Security researcher finds critical XSS bug in Google's Invoice Submission Portal

techrepublic cheat sheet
A young Czech bug hunter has found a security flaw in one of Google's backend apps. If exploited by a malicious threat actor, the bug could have allowed hackers a way to steal Google employee cookies for internal apps and hijack accounts, launch extremely convincing spear-phishing attempts, and potentially gain access to other parts of Google's internal network.
This attack vector was discovered by security researcher Thomas Orlita in February, this year, and has been patched in mid-April, but only now made public.
XSS in Google's invoicing portal
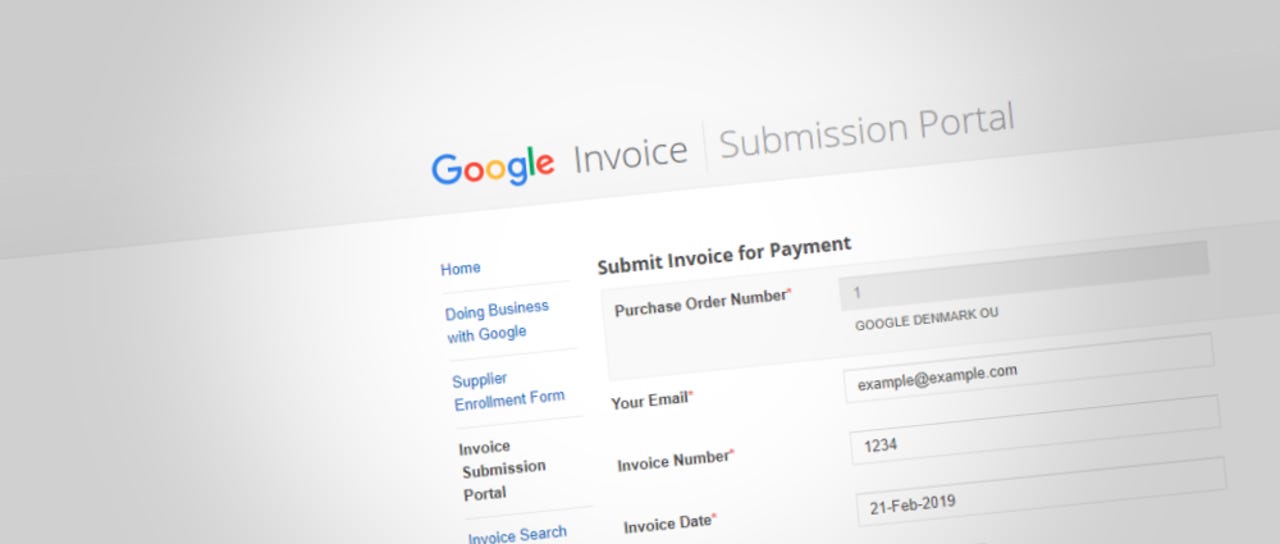
Described as a cross-site scripting (XSS) vulnerability, the security flaw impacted the Google Invoice Submission Portal, a public website where Google redirects business partners to submit invoices, based on contractual agreements.
Most XSS flaws are considered benign, but there are those rare cases where these types of vulnerabilities can lead to serious consequences.
One of those cases was Orlita's discovery. The researcher said that a malicious threat actor could have uploaded malformed files in the Google Invoice Submission Portal, via the Upload Invoice field.
Using a proxy, the attacker could have intercepted the uploaded file immediately after the form submission and validation operation took place, and modified the documents from a PDF to HTML, to the XSS malicious payload.
The data would have ended up being stored in Google's invoicing backend and would have executed automatically when an employee tried to view it.
Google's internal network could have been at risk
"Since the XSS was executed on a googleplex.com subdomain while the employee is logged in, the attacker should be able to access the dashboard on this subdomain where it's possible to view and manage the invoices," Orlita told ZDNet via email.
"Depending on the way cookies are configured on googleplex.com, it might also be possible to access other internal applications hosted on this domain," the researcher added.
Since most Google internal apps are hosted on the googleplex.com domain, this opens the door for attackers to a wide range of possibilities.
But, all in all, like most XSS security bugs, this bug would have depended on a threat actor's skill level and ability to pivot to more complex attacks.
"The severity of the impact is, of course, depending on how well it can be exploited to access their internal sites," Orlita told ZDNet. "For example, an attacker might try a phishing attack on the employee."
For more technical details about the XSS bug, Orlita's official vulnerability disclosure is the place to go.
Google I/O 2019: The biggest announcements from the keynote
More vulnerability reports:
- Microsoft's June 2019 Patch Tuesday fixes many of SandboxEscaper's zero-days
- Diebold Nixdorf warns customers of RCE bug in older ATMs
- Yubico to replace vulnerable YubiKey FIPS security keys
- Major HSM vulnerabilities impact banks, cloud providers, governments
- 'RAMBleed' Rowhammer attack can now steal data, not just alter it
- Microsoft blocks BLE security keys with known pairing vulnerability
- KRACK attack: Here's how companies are responding CNET
- Top 10 app vulnerabilities: Unpatched plugins and extensions dominate TechRepublic