Religious-themed Madi malware hitting select targets in Iran, Israel

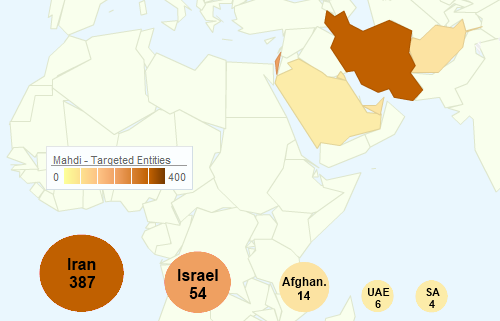
A sustained cyber-surveillance operation has netted more than 800 victims at government entities, financial institutions, engineering and critical infrastructure operations in the Middle East, according to security researchers tracking the malware.
Security researchers from Kaspersky Lab and Seculert (see important disclosure) warn that a Trojan called Madi is being delivered to select targets in Iran, Israel and surrounding countries with a specific mission: monitor communications on infected machines, hijack documents and upload sensitive files to remote servers controlled by the attackers.
Madi is delivered via Microsoft Office attachments (PowerPoint slideshows) and relies heavily on social engineering tricks to infect the target machine. Once opened, the suspicious file walks the viewer through a series of calm, religious themed, serene wilderness, and tropical images, confusing the user into running the payload, according to a Kaspersky blog post.
Once a victim is infected with the malware, the attackers can:
- Log keystrokes.
- Capture screenshots at specified intervals.
- Capture screenshots capture at specified intervals, initiated exclusively by a communications-related event. The event may be that the victim is interacting with webmail, an IM client or social networking site. These triggering sites include Gmail, Hotmail, Yahoo! Mail, ICQ, Skype, google+, Facebook and more.
- Update the backdoor.
- Record audio as .WAV file and save for upload.
- Retrieve any combination of 27 different types of data files.
- Retrieve disk structures.
- Delete and bind.
The campaign, which has been ongoing for at least eight months, is being managed by people who are fluent in Farsi, according to Seculert's Aviv Raff. In a separate blog post, Raff said the attackers originally used a command-and-control server located in Tehran, Iran before moving operations to servers in Canada.
"It is still unclear whether this is a state-sponsored attack or not. The targeted organizations seem to be spread between members of the attacking group by giving each victim machine a specific prefix name, meaning that this operation might require a large investment and financial backing," Raff said.
Kaspersky's research team reports that the malware is very rudimentary and basic in nature but makes the point that this is hardly relevant because of the success of the operation to target and infect high-value individuals.