Ransomware is working, and the cybercrooks know it

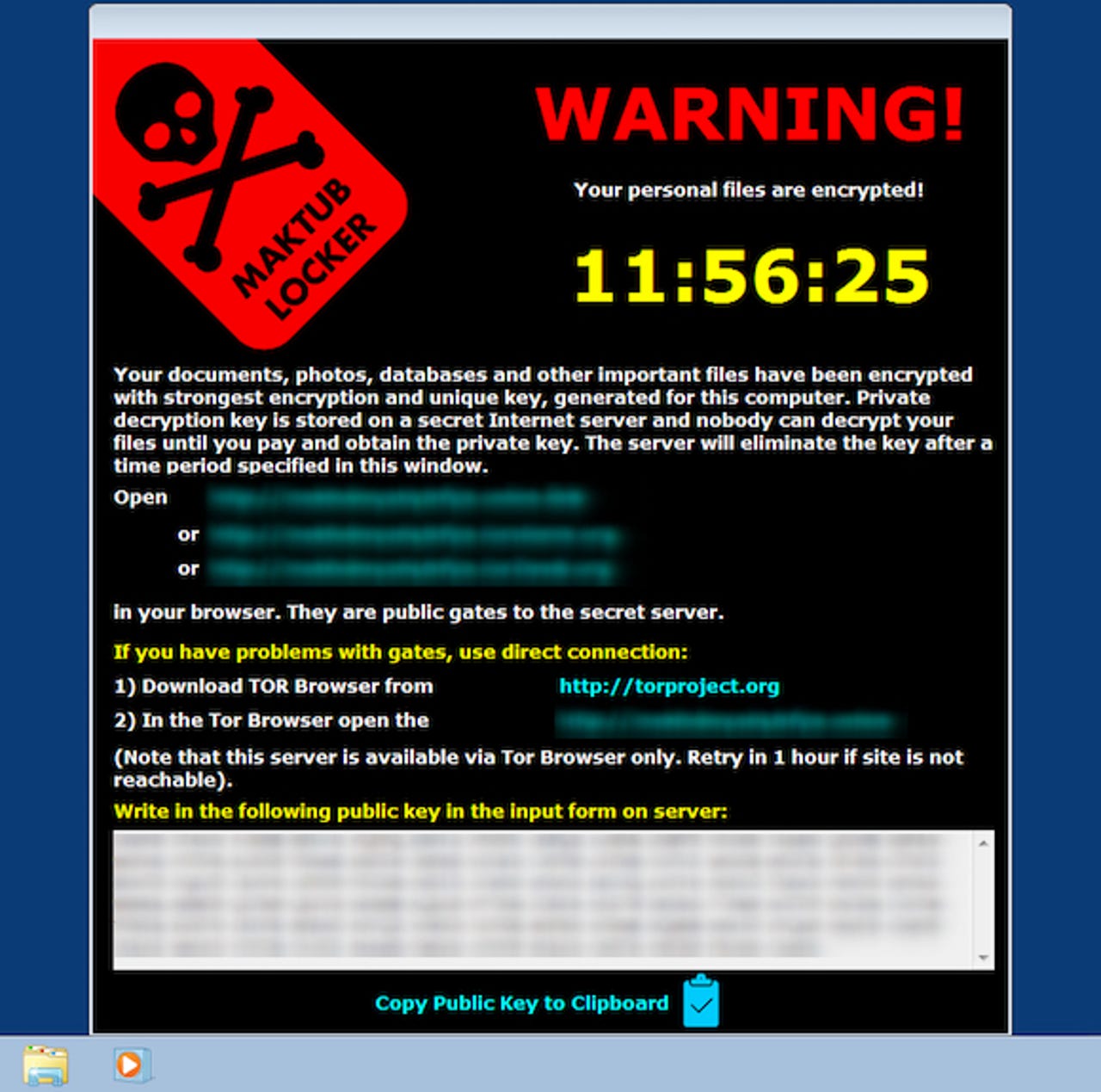
Ransomware is becoming a bigger and bigger threat.
The number of internet domains serving up ransomware has risen massively in just the space of three months, as cybercriminals look to cash in.
Sites designed to host malware, exploit kits, phishing scams, and other threats have also reached their highest-ever level, according to security researchers at Infoblox.
In raw numbers, exploit kits remain the biggest security threat, accounting for just over 50 percent of the index. As in past quarters, Angler remains the top piece of ransomware, but a new contender has emerged from far back in the pack: observations of Neutrino have grown by 300 percent, the researchers said.
"Again in simple terms: Ransomware is working," the report said.
"What has changed over the past quarter or two is a shift from small-dollar heists targeting consumers to larger, more profitable attacks on commercial entities. And as news of this success has spread, certainly through underground networks and ironically through general media coverage of the danger, cybercriminals have apparently taken notice," the report added.
One high-profile incident during the period covered by the report was the cyberattack against a Hollywood hospital, which saw 'Locky' malware knock its systems offline for days. Those behind the attack then made off with $17,000 in Bitcoin in exchange for unlocking the infected systems.
Indeed, FBI figures suggest that ransomware victims reported costs of $209m in the first quarter of 2016, compared to $24m for all of 2015, demonstrating that the threat is very much on the rise.
When other cyber fraudsters see that this type of attack is working, they take notice, hence the rapid rise in malicious domains serving up ransomware - each one a potential pot of gold for the owner. According to Infoblox, this threat will remain an issue for some time.
"Unless and until companies figure out how to guard against ransomware - and certainly not reward the attack - we expect it to continue its successful run," warns the report.