Ransomware now locks your smart TV - and then demands Apple iTunes gifts

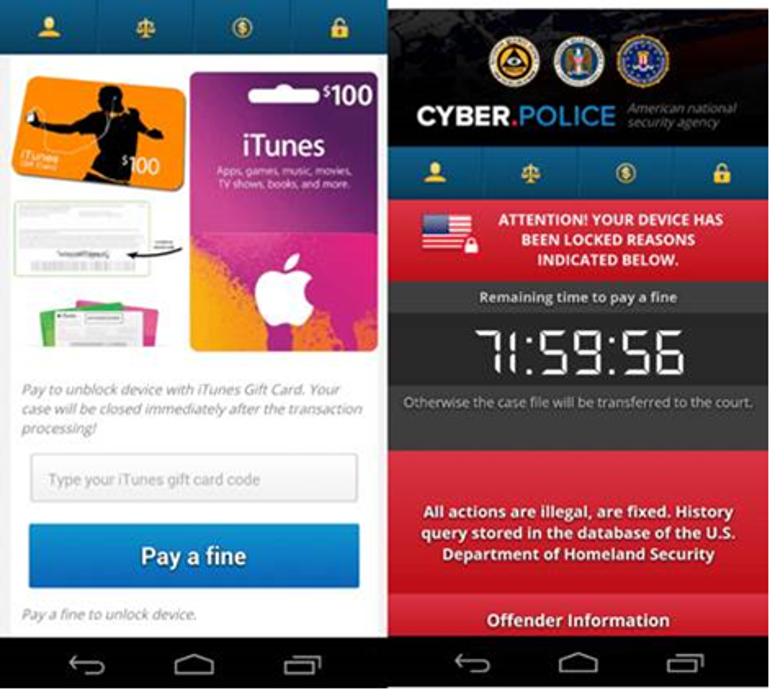
The malware will lock a device's screen and then displays a ransom message in the local language, purportedly from US Cyber Police or another law-enforcement agency.
Malware researchers at Trend Micro have discovered a new variant of ransomware that locks up Android smartphones and Android TVs.
FLocker, which is short for Frantic Locker, has posed a threat to Android smartphones since May 2015, but one version of several thousand variants has now gained the ability to infect smart TVs.
The malware will lock a device's screen and then displays a ransom message in the local language, purportedly from US Cyber Police or another law-enforcement agency.
Next, it demands $200 in iTunes gift cards to unlock the infected device. Trend Micro says the malware operates in the same way on Android smart TVs as it does on smartphones.
FLocker is configured to avoid devices in certain regions and will not lock a device if it detects a location in Kazakhstan, Azerbaijan, Bulgaria, Georgia, Hungary, Ukraine, Russia, Armenia, and Belarus.
If the malware is installed on devices outside these countries, it will wait for 30 minutes before requesting device admin privileges. If the user rejects the request, the malware displays a fake system update screen.
Fortunately, this variant of malware does not encrypt files on an infected device. Nonetheless, it will siphon off data from the device, including contacts, the phone number, information about the device, and location.
It's not clear from Trend Micro's report how a smart TV would be infected, but the company notes that typically ransomware arrives via SMS or malicious links.
It is also possible for more technically-minded users to uninstall the ransomware after removing its device admin privileges.
"If an Android TV gets infected, we suggest that the user contacts the device vendor for solution at first. Another way of removing the malware is possible if the user can enable ADB debugging," Trend Micro explains.
"Users can connect their device with a PC and launch the ADB shell and execute the command 'PM clear %pkg%'. This kills the ransomware process and unlocks the screen. Users can then deactivate the device admin privilege granted to the application and uninstall the app."
It's not the first piece of malware for smart TVs, but acts as a reminder that attackers behind the nastier crypto ransomware can expand from PCs and smartphones to other connected smart devices in the home.
Because smart TVs run a browser, they can also become inadvertent targets of malware designed for PCs, as recent research by Kaspersky has highlighted.