Report: third party programs rather than Microsoft programs responsible for most vulnerabilities
According to Secunia's recently released "Yearly Vulnerability Research Report", third party applications rather than Microsoft programs are responsible for the majority of vulnerabilities.
Moreover, the report further confirms a popular myth which I already debunked in my "Seven myths about zero day vulnerabilities debunked" post, namely that patched vulnerabilities remain the the primary exploitation vector that malicious attackers take advantage of.
More from the report:
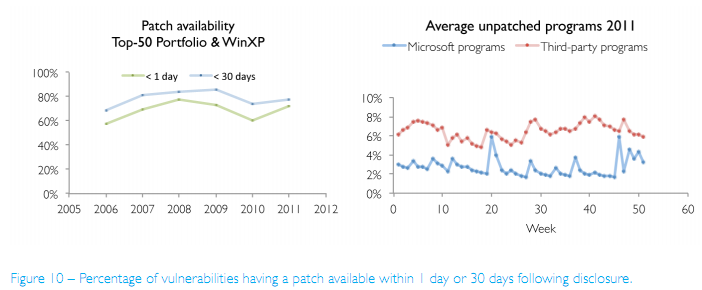
For all Secunia Advisories affecting a typical end-point in 2011, 72% had a patch available within one day of the disclosure of the vulnerability, and 77% of the advisories had a patch available within 30 days of disclosure.
This data indicates that there is limited room for 0-day exploits. The 28% of the advisories that had no patch available on the day of disclosure indicates an upperbound of potential for 0-day exploit availability. Microsoft even reports that less than 1% of the attacks in the first half of 2011 were attributed to 0-day exploits. Therefore, the mere possibility of 0-day exploits, a force majeure, does not justify ignoring 72% of the cases where effective remediation is possible and at users’ fingertips.Thus, organisations can hardly hide behind the threat of 0-days when a solution is available for 72% of vulnerabilities.
Averaged over a year, 2.7% of the Microsoft programs are found insecure compared to 6.5% of the third-party programs. Thus, on average,more than twice as many third-party programs are found unpatched than Microsoft programs.
What does this mean? It means that end and corporate users continue utilizing the potential of the Internet while using outdated third-party applications and browser plugins. In the past, Secunia has released detailed statistics on the average number of insecure applications per country, with Cuba and North America topping the chart.
End users are advised to ensure that they're using the latest versions of their third-party software, and browser plugins.
Related posts: