Stop calling everything a "hack"

There's something that's been bugging me all day.
On Wednesday, security researcher Justin Shafer reached out to a handful of security reporters after he found that Nevada state government's website was leaking thousands of applications from its medical marijuana dispensary program.
Shafer found the leaky web portal by using Google to search government websites for words like "social security," which anyone can do with relative ease. He found one listed web address, ending in a number, which pointed to a PDF file purporting to be a medical marijuana dispensary application. Altering the number in the web address let anyone view different applications.
The first reports came in.
- CSO Online: "Agent applications for Nevada's medical marijuana program exposed"
- The Daily Dot: "Medical marijuana portal exposes thousands of Social Security numbers"
- ZDNet: "Nevada leaks thousands of medical marijuana dispensary applications"
See the common thread? The leak was Nevada's fault. No systems were hacked or breached.
Around the time we published, the site had been taken down to "limit the vulnerability," according to spokesperson Martha Framsted.
Framsted said in a phone call Wednesday that it was "aware of the leak" from the security researcher via multiple reporters, including those from CSO Online and The Daily Dot, and would release a statement later in the day.
In our brief conversation, Framsted said that the state's IT staff had pulled the website offline in order to prevent the data from leaking further. There wasn't a hint of accusation -- clearly, this was a system that wasn't working properly.
Then, headlines began to turn from "leak" and "exposed", to "hacked" and "breached" later in the day.
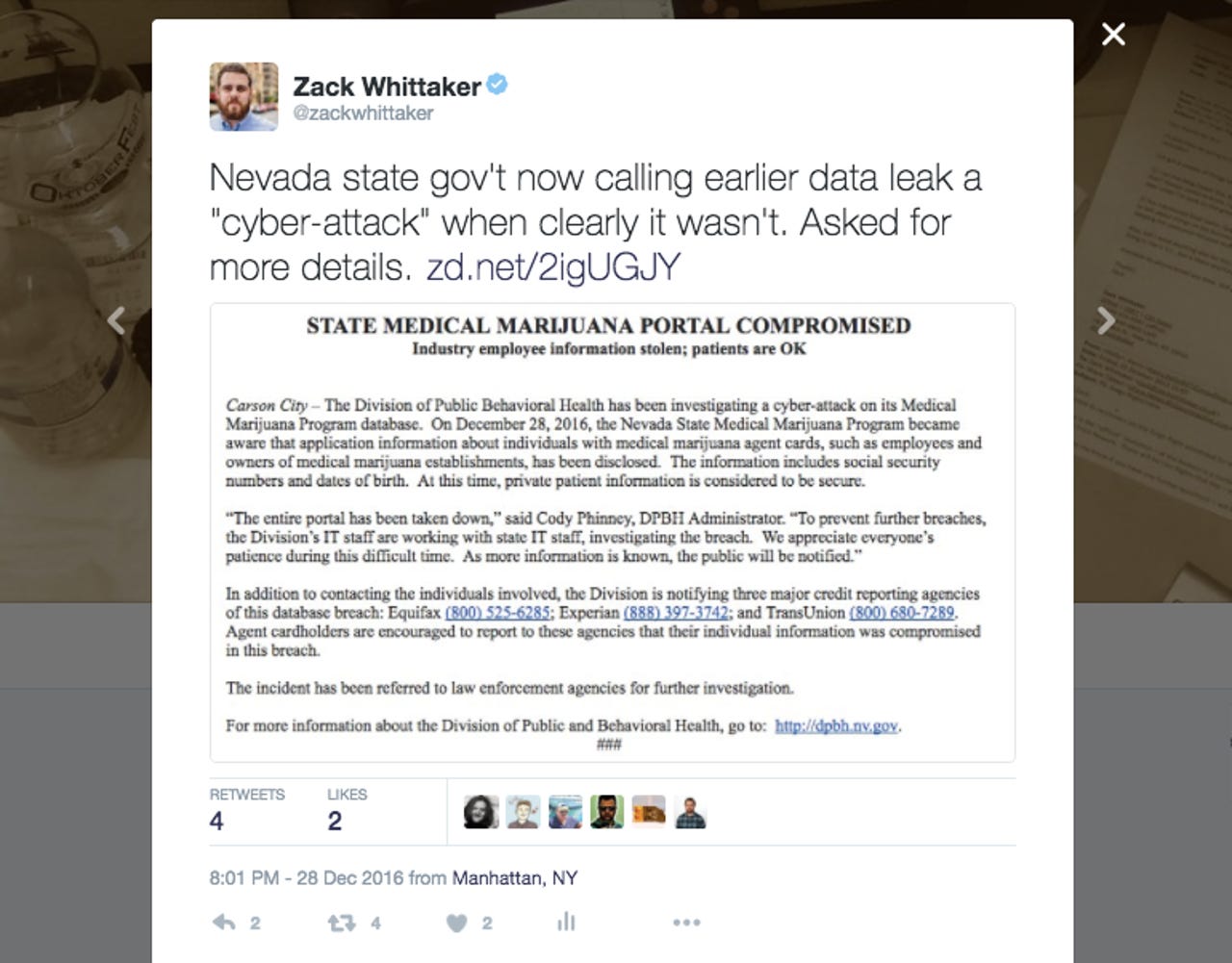
What happened? Nevada's official statement reversed its rhetoric entirely and began blaming the leak on a "cyberattack." The statement said that industry employee information had been "stolen," adding that the incident had been "referred to law enforcement agencies for further investigation."
Enter this tweet.
In a follow-up email, Framsted would not say why the state had seemingly changed its tune in the matter of a few hours.
"This is an ongoing investigation and as we have more details we will make those details available to you," she said.
Not all disclosures of data are the same. A hack may lead to a breach, but a leak isn't a hack, nor does a breach always lead to a leak.
Confusing -- right?
Hacking a computer is an illegal act, usually by way of unauthorized access. But when data is sitting on the internet in an unprotected manner, that's a leak. The two aren't comparable, but US computer hacking laws are outdated and vague.
That confusion can often lead to misplaced blame, and while that alone can lead to serious consequences, it can also be used to pass the buck entirely.
When you call a leak a "hack," you're calling the person who found the vulnerability a "hacker." That immediately tarnishes what is usually an act of good intention -- reporting a bug either to the affected party or the media -- with that of an illegal act.
But better a good guy finding the flaw than a bad guy. And this kind of response by Nevada state is just one incident in a list of many that pose a larger question for security researchers.
Shafer, and others who have brought matters of insecurity to their owner's eyes, often face backlash or legal threats from the very people they're trying to help.
Incidentally, Shafer had been accused of "hacking" before, simply for informing a company, Eaglesoft, a provider of dental practice management software, that it was leaking confidential patient data by storing it in an unsecured FTP folder, available for anyone with an internet connection to see. His house was raided by the FBI as a result. But, unsurprisingly, no charges have been filed over the matter.
It makes you wonder why security researchers even bother.
For bug finders, it's their duty, responsibility, and often -- as we've seen in this case -- also an occupational hazard. But each time there's pushback stemming from good intentions, it's only going to deter researchers from doing their good work.
That leaves open field for others of the criminal variety to find the flaws instead. And we all know that won't go down well.