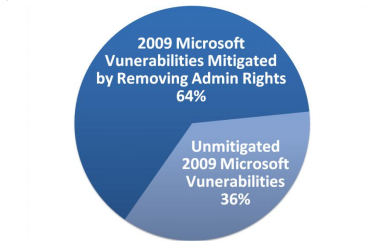
Report: 64% of all Microsoft vulnerabilities for 2009 mitigated by Least Privilege accounts
By collecting data from Microsoft's Security Bulletins published throughout the year, and identifying the vulnerabilities who would have been mitigated by users whose accounts are configured to have fewer user rights on the system, BeyondTrust's quantitative report message is simple - get back to the basics.
Key summary points on the percentage of flaws mitigated:
- 90% of Critical Windows 7 operating system vulnerabilities are mitigated by having users log in as standard users
- 100% of Microsoft Office vulnerabilities reported in 2009
- 94% of Internet Explorer and 100% of IE 8 vulnerabilities reported in 2009
- 64% of all Microsoft vulnerabilities reported in 2009
- 87% of vulnerabilities categorized as Remote Code Execution vulnerabilities are mitigated by removing administrator rights
The window of opportunity -- 21 days in the case of this out-of-band IE patch -- often left wide open for too long, prompts the most basic question - what should a company or an end user do by the time a patch is available, next to logically switching to an alternative browser? Get back to the basics, and assume the worst in an attempt to mitigate the highest percentage of risk posed by the situation.
- Go through related posts: Secunia: Average insecure program per PC rate remains high; Research: 80% of Web users running unpatched versions of Flash/Acrobat; Report: 48% of 22 million scanned computers infected with malware; Report: Malicious PDF files comprised 80 percent of all exploits for 2009
Calls for "dropping your rights" have been made for years. And whereas the process has become easier to
Prevention is better than the cure, even from a cost-effective perspective. There's also no shortage of alternative solutions, such as for instance sandboxing your favorite browser -- Sandboxie is free for personal use -- in order to ensure that what happens in the sandbox, stays in the sandbox. A similar advice was given by the American Bankers’ Association (ABA) last month.
Moreover, in respect to BeyondTrust's report, there are two fundamental points that the report isn't emphasizing on:
- Cybercrime is not driven by the use of zero day flaws, but by the millions of people using the Internet with outdated software - It's a simple fact that has so far contributed to the rise and rise of some of the most prolific botnets, and outdated flaws within popular applications remain the main vehicle for Zeus crimeware infections. Naturally, there are campaigns that exclusively rely on recently published flaws, but the window of opportunity offered by those would be closed sooner than the one of all the outdated applications running on the same PC, combined. It's the cybercriminal's mentality of traffic optimization for malicious purposes, (See example: Money Mule Recruitment Campaign Serving Adobe/Client-Side Exploits), that offers the highest probability of infection.
- Microsoft OS/software specific vulnerabilities are only a part of the drive-by exploits cocktail served by web malware exploitation kits - You would be surprised to know how many people are so obsessed with "Patch Tuesday" that they exclude the decent number of outdated browser plugins and third-party software installed on their PCs. The result? A false feeling of security, which combined with an outdated situational awareness on how modern web malware exploitation kits work, leads to a successful drive-by attack. It shouldn't come to as a surprise that, not only did malicious PDF files comprise 80 percent of all exploits for 2009, but also, the use of Microsoft Office files for targeted attacks is declining. Two years ago, Microsoft in fact confirmed this trend - Microsoft: Third party apps killing our security.
In terms of closing the window of opportunity that malicious attackers systematically exploit until a patch is released, the best advice is the most pragmatic one. And in this case, it's the easiest one to implement - remove admin rights, sandbox your browser, and take care of all those third-party apps and browser plugins.