Snowden's privacy-oriented email provider shuts down under U.S. government pressure

An American company that specialized in private e-mail announced today that it is shutting down, effective immediately.
Normally, that wouldn’t be a big deal—after all, small tech companies fail all the time. But this company’s different. Lavabit, which had been in operation since 2004, was outed last month as Edward Snowden’s email provider. And today the company’s owner and operator, Ladar Levison, announced that he was “walking away from nearly ten years of hard work” rather than “become complicit in crimes against the American people.”
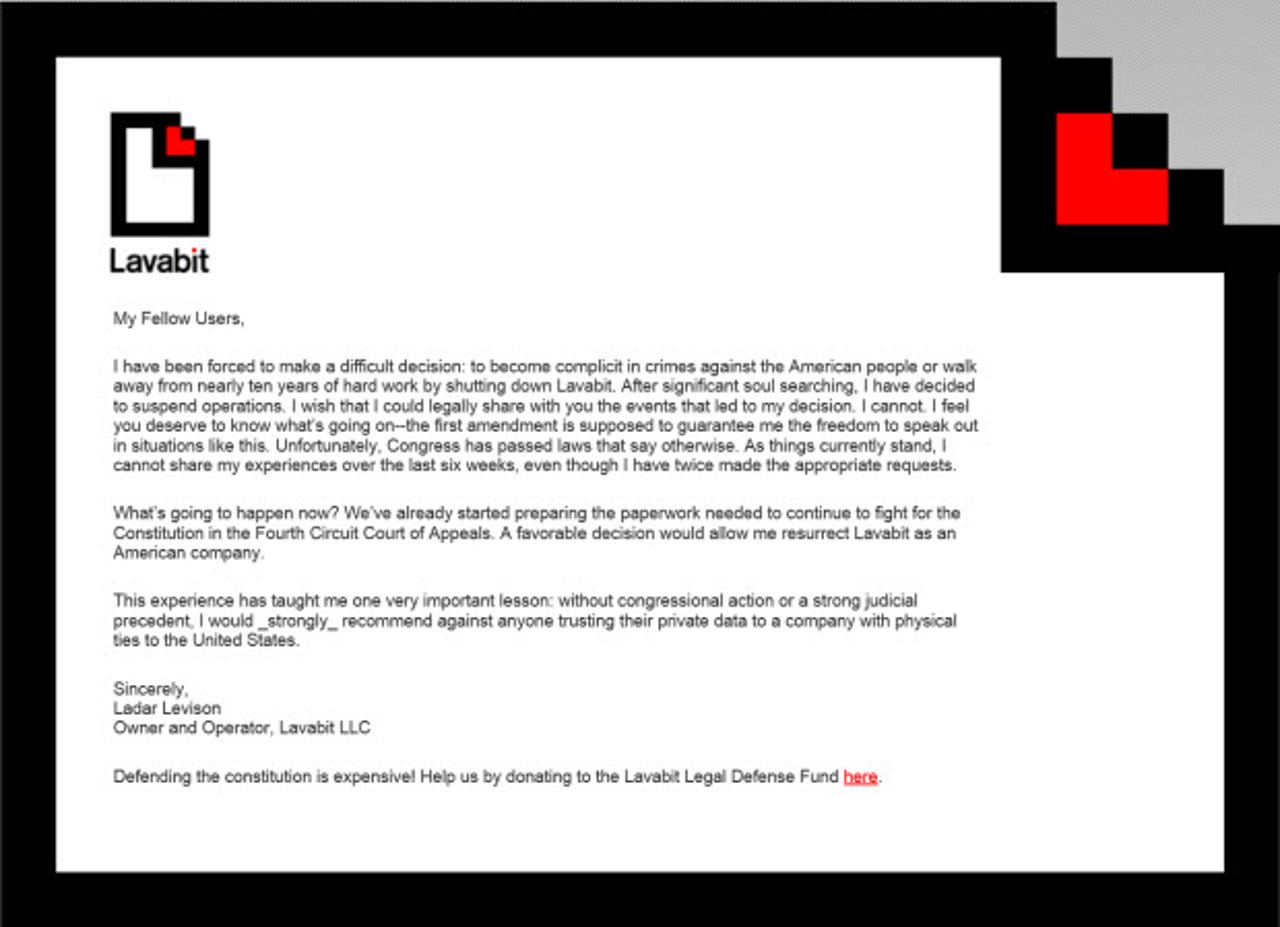
Visitors to Lavabit’s website, including paying customers, now see this message:
What happened?
The details are cryptic, but here are a few essential facts.
On Friday, July 12, Edward Snowden, who had used his position as a trusted contractor at the NSA to steal thousands of classified documents, held a press conference at Moscow’s Sheremetyevo Airport to complain about an “unlawful campaign” against him by the United States government.
In a liveblog of the event, the Boston-based GlobalPost.com reported this crucial detail:
Sergei Nikitin, the head of Amnesty International’s Moscow office, and Vladimir Lukin, the Kremlin-appointed human rights ombudsman, are among those who confirmed to Russian news agencies that they would accept the invitation to Moscow’s Sheremetyevo Airport, reportedly sent Thursday from an email address supposedly belonging to Snowden.
The note, which could not be verified, requested the attendance of a slew of well-known rights workers and lawyers “for a brief statement and discussion regarding the next steps forward in my situation,” according to a copy of the invitation posted Lokshina.
It was sent from the email address “edsnowden@lavabit.com,” according to Lokshina’s post, and signed “Edward Joseph Snowden.”
[emphasis added]
Before and after Edward Snowden engineered the NSA document heist, he had been in touch via e-mail with several journalists scattered around the world. As part of the communication process, Snowden insisted on encrypting his correspondence using PGP software. He also used Lavabit, which offered “Security Through Asymmetric Encryption” as a key part of its service. In a white paper explaining its technology, Lavabit said “Lavabit has developed a system so secure that it prevents everyone, including us, from reading the e-mail of the people that use it.”
(The whitepaper is no longer available online, but a copy is still available in the Internet Archive.)
According to that whitepaper, here’s what happened to messages stored at Lavabit:
[I]ncoming e-mail messages are encrypted before they’re saved onto our servers. Once a message has been encrypted, only someone who has the account password can decrypt the message. Like all safety measures, encryption is only effective if it’s used. To ensure privacy, Lavabit has developed a complex system that makes the entire encryption and decryption process transparent to the end user.
[…]
We should note that this encryption process is only secure if you select a strong password. If your password is weak, an attacker would only need to brute force the password to crack our encryption. We should also note that this feature only protects messages on the Lavabit servers. Messages can always be intercepted before they reach Lavabit or between Lavabit’s servers and your personal computer, if SSL is not used. Finally, messages can be retrieved from your local hard drive if encryption software isn’t used on your computer to protect the files. These vulnerabilities are intentional. Our goal was to make invading a user’s privacy difficult, by protecting messages at their most vulnerable point. That doesn’t mean a dedicated attacker, like the United States government, couldn’t intercept the message in transit or once it reaches your computer.
And this section is inadvertently prescient:
Our hope is the difficulty associated with those strategies means they will only be used by governments on terrorists and scammers, not on honest citizens. If you’re intent on hiding your communications from the government, we recommend you investigate systems that secure messages throughout the entire e-mail system and not just at one particular point along that journey.
Levison’s note says, “I wish that I could legally share with you the events that led to my decision. I cannot.” That suggests he and his company were served with a warrant whose terms included a gag order prohibiting any disclosure of the order’s contents. That warrant could have been a National Security Letter, but it could just as easily have been a court order requiring the company to cooperate with an interception of Snowden’s correspondence as well as those of other Lavabit subscribers who might have been allegedly conspiring with Snowden.
The outrage over overly broad surveillance of U.S. citizens by the NSA doesn’t seem to apply here. Snowden freely admitted that he had broken the law in an act of civil disobedience. He has been indicted on three counts of espionage, theft, and conversion of government property. The criminal complaint was filed not in the secret Foreign Intelligence Surveillance Court but in the United States District Court in Virginia.
In a post on Google+, CNET’s Declan McCullagh speculated that Lavabit had been served with a court order to intercept passwords and possibly encryption keys, that they had fought the order for six weeks and lost, and had shut down the service rather than comply.
That’s certainly a reasonable scenario, but those who know the details aren’t talking.
In a closing note, Levison offered a warning about anyone doing business with U.S. tech companies:
This experience has taught me one very important lesson: without congressional action or a strong judicial precedent, I would _strongly_ recommend against anyone trusting their private data to a company with physical ties to the United States.
So far, no other U.S. companies have reported similar orders.