Russian national, author of NeverQuest banking trojan, pleads guilty

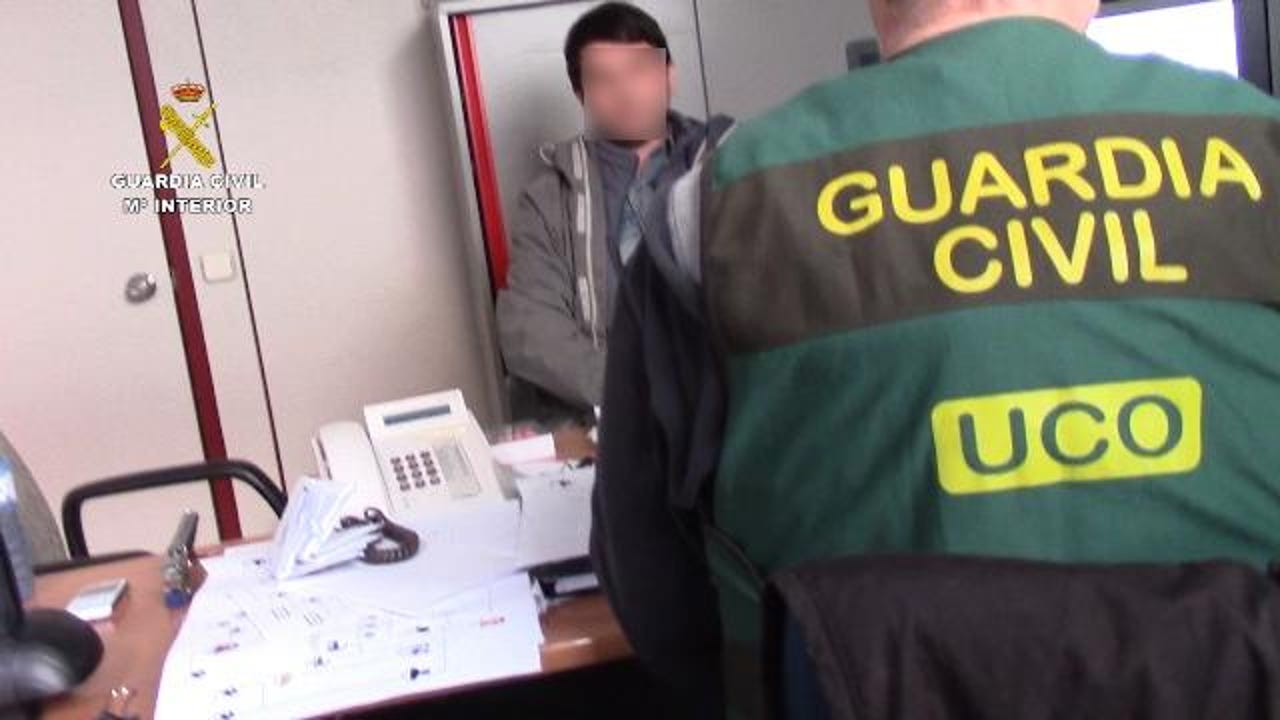
Image from Stanislav Lisov's arrest in Barcelona
Security
A Russian national pleaded guilty today in a New York court of creating, running, and infecting users with the NeverQuest banking trojan --also known as Snifula and Vawtrack.
The man's name is Stanislav Vitaliyevich Lisov, a Russian national who went online under the names of "Black" and "Blackf," and who, according to a Department of Justice press release, "was responsible for key aspects of the creation and administration" of the NeverQuest malware botnet.
More specifically, DOJ officials say Lisov was the one responsible with renting and then managing the servers that supported the NeverQuest trojan's backbone, the servers to which infected computers would connect, get instructions, and send stolen information.
US authorities say Lisov worked on NeverQuest between June 2012 and January 2015, defrauded banks of around $855,000 by emptying user accounts, and also attempted to sell the information he gathered from some of his victims.
Lisov came to be in US custody after he was arrested in Barcelona, Spain, in January 2017. Spanish police arrested Lisov and his wife when he returned a rented car at Barcelona's El Prat's airport. At the time, Lisov was on vacation and was preparing to leave Spain for Lyon, France, to visit friends.
Lisov's wife claimed her husband was a mere systems administrators and web developer at a company in Taganrog, Russia, and Russian authorities protested his arrest, calling it an "international kidnapping."
Spanish authorities approved Lisov's extradition to the US in August 2017, and the suspect was arraigned in a New York court in January 2018.
Lisov's guilty plea today represents the last pahses of an investigation into NeverQuest trojan operations that US authorities started back in 2014. Investigations broke through when they identified and seized NeverQuest servers located in France and Germany, which Lisov was managing and where authorities found data stolen from infected victims.
The NeverQuest malware worked just as any other banking trojan, intercepting login credentials for e-banking accounts, and sending the data to a remote command and control server.
At the time of Lisov's arrest, NeverQuest was one of the larger and active banking trojans. Months after Lisov's arrest, NeverQuest activity took a nose dive.
Lisov today pleaded guilty to one count of conspiracy to commit computer hacking, which carries a maximum sentence of five years in prison. His sentencing is scheduled for June 27, 2019.
Update: On November 21, 2019, Lisov was sentenced to four years in prison, and was ordered to pay forfeiture of $50,000 and restitution of $481,388.
Cybercrime and malware, 2019 predictions
Related cybersecurity news coverage:
- Microsoft Edge lets Facebook run Flash code behind users' backs
- A third of all Chrome extensions request access to user data on any site
- Vulnerabilities uncovered in popular password managers
- Malvertising campaign hits US users hard over Presidents' Day weekend
- Cisco patches a couple of root access-granting security flaws
- Malware that hunts for account credentials on adult websites tripled in 2018
- Major vulnerability found in Android ES File Explorer app TechRepublic
- Xiaomi electric scooter reportedly vulnerable to hijacking hack CNET