Researcher discovers Nokia S40 security vulnerabilities, demands 20,000 euros to release details
Will disclose Nokia s40 security vulnerabilities for money? Part of Security Exploration's research program, Adam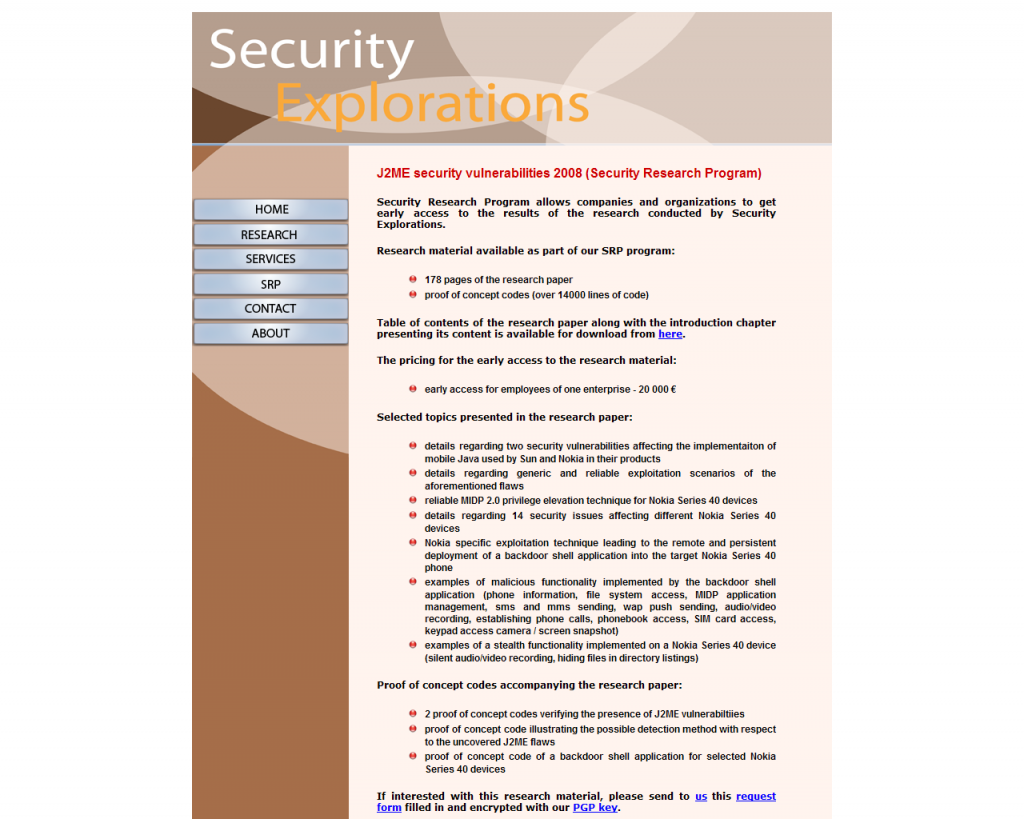
"The initial motive for this work was to verify security of proprietary Nokia devices and its Series 40 Platform in particular. For many years, no major threat had been uncovered for this family of Nokia devices. All of that regardless of increasing devices complexity and their very closed nature. Unfortunately, in a security research world, closed source/platform and complexity never go along with security. Thus, the motive for the research.
This paper presents the results of the research conducted from Feb 2008 till Jul 2008 in the area of security of Nokia Series 40 Platform devices and Java 2 Micro Edition (J2ME). It also contains information pertaining to security vulnerabilities discovered during the research process as well as detailed discussion of universal and reliable exploitation techniques for the aforementioned family of Nokia devices."
Will vendors purchase the research, ignore it entirely, or try to reverse engineer his claims based on the already provided details in order not to pay?
While I'm fairly certain that they'll try to reverse engineer his claims in order not to entice other researchers into holding
This very same situation happened last year, when Vulnerability Discovery and Analysis (VDA) Labs demanded $5000 for a security vulnerability that they found in LinkedIn's toolbar, an offer that would have increased to $10,000 unless LinkedIn didn't pay the price based on the deadline they set. Here's a sample of the letter :
"We've discovered an attack against the LinkedIn toolbar. If you are interested in the bug, we would like to give first right of refusal to purchase it. We'd also like to perform a more complete security audit of your products. We can help make the LinkedIn products more secure," DeMott stated in e-mail sent to LinkedIn on July 10, as viewed by CNET News.com.
The e-mail continues: "If you wouldn't like to buy it then we are happy to resell or release as a full disclosure to help prevent security issues arising on end users servers. We strongly believe in keeping users safe. We are unique in that we give vendors a first chance at the bugs we discover rather than selling to a third-party or releasing publicly. Please find the VDA Labs Value add document attached. If you'd like to buy the bug we will provide working attack code, so that you can verify the bug, before you send the check."
Being a hostage of someone else's research isn't a very comfortable situation, especially when millions of mobile device users' security could be at stake. But with mobile device vendors allocating bigger budgets for marketing than R&D in security, and not even raising awareness on basic threats thereby contributing to insecure habits that would become the cornerstone for efficient exploitation of mobile devices in the very near future, perhaps this is a the wake up call they need to take seriously this time. Case in point - trivial security vulnerabilities in NFC mobile phones that could have been taken care of if usability was balanced with security, remain unpatched, some of them not even recognized as vulnerabilities yet.
The bottom line of this insecure by design mentality is an end user that's paying more attention to the quality of the camera of the device, and taking security as granted. However, once the trivial vulnerabilities start taking place in the moment when the user is actively using mobile banking, he'd be the first to blame the vendor for lack of security, forgetting that he accepted and got used to using an insecure device at the first place. So don't take security for granted.