Security researcher creates Windows 8 'bootkit'

Austrian security researcher Peter Kleissner claims to have developed a 'bootkit' for Windows 8 that bypasses security features built into the operating system's bootloader.
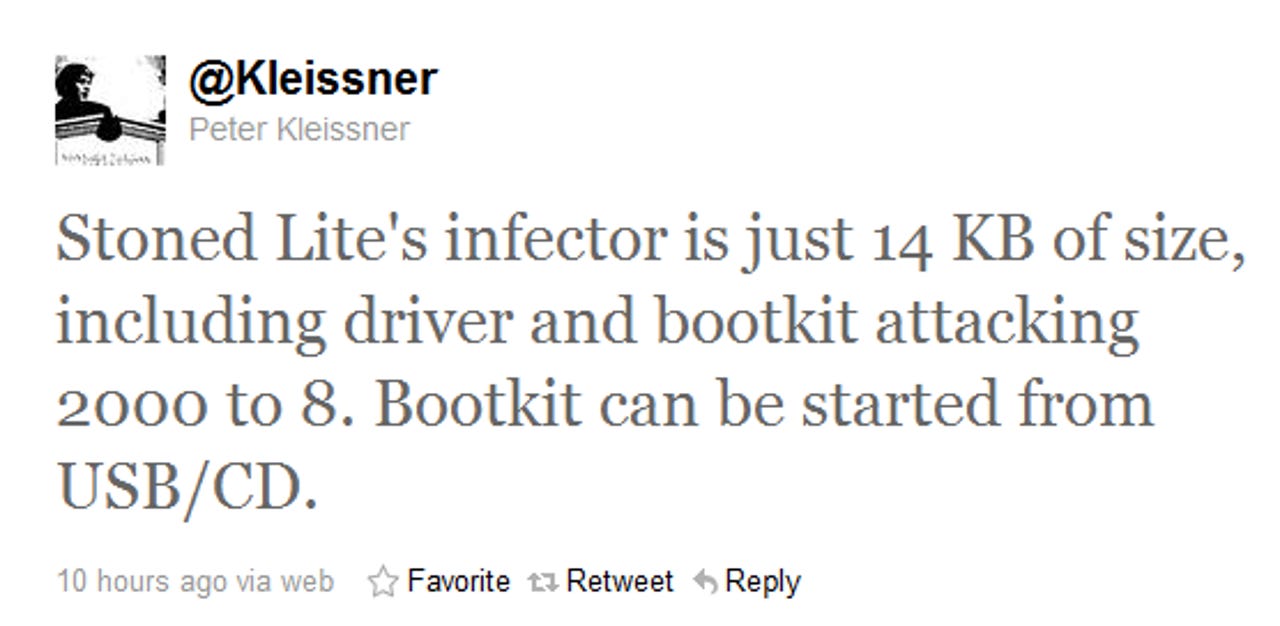
Kleissner broke the news on his Twitter account:
Kleissner previously developed a proof-of-concept 'bootkit' called Stoned[PDF] capable of attacking Windows platforms ranging from XP to 7. It seems that this work has now been extended to include Windows 8. The source code to Stoned is available for download from Kleissner's website.
According to Kleissner the new Windows 8 hack does not attack UEFI 'secure boot' feature and currently only works on systems running legacy BIOSes.
Microsoft has already been informed of the details of the hack:
The attack also bypasses UAC (User Account Control) for Admin accounts on Windows 8.
That means we can expect this vulnerability to be fixed before Windows 8 sees light of day.
Given Kleissner's background, I have no reason to doubt his claims at this stage. We'll know more about the attack when his paper is released on Saturday.
Kleissner is tentatively expected to present a paper at the MalCon security conference in Mumbai, India, later this month (he has yet to be granted a visa). Additionally, he is set to appear in court on December 15 on charges related to his Stoned 'bootkit' malware.