Report: Large US bank hit by 20 different crimeware families
For years, cybercriminals have been systematically undermining the effectiveness of antivirus software, successfully reaching a "malicious economies of scale" stage in their ambitions to steal money from affected parties across the globe.
One of the major shifts in their strategy over the past couple of years, is the professionalism applied to malicious campaigns targeting the weakest link in the entire trust chain - a bank's customers. Instead of trying to directly compromise the infrastructure of a specific financial institution and steal money from the inside, cybercriminals have been busy developing advanced and efficient ways to steal these very same money from a bank's customers.
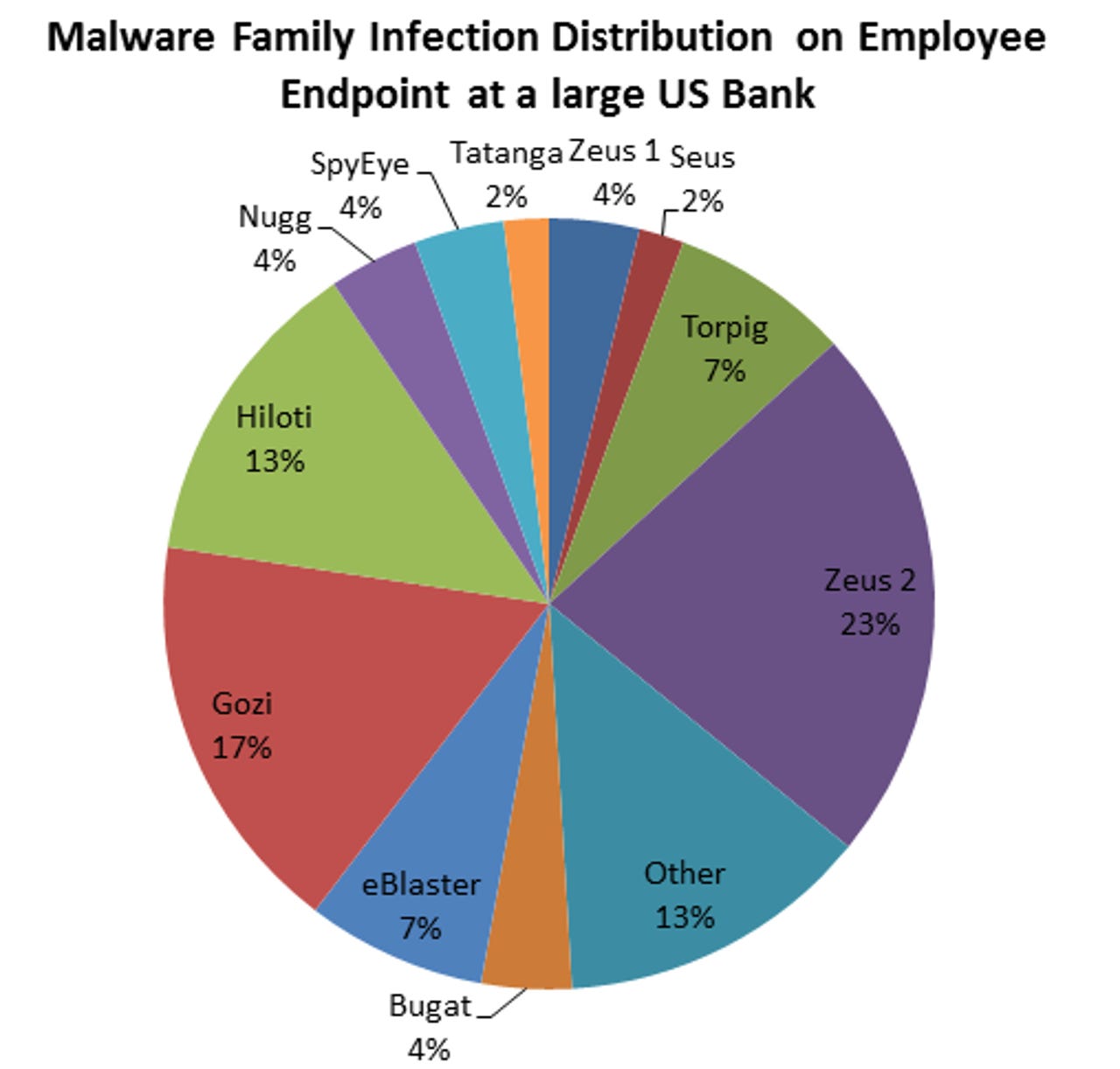
In 2012, are cybercriminals still busy coming up with ways to directly compromise a financial institution's infrastructure? It appears so, at least according to recently released Trusteer advisory, indicating that during their research they found over 20 different crimeware families on a single host within a large U.S bank during a period of 12 months.
Were these targeted attacks, or good old fashioned massive spamvertised campaigns? Based on the fact that the host was infected with such a wide variety of crimeware, it appears that the host has been compromised by multiple cybercriminals/gangs of cybercriminals, who managed to trick the user behind this host, over and over again, resulting in the messy situation.
Although enterprises get compromised on a daily basis, Trusteer's findings are more of a fad, then a trend. How come? Pretty simple, its easier to target a bank's customer, compared to attempting to somehow compromise the bank's infrastructure, and cybercriminals know that already, hence their malicious campaigns orbit around this fact and will continue to do so.
What do you think? Will cybercriminals attempt more sophisticated attacks against the infrastructure of financial institutions, compared to targeting the weakest link in the trust process - the bank's customers?
TalkBack.
Find out more about Dancho Danchev at his LinkedIn profile.