Securing OS X 10.4: Tips from Apple and the NSA

Apple and the National Security Administration (NSA) have published a security guide for Mac OS 10.4 with key highlights on network administration, securing Safari and the importance of physical security.
As Jason O'Grady points out, the guide is helpful to anyone that works with a number of Macs. And the 171-page guide is also likely to become more relevant as Apple increasingly becomes a security target.
Among the key excerpts by chapter:
Chapter 1: Apple makes its case that 10.4 (Tiger) is more secure due to the operating system's design and architecture choices. Apple says 10.4 is more secure because it has:
- An open source foundation. "Using open source methodology makes Mac OS X a more robust, secure operating system, because its core components have been subjected to peer review for decades.
- Secure default settings. "When you take your Mac out of the box, it is securely configured to meet the needs of most common usage environments, so you don’t have to be a security expert to setup your computer. The default settings make it very difficult for malicious software to infect your computer."
- Modern security architecture. "Mac OS X includes state-of-the-art, standards-based technologies that enable Apple and third-party developers to build secure software for the Mac. These technologies support all aspects of system, data, and networking security required by today’s applications."
- Innovative security applications. "Mac OS X includes features that take the worry out of using a computer. For example, FileVault protects your documents using strong encryption, an integrated VPN client gives you secure access to networks over the Internet, and a powerful firewall secures your home network."
- Rapid response. "Because the security of your computer is so important, Apple responds rapidly to provide patches and updates."
Chapter 2: Apple recommends a reinstall to make sure the computer is secure. "If Mac OS X was already installed on the computer, consider reinstalling it. By reinstalling Mac OS X, and reformatting the volume, you avoid potential vulnerabilities caused by previous installations or settings."A lot of time is spent on permissions and whether to use software updates externally over the Internet or via an internal server.
Chapter 3: The big takeaway in this chapter: Physical security matters--a lot.
"The first level of security is protection from unwanted physical access. If someone can physically access a computer, it becomes much easier to compromise the computer’s security. When someone has physical access to the computer, they can install malicious software or various event-tracking and data-capturing services. Use as many layers of physical protection as possible. Restrict access to rooms that contain computers that store or access sensitive information. Provide room access only to those who must use those computers. If possible, lock the computer in a locked or secure container when it is not in use, or bolt or fasten it to a wall or piece of furniture."
In addition: "Hardware components such as wireless features and microphones should be physically disabled if possible. Only an Apple Certified Technician should physically disable these components, which may not be practical in all circumstances."
Directions are then given on what to disable every time there's a system update. Meanwhile, OS 9 also lingers:
"When you upgrade from previous versions of Mac OS X to Mac OS X version 10.4, an adaptation of Mac OS 9, known as Classic, remains on the computer. If you perform a new installation of Mac OS X version 10.4 without upgrading, Mac OS 9 is not installed on the computer. It is possible to install Mac OS 9 on computers with a new installation of Mac OS X version 10.4. Mac OS 9 lacks many of the security features included with Mac OS X, so you should remove it unless you need it. If you must use Mac OS 9, you can run it from a CD or DVD, or from a disc image."A walk-through of access warnings is also provided. In a nutshell, these warnings tell the user he is being monitored.
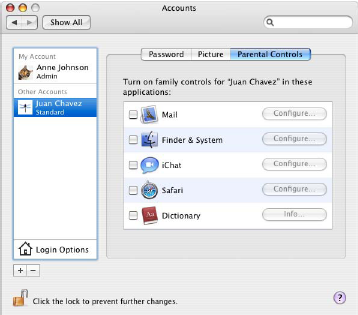
Chapter 4: Here Apple and the NSA talk about securing accounts. Among the tips:"When creating non-administrator accounts, you should restrict the accounts so that they can only use what is operationally required. For example, if you plan to store all data on your local computer, you can disable the ability to burn DVDs."
"The most powerful user account in Mac OS X is the system administrator, or root, account. By default the root account on Mac OS X is disabled and it is recommended you do not enable it...You should restrict access to the root account. If multiple users can log in as root, it is impossible to track which user performed root actions. Direct root login should not be allowed, because the logs cannot identify which administrator logged in. Instead, accounts with administrator privileges should be used for login, and then the sudo command used to perform actions as root."
There's also discussion about biometrics, tokens and smart cards.
Chapter 5: In this chapter there's discussion about how to secure systems preferences.
"System Preferences has many different configurable preferences within it that can be used to further enhance system security. Some of these configurations might be things to consider, depending on your organization. Mac OS X includes many system preferences that you can customize to improve security. When modifying settings for one account, make sure your settings are mirrored on all other accounts, unless there is an explicit need for different settings."
Among the tips:
- If you must use .Mac, enable it only for user accounts that don’t have access to critical data. Do not enable .Mac for your administrator or root user accounts.
- You should not enable iDisk Syncing.
- You should also modify login options to disable the Restart, Sleep, and Shut Down buttons. By disabling these buttons, the user cannot restart the computer without pressing the power key or logging in.
- The computer should not perform automatic actions when the user inserts CDs or DVDs. When you disable automatic actions in System Preferences, you must disable these actions for every user account on the computer. This does not prevent users from re-enabling automatic actions. To prevent the user from re-enabling automatic actions, you must restrict the user’s account, so that the user cannot open System Preferences.
Chapter 6: This chapter examines the importance of data and secure erasing if a computer is stolen. Much of the discussion is best suited for qualified professionals.
Among the tidbits:
- "By setting global permissions, encrypting home folders, and encrypting portable data, you can be sure your data is secure. Using the secure erase feature of Mac OS X, any deleted data is completely erased form the computer."
- "To protect files that you want to transfer over a network or save to removable media, you should either encrypt a disk image or encrypt the individual files and folders. FileVault doesn’t protect files transmitted over the network or saved to removable media."
- "Mac OS X provides several ways to securely erase files. You’ll have the choice of using one of three erase methods: a zero-out erase, a 7-pass erase, or a 35-pass erase. A zeroout erase sets all data bits on the disk to 0, while 7-pass and 35-pass use algorithms of varying complexity to overwrite the disk. The zero-out erase is the quickest. The 35-pass erase is the most secure, but it is also 35 times slower than the zero-out erase."
Chapter 7: This chapter covers network security.
Tips include:
- "You should only send email that is digitally signed and encrypted. Digitally signed messages let your recipients verify your identity as the sender, and provide assurance that the message has not been tampered with in transit."
- "In particular, you should change your Safari preferences to disable all AutoFill options, opening safe files after downloading cookies (only from sites you navigate to), and ask before sending nonsecure forms."
- "When using Safari, you should always use private browsing. Private browsing prevents Safari from logging your actions, adding web pages to the history, keeping items in the Downloads window, saving information for AutoFill, and saving your Google searches."
There's also discussion of VPNs, firewalls and connection protocols. To close out the document, there's checklist of all actions to secure OS 10.4 as well as daily best practices. Those best practices include all those password usage tips that IT users forget almost daily.