Shifting IT delivery to tablets: The strategic issues

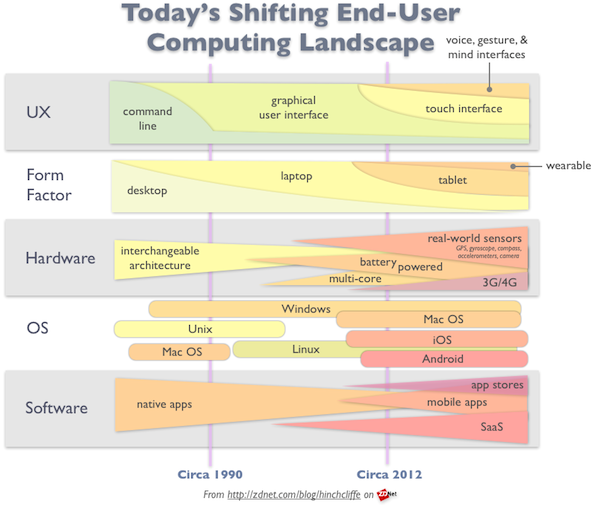
To access the real competitive advantage of the next-generation of end-user computing will require rethinking how tablets and their innate new capabilities can be used to transform business processes. A few weeks ago the IT analyst firm Forrester made what is probably the first major declaration that tablets will soon become the primary computing device for most users, even going so far as to say that they will 'rule' personal computing in the near future. While I think the numbers speak for themselves on this, I also believe that many organizations are either unready or unwilling to hear this yet.
Part of the reason for this avoidance is because of the substantial overhaul it will require IT departments to undergo, and major change is invariably painful and difficult. This retooling includes the full gamut of IT responsibilities: Infrastructure, architecture, processes, tools, skills, and governance, right when so many companies are also dealing with many other generational IT disruptions.
Another reason for unpreparedness is that the tablet revolution has largely become a bring-your-own-device (BYOD) phenomenon. This has started to displace IT as the primary middle-man when it comes to much of technology delivery inside of our organizations. The current wave of nearly rampant IT consumerization is in the center of this discussion: Users are starting to call the shots, and when they aren't, the tablet vendors are with app stores and other delivery channels that neatly sidestep yesterday's technology intermediaries, particularly the traditional IT department.
Finally, the tablet industry itself has moved faster recently than just about any technology bureaucracy ever could, setting records for end user adoption along the way. In just two years, the industry has gone from basically non-existent to 19% of everyone in North America having a tablet of one kind or other, according to the Pew Research Center. This has left most IT departments either in a profoundly reactive mode or attempting to be proactive but not moving rapidly enough.
Not helping matters is that the tablet industry is also highly fluid at the moment. Its overall direction -- especially for how it will meet the needs of enterprise customers -- is uncertain, other than simple facts like Apple is dominating and Android is #2. Beyond that, the details of the story keep changing, making it hard, or at least fairly risky, to place expensive bets on strategies for the future of service delivery in the enterprise.
Reformulating IT delivery in an uncertain tablet world
While difficult and potentially risky, waiting for the dust to settle and for clear trends to emerge in the mobile industry just isn't an option. Employees are using their tablets for work now. They're using the apps they prefer and they also want access to company networks, intranet services, and enterprise data. And this strong demand is not just coming from line workers, but from the most senior executives as well, whose requests are far more difficult to ignore or put off. Organizations must have a strategy that will co-evolve rapidly with the tablet industry, providing ways to maximize the business value that tablets offer while managing the downsides, the largest of which -- at least today -- are generally perceived as security, data control, regulation, and compliance.
While employees are busy downloading Dropbox, Evernote, and an array of MS Office editors en masse today, IT departments are first and foremost worried about the uncontrolled exposure to the cloud that these mobile apps often cause. This is because many of the most useful apps aggressively use the cloud and beam user data (and therefore company data) into their own data centers or those of their partners. It's essentially a nightmare situation for data security and virtually all organizations today are facing it.
Related: Tablets in the enterprise: Pros and cons
Given that tablet operating systems and management tools don't have the right level of declarative policy control over which apps that workers can use based on where say, they store their data (other than the highly ineffective route of white or blacklisting offending apps), and it's a recipe for the perfect tightrope walk: IT can't stop users from using tablets, but enabling them automatically triggers the scenarios that the Chief Security Officer is most worried about.
In reality, the decision points for how much and what to open up and tablet-enable is even more complex, along with the challenges of delivering IT on devices that were largely never designed for enterprise requirements. These are at least the following:
- Tablet OS/hardware proliferation. As of this writing, there is really just iOS and Android to deal with when it comes to tablets. However, especially with Android, but with iOS to a lesser extent, there are now literally hundreds of combinations of hardware and OS to deal with. The available features and capabilities of these combinations is making it quite challenging for mobile developers themselves, never mind enterprises. While Mobile enterprise application platforms (MEAP) such as Worklight and Sybase Unwired are trying to build intermediate abstraction layers so that enterprise can manage this issue, they also have the inevitable immaturity and common denominator challenges. They also generally create short-term advantages that can introduce long-term disadvantages. For now, most enterprises will have to maintain a manageable list of tablet devices/OSs that they fully support. However, especially with internally developed solutions, the challenge of strong device plurality remains steep.
- Service-enabling existing IT for tablets. While solutions to existing mainstays of IT, such as access to the general intranet and e-mail, are largely solved for tablets today, the issue of opening up and accessing existing enterprise data in the silos where they currently reside remains one of the biggest challenges. It's also what users typically want most. While it's relatively easy to make it possible for workers to access existing productivity documents, simple data feeds, and even use their desktops remotely through screen sharing solutions, these are not the native apps your workers are looking for. They want the same level of user experience from your mobile IT as they're getting from the apps in Apple's App Store and the Android Market. While many enterprise software vendors are now offering at least rudimentary tablet front ends for their products, they largely remain that: Rudimentary and unable to compare to consumer apps. Forward thinking enterprises will find out which apps have the most demand internally for tablet editions and work with development partners to quickly create them when vendor supplied version don't exist. In reality, however, IT leaders should expect a great deal of end user-led mobile IT solutions for this, ranging from data migration of company data to the apps they prefer to wholesale outsourcing of the custom mobile apps they need. If IT can't lead this, it will need to make these scenarios safe and secure at the very least, and fully manageable and governable if at all possible.
- Demand certain key enterprise-class features for tablets. In my analysis, given that they'll have to pick and choose their battles with consumer-oriented tablet vendors, enterprises should band together and require at least the following from tablet vendors:
- Declarative policy control over apps in the app store. Individually screening apps is a non-starter, given that there are already over a million in the two top app stores today. These policies should allow filtering by data storage location (local or cloud),
- Control over cloud data. Right now, enterprises can indeed gain control over mobile devices, but not the cloud services offered by tablet providers. From my conversations with CIOs recently, Apple's iCloud is one of the worst offenders, making it very difficult to wipe devices when employees leave the company, since a simple relogin from a wiped BYOD device just resyncs everything from iCloud, including company data. Companies are in a much worse situation with app providers themselves, who are far too fragmented to ever provide control over company data, or partition worker's private data from a enterprise's business data. This capability probably needs to be baked into the mobile platforms themselves. In the meantime, strict end-user policies combined with clear education of workers about the risks are about the only avenue open to businesses to protect their data unless they block iCloud and app stores completely, generally a non-starter.
- Location-aware degradation of features. Global companies in particular are challenged by mobile devices being used by workers that frequently travel. That's because tablets have features or use data in a way that can often be at odds with local laws about customer data, worker privacy, and more. While the Middle East is particularly problematic for mobile apps, especially when it comes to video and audio, even developed countries are putting more and more digital regulation in place that will make it easier for workers to inadvertently break the law. Tablet vendors need to make it easier for apps to be smarter about the world they work in and degrade features that break local laws. This is a topic I've heard in particular from a large number of global tablet customers and often they must just blacklist entire countries, negating the advantages of their mobile investments.
- Playbook for internal app development vs. outsourcing. Most organizations I speak with are going the outsourcing route because mobile app development has become such an involved discipline. However, large companies often don't have the option of ramping up mobile development shops on today's complex next-gen enterprise IT landscapes. Getting the balance right here will mean the difference between being somewhat agile from not delivering internal mobile apps to users in reasonable time frame.
- Mobile data security strategy. This is a set of tooling, infrastructure, and procedures to detect major data leaks and be as much ahead of problems right as they occur as possible.
Enabling tablets isn't enough: IT must be rethought
The real lesson is this: To get the primary advantages of tablets will require more than paving the old cowpath (i.e. merely conducting a literal translation of legacy IT to tablets.) Tablets are fundamentally different computing devices with entirely new capabilities. To get the real competitive advantage of the next-generation of end-user computing will require rethinking how tablets and their innate capabilities and strengths can be used to transform business processes. Location-awareness, always-connectedness, augmented reality, pervasive video/audio, and more can create highly situational and context-aware apps that hold the potential to provide hard business benefits. These benefits include boosting worker productivity, improving decision making, saving time, enabling more self-service, and reinventing business processes to operate in deeply integrated, highly immersive, and seamless new ways.
Related: Ten strategies for dealing with next-gen enterprise tech trends.
At the end of the day, as with the rapidly emerging field of social business, organizations that are able think as true mobile natives, and are successful in enabling the new business models and ways of operating which next-generation mobility makes possible, will reap the fullest rewards as they update and refine their end-user computing leadership.
See Also: