Study: password resetting 'security questions' easily guessed
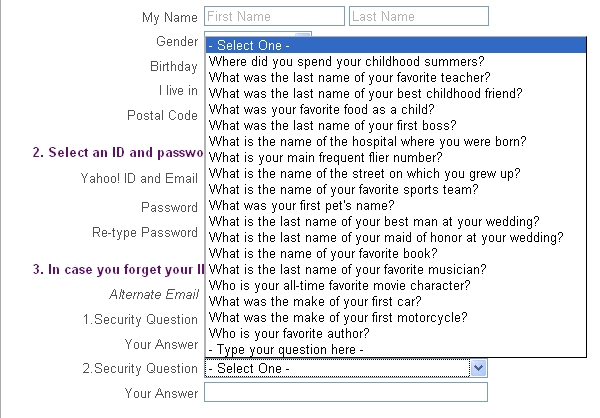
Here's an abstract from the study presented at this year's IEEE Symposium on Security and Privacy, by Stuart Schechter, A. J. Bernheim Brush, and Serge Egelman :
"We ran a user study to measure the reliability and security of the questions used by all four webmail providers. We asked participants to answer these questions and then asked their acquaintances to guess their answers. Acquaintances with whom participants reported being unwilling to share their webmail passwords were able to guess 17% of their answers. Participants forgot 20% of their own answers within six months. What’s more, 13% of answers could be guessed within five attempts by guessing the most popular answers of other participants, though this weakness is partially attributable to the geographic homogeneity of our participant pool."
Moreover, upon assessing the memorability of the 'secret questions', the user study involving 130 participants (64 male and 66 female) also found out that the harder ones to guess were also the hardest ones to remember.
Two similar recently conducted studies confirm these findings. For instance, in "Choosing Better Challenge Questions" Mike Just and David Aspinall found out that users also tend to stick to low entropy answers which are potentially vulnerable to brute forcing attacks. The researchers came to the same conclusion in their second study "Challenging Challenge Questions" pointing out that given the average answer length of less than 8 characters, the authentication system relying upon only a single security question is highly vulnerable to brute force attack.
Case in point - the applicability of their findings can be confirmed through real-life incidents. For instance, the Sarah Palin hacker managed to reset her password by Googling for the answer to her 'secret question', followed by two similar password resetting attacks aimed at Twitter employees throughout the past one year. Moreover, a huge percentage of the commercial 'password recovery services' or email hacking for hire propositions rely on password resetting attacks next to the plain simple malware infection, and attempt to exploit a XSS flaw within a particular web based email service provider.
All of these findings, combined with the misalignment of the end user's perception of security offered by security questions and the extend to which the answers have already been made public, can be summarized with a single security tip - make sure that you don't tweet about how much fun you had on your honeymoon in Paris a couple of years ago, when your security question is "Where did you spend your honeymoon?", which you would have presumably answered correctly.
What do you think, are security questions a viable form of authentication? Talkback.