SCADA systems at the Water utilities in Illinois, Houston, hacked
UPDATE: DHS denies report of water utility hack
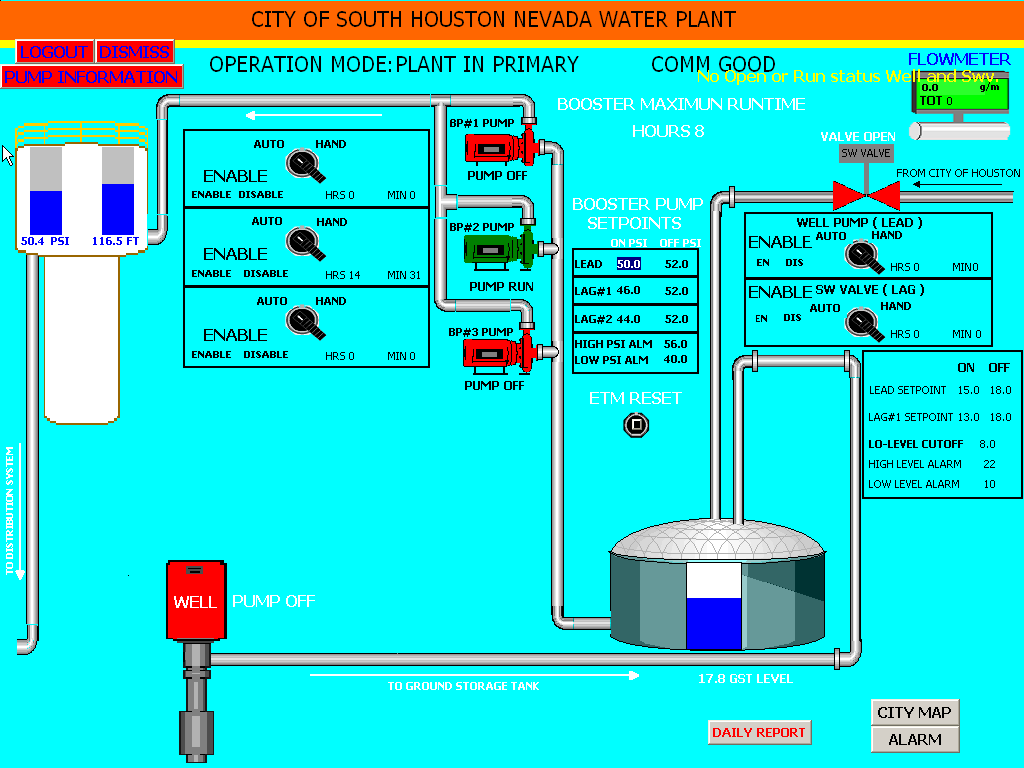
According to reports, the SCADA systems at the Water utilities in Illinois, Houston were recently hacked by a malicious attacker using the handle "pr0f".
The attacker has posted evident proof of a direct compromise of the SCADA systems at this water utility, with a separate report confirming that there was actual damage - "the SCADA system was powered on and off, burning out a water pump."
Joe Weiss, a managing partner for Applied Control Solutions, said the breach was most likely performed after the attackers hacked into the maker of the supervisory control and data acquisition software used by the utility and stole user names and passwords belonging to the manufacturer's customers. The unknown attackers used IP addresses that originated in Russia.
- The disclosure was made by a state organization, but has not been disclosed by the Water ISAC, the DHS Daily unclassified report, the ICS-CERT, etc. Consequently, none of the water utilities I have spoken to were aware of it.
- It is believed the SCADA software vendor was hacked and customer usernames and passwords stolen.
- The IP address of the attacker was traced back to Russia.
- It is unknown if other water system SCADA users have been attacked.
- Like Maroochy, minor glitches were observed in remote access to the SCADA system for 2-3 months before it was identified as a cyber attack.
- There was damage – the SCADA system was powered on and off, burning out a water pump.
Meanwhile, the "DHS and the FBI are gathering facts surrounding the report of a water pump failure in Springfield, Ill," Boogaard wrote.
Go through related posts: