Pwn2Own 2012: IE 9 hacked with two 0day vulnerabilities

VANCOUVER -- Microsoft's Internet Explorer 9 browser has fallen.
A team of French researchers exploited two different IE zero-day flaws to break into a fully patched Windows 7 SP1 machine and take an almost unassailable lead in this year's CanSecWest Pwn2Own competition.
The hacking team, from French security research outfit VUPEN, used an unpatched heap overflow bug to bypass DEP and ASLR and a separate memory corruption flaw to break out of the browser's Protected Mode sandbox.
The code execution attack, which required no user action beyond browsing to a rigged web site, also works on Internet Explorer v10 (consumer preview) running on Windows 8.
VUPEN co-founder Chaouki Bekrar, who led his team's work hacking into two major browsers -- Chrome and IE9 -- said the Internet Explorer flaws went undetected for a very long time.
"This goes all the way back to IE 6. It will work on IE 6 all the way to IE 10 on Windows 8," Bekrar said.
If they win the Pwn2Own challenge, which is likely based on their work popping Chrome and writing on-the-spot exploits for previously patched vulnerabilities, VUPEN will give up the rights to only one of the IE bugs.
"We're only giving up the heap overflow. We will keep the Protected Mode bypass private for our customers," Bekrar said.
He said VUPEN used two researchers working for six weeks on a full-time basis to craft the IE 9 exploit for Pwn2Own.
"This one was difficult. When you have to combine many vulnerabilities and bypass all these protections, it takes a longer time," he said, noting that his team came to Vancouver with zero-day flaws for every browser on every operating system.
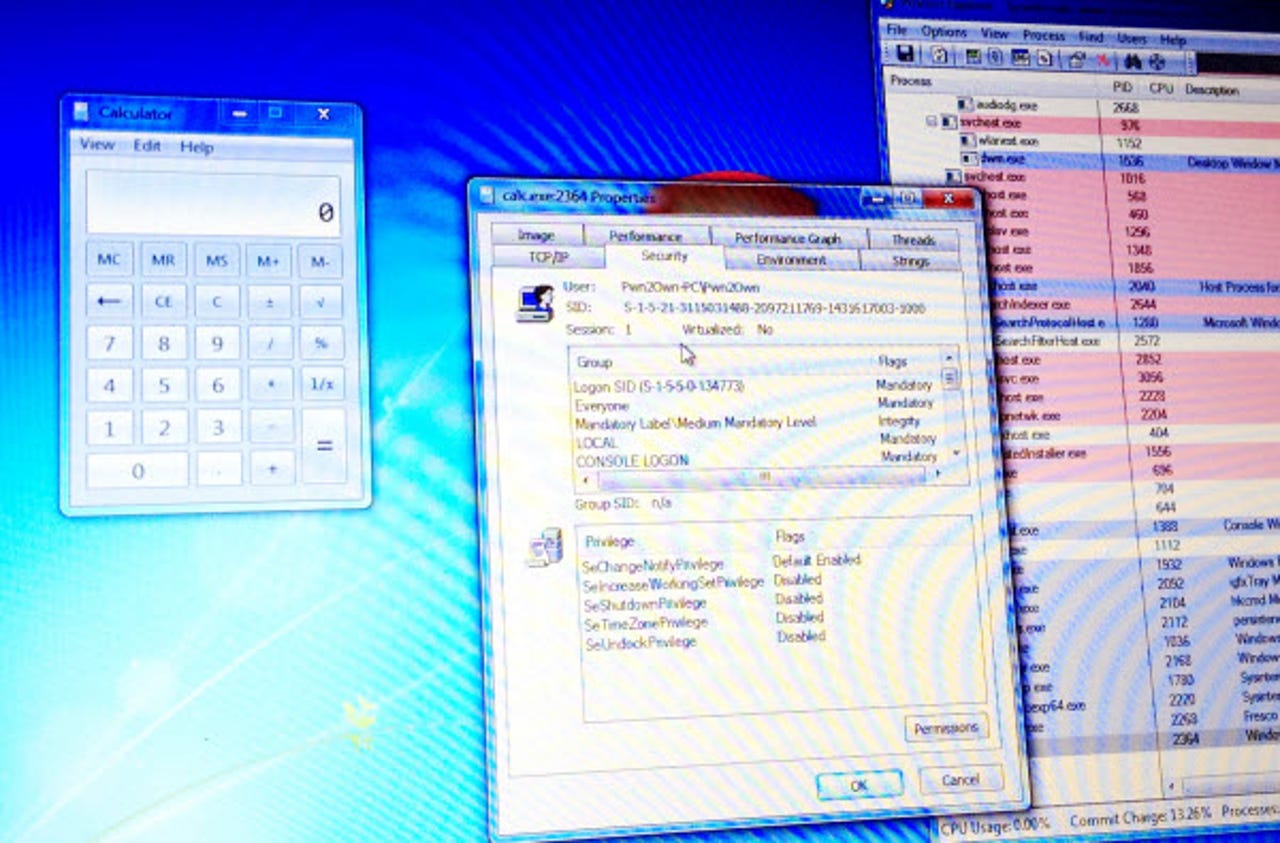
Explaining the two-stage IE 9 attack, Bekrar said the first vulnerability was used to execute first-stage shellcode. "In this first-stage shellcode, we included a second exploit. [Then] we move the code execution from low integrity level to medium integrity level and bypass the Protected Mode sandbox."
Bekrar said his team has found "many vulnerabilities in Protected Mode" that are all unpatched. "We used a memory corruption vulnerability in the way Protected Mode is implemented but we have found many more vulnerabilities there."
He said VUPEN's motive for participating in Pwn2Own was to prove that a dedicated hacker can bypass all security protections, even on the newest operating systems. "We want to show that we can."
Bekrar said his team has started work analyzing the IE 10 consumer preview and has found it much more difficult to exploit, due to new mitigations. Microsoft has added protections to use-after-free and memory leaks but these mitigations come with a price.
"Exploitation is much harder and more time consuming," Bekrar said. "But, they make the prices for vulnerabilities and exploits go higher."
Representatives from Microsoft's security team were on hand to witness the IE 9 hack and they plan to activate their response process once they receive the vulnerability information from the Pwn2Own organizers.
ALSO SEE: