Researchers spot new Web malware exploitation kit
Over the past two years, the security industry witnessed the tremendous growth of web malware exploitation kit as efficient platforms for serving client-side exploits and malware to unaware end and corporate users.
The trend, largely driven by the professional work done on behalf of the cybercriminals behind these kits, is largely attributed to the standardized model behind the release of these kits. On a periodic basis, copycat cybercriminals will basically rebrand a well know web malware exploitation kit, introduce a new layout template, combined with a unique mix of exploits, and start advertising it within the cybercrime ecosystem.
On the other hand, sophisticated cybercriminals will do their best to stay beneath the radar of security researchers and security vendors, and will only serve a dedicated market segment within the underground economy.
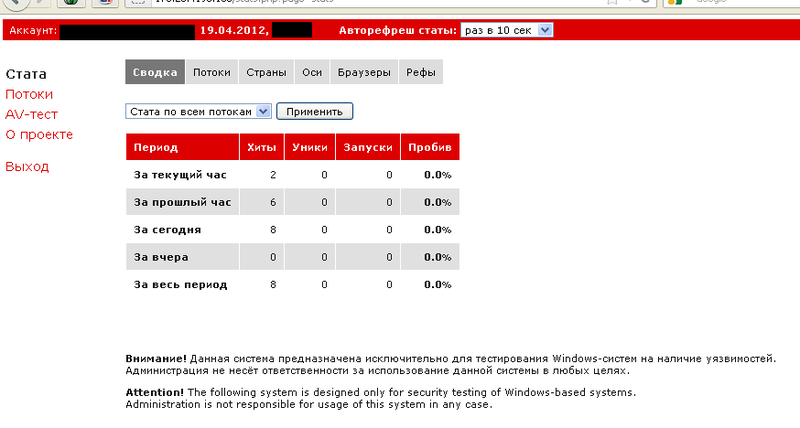
This is exactly the type of web malware exploitation kit that researchers from SpiderLabs recently spotted. Meet the RedKit, a private web malware exploitation kit, exploiting popular and already patched Java vulnerabilities, next to having an embedded QA (quality assurance) element embedded into it.
What's so special about RedKit, and how does it differentiate itself from the rest of the exploit kits currently observed in the wild? Next to exploiting CVE-2010-0188 and CVE-2012-0507, the cybercriminals behind the kit also offer legitimate traffic that will be later on converted to malware-infected hosts as a managed service.
See also:
- Web malware exploitation kits updated with new Java exploit
- Which are the most commonly observed Web exploits in the wild?
- Report: Patched vulnerabilities remain prime exploitation vector
- Seven myths about zero day vulnerabilities debunked
Moreover, in order to evade detection by security vendors, the cybercriminals behind the kit have introduced an API feature, helping customers of the kit acquire a new exploits-serving URL on an hourly basis. The next, and perhaps most important quality assurance element in the kit's propositions, is the fact that the malicious binary will be pre-scanned against 37 different antivirus vendors such as:
A-Sqared, AVG8, AVL, ArvaVir, Avast, Avira, BitDefender, ClamWin, Comodo, DigitalPatrol, DrWeb, Emsisoft, Ewido, F-Prot, F-Secure, GData, IKARUS, IkarusT3, KAV8, McAfee, NOD32, Norman, OneCare, Panda, QuickHeal, Rising, SAV, Solo, Sophos, TrendMicro, TrendMicro2010, Vba32, Vexira, VirusBuster, Webroot, ZoneAlarm, eTrust
in order to ensure that the malicious binary has a low detection rate before serving it to unsuspecting end and corporate users.
Thanks to the fact that this is a private kit, not actively advertised across popular cybercrime-friendly web forums, it will never manage to gain the market share of publicly obtainable exploit kits such as the market leading BlackHole web malware exploitation kit.
Rather surprisingly, researchers from SpiderLabs, have already intercepted an increase in attacks using the RedKit, indicating that the invite-only business model seems to be working.
What happens once an exploit kit gains a high market share? Once an exploit kit becomes well known within the cybercrime ecosystem thanks to its high conversation rate -- trafic-to-malware-infected-hosts -- international cybercriminals will localize these kits to their native languages, once again confirming that cybercriminals across borders are increasingly cooperating and working together.