Puush calls for password change after malware hit

Users of the Puush screenshot-sharing platform are being told to change any passwords stored on their PCs or browsers after the service was hit by malware.
At around 9am AEDT on Monday morning, the Puush Twitter feed erupted with news that users of the platform, which is available as an app for Windows, OS X, and iOS, had been sent possible malware disguised as a Puush update.
"We've received reports of possible malware being sent in disguise of a Puush update. For now, we suggest closing the Puush app (Windows only)," the company said on its Twitter page early on Monday morning.Within the hour, Puush had told users with Windows to run a virus scan on their PCs, and uninstall the Windows Puush client.
"In the meantime you can check your PC for push.daemon.exe and remove it. It seems to sit in AppData/Roaming/puush/," it tweeted.
Latest Australian news
Although Puush said that passwords were not compromised, as it stores passwords "salted and hashed using bcrypt", it later tweeted that it had received unconfirmed reports from a person analysing the malware that it may be attempting to obtain passwords from users' local systems.
"We therefore highly recommend changing any saved passwords on your system (mail clients/Chrome or Firefox sessions) after patching," Puush said.
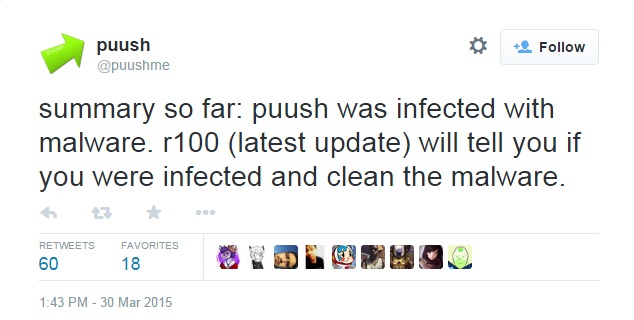
Within two hours of first notifying users of the potential malware threat, Puush took down its service, released a new Windows patch, and eventually restored service, telling users that it should be safe to reinstall the software.
Puush, which is developed by Western Australia-based developer Dean Herbert, has since told users that the time during which infected updates were sent out, was from 6.51pm to 9.41pm UTC on the evening of March 29.
Puush subsequently tweeted that while it recommends users change their passwords, its sandboxed investigations had shown no sign of data, such as passwords, being transmitted.