The future of mobile malware - digitally signed by Symbian?
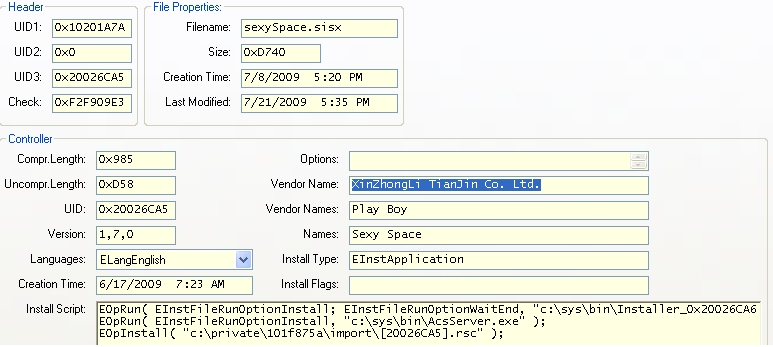
Upon notification, the Symbian Foundation quickly revoked the certificate used by the bogus Chinese company XinZhongLi TianJin Co. Ltd, however, due to the fact the revocation check is turned off by default, the effect of the revocation remains questionable.
What are the chances that future malware authors could bypass the code signing procedure again?
The missing human inspection, instead of the total reliance on mobile antivirus scanner, could have prevented the signing of the malware, since the malware authors didn't even bother to create a fake company page on the Internet in an attempt to improve their legitimacy. For instance, none of the previously used Chinese company names (XiaMen Jinlonghuatian Technology Co. Ltd., ShenZhen ChenGuangWuXian Tech. Co. Ltd. and XinZhongLi TianJin Co. Ltd.) have any public reference.
The Symbian Foundation is investigation how they can improve the signing procedure, and detect malware before they issue yet another certificate to its authors. Over 2000 applications go through the signing process each month.