Source code for ikee iPhone worm in the wild
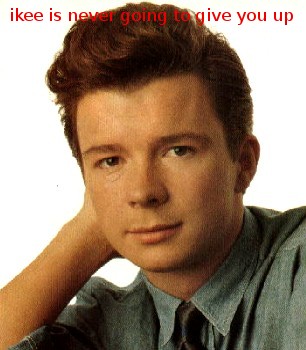
Upon successful exploitation of devices running SSH with default passwords, the worm would announce its presence by changing the wallpaper to a new one featuring pop-star Rick Astley.
Despite the author's intention to raise awareness on the issue, the originally released as "closed source" code for the "awareness-building worm" has now leaked in the wild, with several modifications already capable of stealing a compromised iPhone's contacts and SMS messages.
Interestingly, in a recent poll results, 76% of the people who voted believe that "He's done iPhone users a favour. This was an acceptable way to raise awareness of poor security". I wonder what would their attitude be if they knew that several modifications and customized modules are already capable of stealing their SMS messages and contacts, potentially using them for fraudulent activities.
What do you think, did the teenagers that launched these attacks during the last two weeks did someone a favor, or did they actually started a short-lived trend with malicious copycats already looking for ways to exploit the potentially hundreds of thousands of jailbroken devices using the easy to find 3G IP ranges?
TalkBack.