Spam coming from free email providers increasing
After analyzing three weeks of spam data between June 13 to July 3, 2008, Roaring Penguin Software Inc. found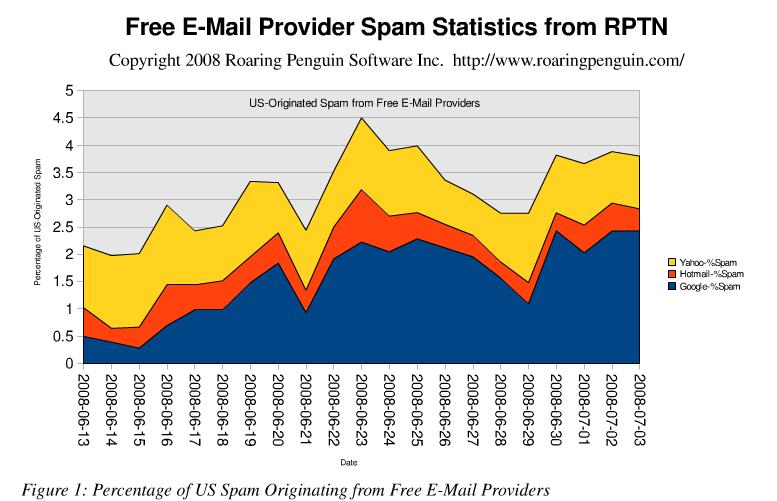
"Spammers are increasingly using free e-mail providers to avoid IP address-based reputation systems. These systems track mail sent by various IP addresses and assign each IP address a rating. Some anti-spam software operates largely or exclusively on the basis of the IP address rating.
Roaring Penguin's data shows that over the three weeks from June 13 to July 3, 2008, the percentage of US-originated spam originating from the top 3 free e-mail providers (Yahoo, Google and Hotmail) rose from about 2% to almost 4%. Roaring Penguin believes that spammers are using Google's service in particular to send spam, relying on the fact that blacklisting Google's servers is impractical for most organizations. According to their data, the probability that an e-mail originating from a Google server is spam rose from 6.8% on June 13 to a whopping 27% on July 3."
Spammers and phishers are not just interested in the clean IP reputation of free email providers, they are also interested in taking advantage of the trust they have established among themselves through the use of DomainKeys and Sender ID Frameworks, and by abusing this through the bogus accounts that they've automatically registered by breaking the CAPTCHA based authentication, reach the widest possible audience and ensure the successful receipt of their spam/scam.
How are they managing to efficiently abuse these services, and is CAPTCHA breaking for the purpose of automatically registered bogus accounts to blame? The broken CAPTCHAs are only part of the problem. It all starts from the basics, in this case, the companies themselves admitting there's a problem and how committed they are in not just fighting incoming spam, but also, outgoing spam.
The whole quality and assurance process applied by spammers is nothing new, in fact phishers and malware authors have been putting more efforts into coming up with easier ways to measure the return on investment (ROI) for themselves, and to present clear performance data to those taking advantage of their services. Just because someone has successfully sent several million spam emails, doesn't mean that the messages didn't got filtered, and when they did, what number exactly. Coming up with in-depth spam campaign metrics, and processes for verification of delivery, are becoming a top priority for everyone involved in this underground ecosystem.
The problem of spam and phishing coming from free email providers, has had its peaks in the past two years, prompting popular spam blacklists such as SORBS and Spamcop to blacklist entire Gmail servers due to their inability to obtain the real sender's IP. It's a signal from the anti spam community, and since Gmail will continue not revealing the real sender's IP, something they've received a lot of criticism from anti spam vendor, but a lot of applause from privacy fighters, the best they can do is balance their incoming VS outgoing spam fighting strategy. Here's a comment from an anti-spam vendor commenting on the problem back in 2006 :
"Gmail has taken an extreme position on privacy that inhibits the antispam community from doing their job, and it's ticking people off," says Tom Gilles, co-founder of IronPort. Some 10% to 15% of the spam IronPort sees comes from free Web-mail accounts, too big a slice to turn a blind eye to. "From time to time, Gmail mail is getting blocked because spam is leaking out of their service," Gilles says. "Sometimes the babies get thrown out with the bath water, and that is the rub.
It's difficult to gauge how widespread the problem of missing Gmail is, since no blocking records are available, though experts worry it's growing along with the Gmail service. Gmail had 6.7 million visitors in February, up 4.1 million from a year ago, according to measurement firm comScore Networks, a jump that suggests lost email has yet to hurt the service's growth. Yahoo Mail is still nearly 10 times bigger, hosting 64.6 million visitors last month, and AOL and Hotmail are also orders of magnitude larger. The situation reveals again how the studiously iconoclastic search engine is wrangling with where to draw the line on Internet privacy. As in other recent cases, Google is taking a harder line than its peers."
Moreover, the abuse of the authentication at these free email providers, by either breaking the CAPTCHA images automatically, or outsourcing the process to human CAPTCHA breakers who earn cents to authenticate the registration process for the spammers to abuse, is clearly making an impact. For instance, underground services offering hundreds of thousands of pre-registered bogus accounts are popping up like mushrooms these days, and their maturity into a customer-tailored proposition offering everyone the possibility to pre-register bogus accounts at services and web sites that they are not currently targeting, speaks for the confidence they've built into their ability to deliver the goods. The most recent one which I covered in a previous post is continuing to automatically pre-register accounts with its inventory emptying and filling itself automatically in between the customer's feedback indicating the quality of the service. Here's a sample of their inventory as of the last five minutes :
- Yahoo.com - 270,565 pre-registered accounts
- Hotmail.com - 167,013 pre-registered accounts
- Gmail.com - 159,892 pre-registered accounts
These is just the tip of the iceberg, with many other such services offering different inventories and using different tactics in the registration process. And while the companies themselves are keeping track of the latest developments in this ongoing abuse of their services, it's all a matter of drawing the line at a particular moment of time. For instance, a known to be malware infected IP that has repeatedly attempted to send hundreds of thousands of phishing and spam emails on behalf ot the botnet its participates in, shouldn't be trusted in any authentication or registration attempts if you're to take the radical approach, or have the end user warned about what's going on and why is she not allowed to use the site's services unless action is taken. The point is that, preventing automatic authentication abuse as a process is very similar to preventing click fraud, and fighting spam in general with the only different in the shift of perimeters from applying the techniques on incoming emails, to the authentication process in general.
Most of the human CAPTCHA breakers, and the automated programs will either abuse malware infected hosts as open proxies, or use open proxy lists in order to change their IP on every several registrations. Considering that the majority of malicious activity comes from well known bad parties are often blocked by default at the email gateway without even bothering to inspect the content in email messages coming from their networks/IPs, the same approach, activity from malware infected hosts should be challenged more aggressively than it is for the time being.
The increasing spam and phishing emails originating from legitimate email service providers is prone to increase, and fighting incoming spam should be balanced with fighting outgoing spam. Moreover, email spam is so Web 1.0, that the possibilities for abusing the joys offered by Web 2.0 services are slowly starting to materialize, with spammers being a step ahead of the filtering solutions.