Researchers demo wireless keyboard sniffer for Microsoft 27Mhz keyboards
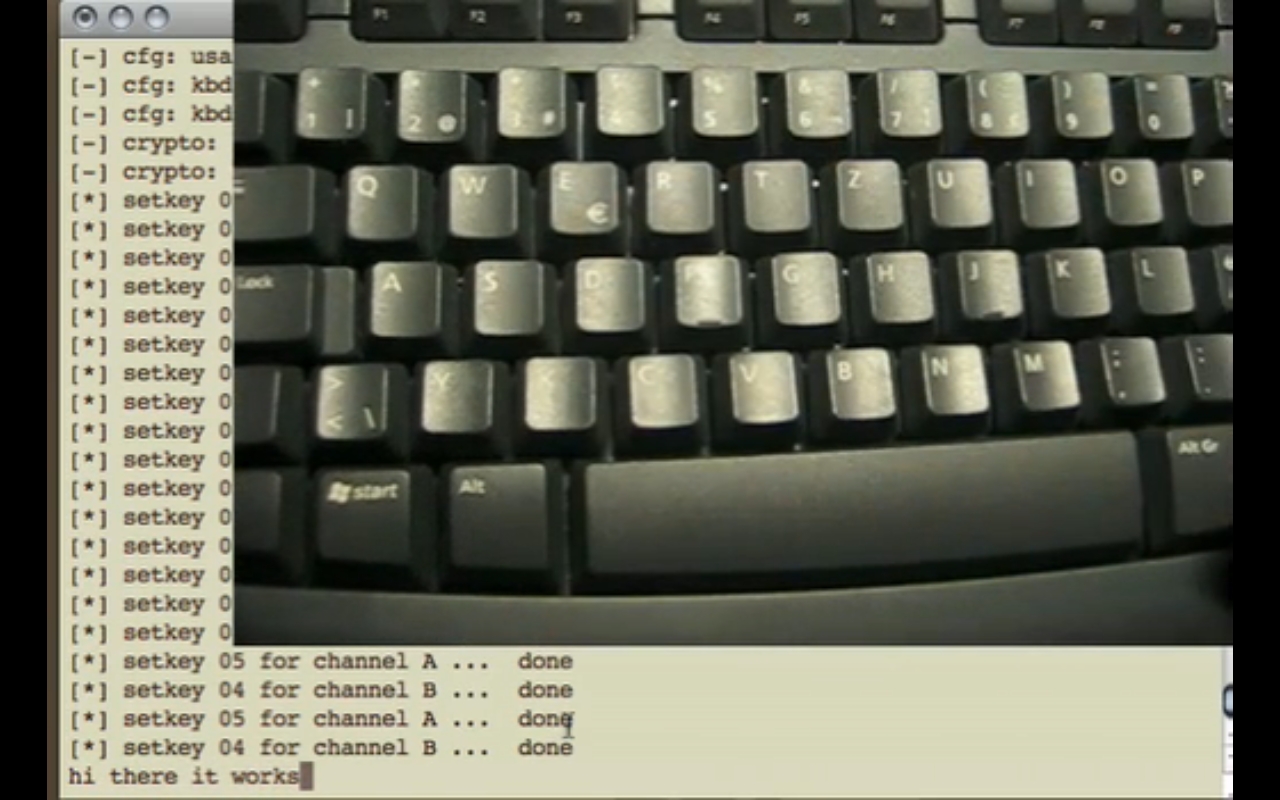
Their wartyping -- decoding signals from wireless keyboards -- proof of concept is based on a research paper published by the group one and a half years ago:
"Now 1.5 years after releasing our whitepaper "27Mhz Wireless Keyboard Analysis Report" about wireless keyboard insecurities, we are proud to present the universal wireless keyboard sniffer: Keykeriki. This opensource hardware and software project enables every person to verify the security level of their own keyboard transmissions, and/or demonstrate the sniffing attacks (for educational purpose only). The hardware itself is designed to be small and versatile, it can be extended to currently undetected/unknown keyboard traffic, and/or hardware extensions, for example, a repeating module or amplifier."
Moreover, the researchers aren't aware of any patching possibility to the affected 27Mhz keyboards, and point out that while Logitech's "Secure Connect" solution is in fact adding an additional layer of encryption, they intend to include decryption capability in future releases of Keykeriki, next to inspection of 2.4Ghz wireless devices and keystroke injection on the affected keyboards.