Profile of a failed Anonymous attack

Data-protection firm Imperva has undertaken an analysis of an Anonymous attack, claiming that it was able to witness a failed 25-day assault by the group and use its surveillance to map out Anonymous' attack methods.
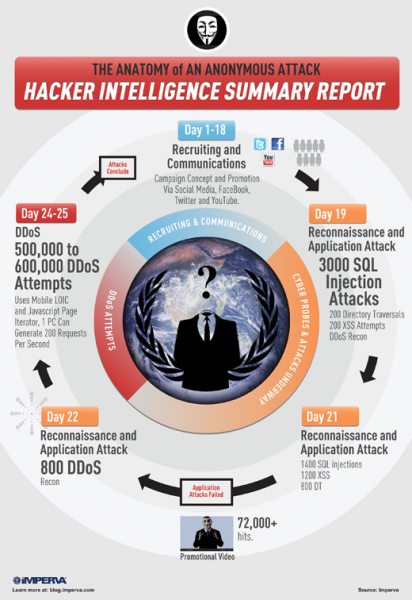
The report (PDF) covers the three phases that it believes Anonymous uses over its 25-day hacking period, as well as the expected structure of the group, the tools that Anonymous members are suspected of using and the techniques used in the attack.
According to Imperva, the first phase of this attack was to begin recruitment and communications. In the attack, Anonymous uploaded a video to YouTube and used Facebook and Twitter to further promote it.
"This is really the essence of all hacktivism campaigns," the report said. "The raison d'être of hacktivism is to attract attention to a cause, so this phase is critical."
Imperva said that Twitter and Facebook were used to bring attention to the cause, and the video was used to rationalize the attack. Promotional material was also used to set the date and convey target details for a future distributed denial-of-service (DDoS) attack. This communication phase lasted about 18 days.
This infographic shows the profile of an Anonymous attack (Credit: Imperva)
The second phase of the operation was a quick reconnaissance and application attack, aimed at surveying the target's state of security and identifying any vulnerabilities ahead of the scheduled attack that might aid in increasing the effectiveness of an attack.
Imperva's analysis of the attackers indicates that Anonymous had knowledge of hacking tools, used anonymity services to hide its members' tracks and kept a low profile to avoid being detected. According to Imperva's report, a small group of attackers of no more than 10 to 15 individuals scanned the target for web-application vulnerabilities, such as cross-site scripting, SQL injection and directory-traversal vulnerabilities, but they were unable to identify any opportunities for a more effective attack.
By examining the victim's firewall logs, Imperva identified that the attackers used at least three off-the-shelf products rather than software specifically created for the attack. These products were Havij, an automated SQL-injection tool; Acunetix Scanner, an automated scanner that was used to look for remote file-inclusion vulnerabilities; and Nikto Scanner, which looks for outdated server software and tests for dangerous scripts.
"Only when failing to find such vulnerabilities, the attackers resorted to searching a resource suitable for DDoS. Such resources involve actions which are time and resource consuming, and might lead to exhaustion of the server resources. Eventually, attackers spotted a specific URL that was later used in the attack itself," the report said.
This URL resulted in the server fetching data from a database, which takes up more resources than a regular web-page request and could potentially be used to deny services. By this stage, over 72,000 hits had been registered on the promotional video released as part of the communications phase.
In the final phase of the operation — the scheduled attack — those participating in the attack visited a website created by Anonymous, which contained JavaScript code intended to loop for as long as the page was open in the user's browser. Within the looping code was a request to the victim's site, pre-crafted to attack the specific URL that Anonymous had identified previously.
Imperva said that since the code was written in JavaScript, any device with a browser could be used to launch the attack. This included mobile devices, of which Imperva saw evidence. Imperva estimated that a regular computer would be capable of achieving 200 requests for information per second.
Although the core team behind the attack was relatively careful in hiding its tracks, Imperva noted that a majority of the actual attackers didn't bother or didn't know how to disguise their identities.
Although these combined efforts was not enough to bring down the victim, Imperva offered advice for anyone who thinks that they might be a target. It recommends monitoring social media, due to the fact that groups like Anonymous often announce their targets before attacking. It also believes that a DDoS attack actually represents the hacker's last resort when they're unable to identify vulnerabilities during the reconnaissance phase.
This story was originally posted on ZDNet Australia.