Report: Malware capital of the world is Shaoxing, China

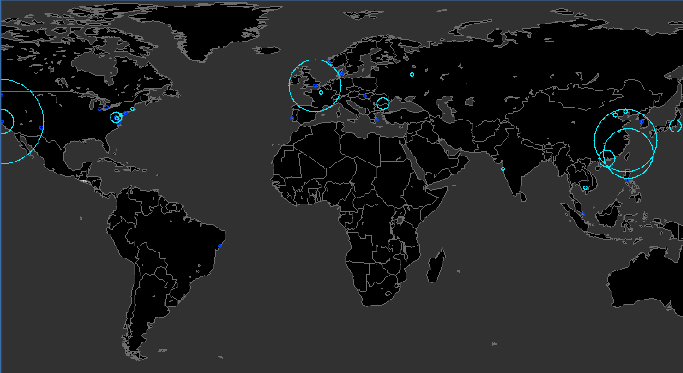
Computer security firm Symantec announced on Monday that Shaoxing, China was malware capital of the world last month.
According to the company's research, nearly 30 percent of targeted malware attacks came from China -- with 21.3 percent from Shaoxing alone. Runner-up to the crown was Taipei, at 16.5 percent, with London taking the bronze at 14.8 percent.
On a national scale, China trumped all, followed by Romania, with 21.1 percent of attempted attacks, and the United States, with 13.8 percent.
There is lots of great data in this report. For example, the majority of targeted malware sent this month originated in the U.S. based on mail server location, at 36.6 percent. When arranged by sender location, however, the previously stated figures hold true.
"When considering the true location of the sender rather than the location of the email server, fewer attacks are actually sent from North America than it would at first seem," said Paul Wood, MessageLabs Intelligence Senior Analyst, in prepared remarks. "A large proportion of targeted attacks are sent from legitimate webmail accounts which are located in the U.S. and therefore, the IP address of the sending mail server is not a useful indicator of the true origin of the attack.
"Analysis of the sender's IP address, rather than the IP address of the email server reveals the true source of these targeted attacks."
More takeaways from the report:
- The most common file types attached to all malicious emails were .XLS and .DOC.
- The most dangerous file type was encrypted .RAR files.
- .XLS and .DOC each accounted for 15.4 percent of file attachments.
- The top four most common file types (.XLS, .DOC, .ZIP and .PDF) accounted for 50 percent of attached files.
- Despite being just 0.32 percent of attached files, .RAR files were compromised 96.8 percent of the time.
- .EXE files were compromised just 15 percent of the time.
The report also took a more global tack:
- At 95.7 percent, Hungary was the most spammed country in March 2010.
- At 1 in 90.9 emails, Taiwan was the most targeted country for email-borne malware in March.
- At 1 in 254.8 e-mails, Britain was the most active country for phishing attacks in March.
Symantec found that the Rustock botnet sent considerably more spam using Transport Layer Security, or TLS, at 77 percent during March.
Spam using TLS accounted for approximately 20 percent of all spam in March, according to the report.
More highlights for March 2010:
- Spam: In March 2010, the global ratio of spam in email traffic from new and previously unknown bad sources was 90.7 percent, an increase of 1.5 percentage points, month-over-month.
- Viruses: The global ratio of email-borne viruses in email traffic from new and previously unknown bad sources was one in 358.3 emails, a decrease of 0.05 percentage points MoM.
- Phishing: Phishing activity was 1 in 513.7 emails, a decrease of 0.02 percentage points MoM. But phishing increased, relatively speaking, compared to other email-borne threats.
- Web security: 14.9 percent of all web-based malware intercepted was new in March, an increase of 1.6 percentage points MoM.
And finally, some industry trends for March 2010:
- Engineering was the most spammed industry sector, followed by education, pharmaceuticals, IT services, retail, government and finance.
- The public sector was the most targeted for malware.
You can find the full report here (.pdf).