Security flaw makes most iPhones, iPads vulnerable to 'app replacement' hack

A security flaw in Apple's mobile operating system can leave iPhones and iPads vulnerable to attacks by cybercriminals, a new report warns.
Security researchers FireEye on Monday detailed a bug in which apps on iOS 7.1.1 and later, including the latest iOS 8 and iOS 8.1 update, can be effectively replaced with fake apps that can be used to install malware or vacuum up a user's data.
The technique, dubbed by the researchers as the "Masque Attack," relies on users clicking on malicious links in emails and text messages which point to pages that contain the app download. These apps are outside the walled garden of Apple's App Store and can replace genuine apps, such as banking or social networking apps.
"This vulnerability exists because iOS doesn't enforce matching certificates for apps with the same bundle identifier," the researchers said on the company's blog. "An attacker can leverage this vulnerability both through wireless networks and USB."
In an interview with Reuters, FireEye senior staff research scientist Tao Wei said word of the flaw began to leak out on specialized security-related forums in October.
The bug was disclosed to Apple months earlier in July.
The decision to go public was after Palo Alto Networks reportedly uncovered the first in-the-wild campaign to exploit the flaw in Apple's desktop, notebook, and mobile devices, dubbed WireLurker.
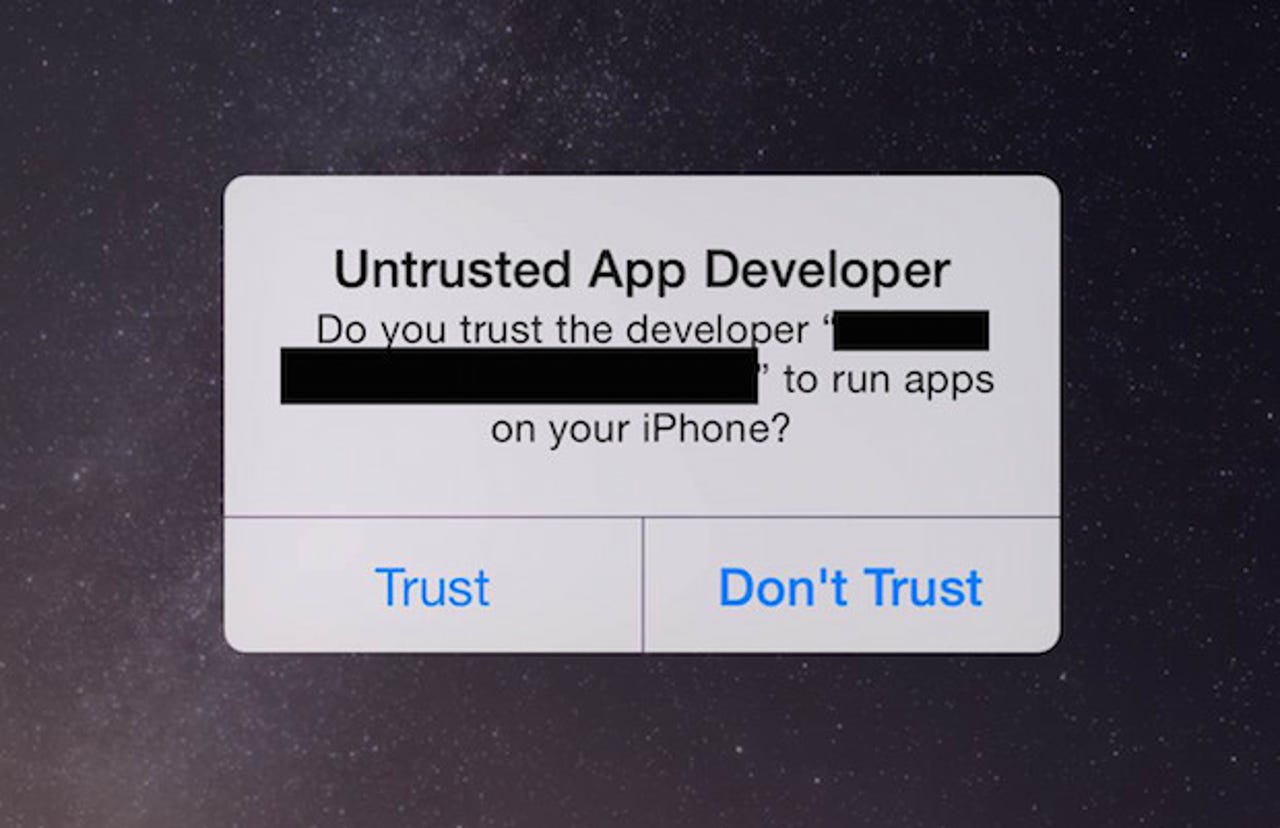
FireEye researchers said users should not install apps from sources other than Apple's App Store, or the user's organization — particularly if they are labeled with a "untrusted app developer" warning.