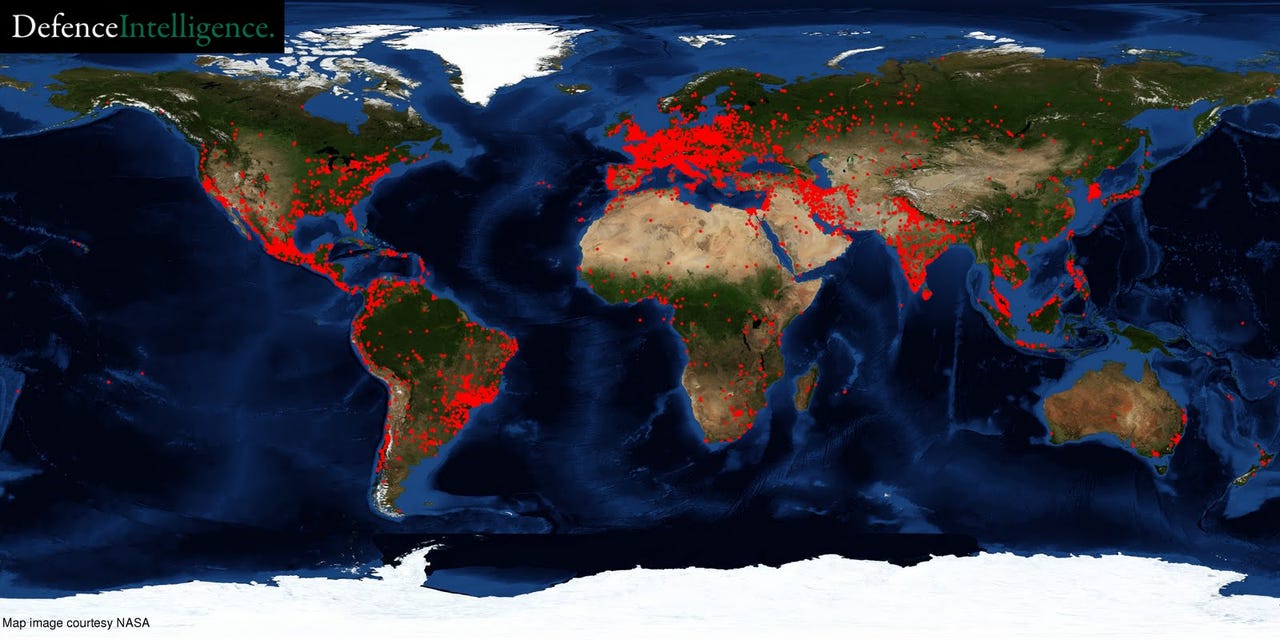
According to a statement published by the Spanish Ministry of Interior, the botnet masters behind a 12M+ infected hosts botnet dubbed Mariposa, were arrested in a cooperative effort between law enforcement, security vendors and the academic community.
Following the arrest of one of the botnet masters, law enforcement officers seized sensitive data belonging to 800,000 users across 190 countries, and found evidence of infected hosts located within the networks of 500 of the US Fortune 1,000 companies and more than 40 major banks.
Just how sophisticated were the botnet masters behind Mariposa? You'll be surprised to find out.
- On December 23 2009, in a joint international operation, the Mariposa Working Group was able to take control of Mariposa. The gang’s leader, alias Netkairo, seemingly rattled, tried at all costs to regain control of the botnet. As I mentioned before, to connect to the Mariposa C&C servers the criminals used anonymous VPN services to cover their tracks, but on one occasion, when trying to gain control of the botnet, Netkairo made a fatal error: he connected directly from his home computer instead of using the VPN. Netkairo finally regained control of Mariposa and launched a denial of service attack against Defence Intelligence using all the bots in his control. This attack seriously impacted an ISP, leaving numerous clients without an Internet connection for several hours, including several Canadian universities and government institutions.
The initial reports describe the group as not so technically sophisticated "normal people" making a lot of money through cybercrime. A logical question emerges - how is it possible that a group of "normal people" can build such a massive botnet? By outsourcing.
- Go through related posts: Malware Infected Hosts as Stepping Stones; The Cost of Anonymizing a Cybercriminal's Internet Activities; The Cost of Anonymizing a Cybercriminal's Internet Activities - Part Two; Zeus Crimeware as a Service Going Mainstream; Managed Polymorphic Script Obfuscation Services
The name Mariposa actually means butterfly, which is the original name of a commercially distributed DIY malware kit, sold online for 800/1000 EUR, unless of course the arrested botnet masters weren't using a pirated version, which is ironically, a common practice within the cybercrime ecosystem these days. What's particularly interesting about the malware was the fact that it was using its own UDP-based protocol for communication, which according to the original author was developed with stealthiness in mind since UDP connections are rarely logged.
Moreover, the bot has typical for modern malware releases anti-debugging features, as well as built-in DDoS functionality relying on TCP and UDP flood tactics. The three main propagation vectors include MSN, removable media, and through P2P, targeting the following networks - Ares, Bearshare, Imesh, Shareaza, Kazaa, Dcplusplus, Emule, Emuleplus, Limewire.
The Mariposa botnet is the tip of iceberg in respect to DIY botnets (Research: Small DIY botnets prevalent in enterprise networks; Inside the botnets that never make the news - A Gallery) aggregated using commercially, or freely available malware kits.
What this incident proves is that not only is cybercrime becoming easier to outsource in 2010, but also, that even inexperienced people can quickly gain access to capabilities once reserved for sophisticated attackers.