Ransomware: Why it's a really big problem for small businesses

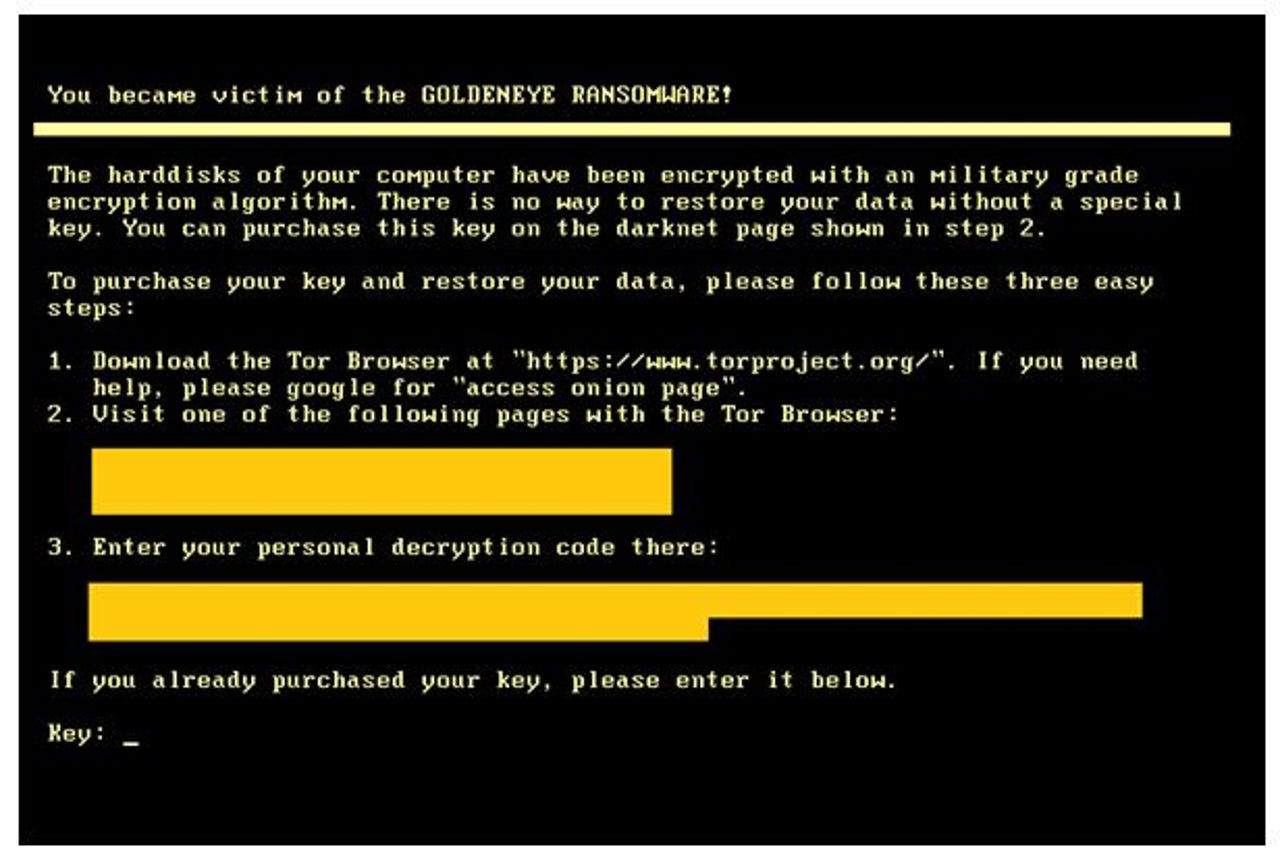
Ransomware can easily destroy a business.
The ransomware threat has massively exploded in the last year, growing from an inconvenience to something which could potentially put you out of business.
Police encourage organisations which fall victim to this file-encrypting malicious software not to give into the demands of cybercriminals, but many will -- if reluctantly-- pay the Bitcoin ransom demanded in order to restore their networks, and this proves lucrative for those operating the schemes.
One of the most high-profile instances of a ransomware infection came when the Hollywood Presbyterian Medical Center become infected with Locky, taking systems offline and causing disruptions to patient treatment until the hospital paid hackers a $17,000 ransom in order to restore its network.
With ransomware robbing victims of an estimated $1 billion in 2016, it might be easy to think that culprits are making their illicit fortunes by targeting big businesses.
But they're not the only targets. Small and medium-sized businesses are also vulnerable to these criminal schemes, even if many still underestimate the potential threat of ransomware, falsely believing that they're too small to be targeted.
Because these smaller businesses have less to spend on cybersecurity software and staff training, it means that if anything they're more likely to be targeted, as nefarious cyberattackers view them as easy prey.
"These are businesses which typically can't afford the protections that they need when this happens. So the business has an awkward decision to make: do I pay the ransom, or do I pay ten times the amount of the ransom to protect against the threat?" says Graeme Newman, chief innovation officer at CFC Underwriting, a specialist provider of cyber-insurance.
When attacking small businesses, cybercriminals will demand smaller ransoms than they would from a multinational corporation, but given how any amount of network down time is damaging for smaller organisations, they're likely to pay up -- and fast.
"Many of these businesses don't have the appropriate technology in place to detect ransomware infections. Further, they don't have a full backup system in place, which typically leads to businesses paying the ransom to recover their data." says Mohamad Ali, CEO of security company Carbonite.
It's this willingness to pay up which makes smaller businesses such an attractive target. While hackers might not pocket the large sums they'd receive for successfully holding a large organisation hostage, infecting an SME is almost a guaranteed payday -- and multiple attacks on smaller firms could add up to a large payoff.
"Cybercriminals do not discriminate -- they will go after any company of any size they feel they can infiltrate. The bottom line is all businesses have data worth protecting, so all businesses need to be proactive and prepare for worst case scenarios," says Ali.
So what is the worst case scenario? It could be the end of your business. Either you refuse to pay the cybercriminals a ransom and your data is destroyed, or you pay the ransom, only to find that they take your money and run, and never return your data.
Newman said that two recent attacks had targeted a logistics firm and an IT provider.
"The logistics company didn't pay the ransom, which led to all of their data, including their backups, being destroyed. It has caused massive business interruption as the company now has to rebuild from scratch," he said.
"The IT provider also didn't pay the ransom, which has led to valuable data being lost. In their case, it has let to reputational harm as well. As an IT provider, they obviously want to be seen as reliable and secure," Newman added.
In both instances, the companies had cyber-insurance which helped to cover the damage costs and keep the businesses afloat -- but it isn't a 'get out of jail free' card.
"While cyber-insurance can be helpful to cover a business liability for an attack, it is not a solution for all consequences and won't help return your stolen data," says Ali. "Cyber insurance cannot negate any negative publicity or negative brand reputation that could come as a result of such breach."
Even the likes of basic cybersecurity training and teaching employees what to look for in a malicious phishing email designed to drop ransomware can hugely decrease the likelihood of falling victim to an attack.
"In the age of digital services, it is vital that SMEs find the best ways to keep the hackers at bay," says David Evans, director of policy at BCS, the Chartered Institute for IT.
"The IT team may well set out the security policies, but it's really important that everyone plays their role in implementing these simple measures."
Security basics can include: teaching staff to think before they click on emails, deploying firewalls, undertaking penetration testing, and the IT team ensuring that all networks and systems are updated. These are just some of the precautions smaller businesses can take against falling victim to attacks.
However, the nature of attackers means they're persistent and they'll strive to find a way to break into a network. So what should a smaller business do if they find their systems locked with ransomware?
"If you have a full backup system, the best course of action is to delete all infected files, remove the computer virus, and download clean versions of the encrypted files from backup," says Ali.
"Other options include attempting to remove the malware by restoring your system to a time before the infection. If that doesn't work, you can attempt to clean your system using a virus scanner from a USB drive or other bootable disk."
Unfortunately, there are plenty of SMEs who won't back up their systems, or won't have the capability to restore the system to a previous date. And that's why hackers will continue to target them with ransomware; it might be small fry, but it's easy money.
Read more on cybersecurity
- Ransomware: Should you pay up?
- Ransomware: How to defend yourself against it [CNET]
- Hit by ransomware? No More Ransom portal adds 32 more free decryption tools to help you
- How one of the biggest data thefts in US history could have been stopped by basic security
- New ransomware could poison your town's water supply if you don't pay up [TechRepublic]