The godfather of ransomware returns: Locky is back and sneakier than ever

Locky is back with a new infection technique.
The ransomware that drove last year's boom in file-encrypting malware is back, and this time it's even harder to detect.
Ransomware cost its victims some $1bn during 2016, with Locky one of the most widespread variants, infecting organisations across the globe.
However, the start of 2017 saw a sudden decline in the distribution of Locky, to such an extent that another form of ransomware -- Cerber -- has usurped Locky's dominance.
But after being all but written off, Locky is staging a comeback. Cybersecurity researchers at Cisco Talos have observed a surge in emails distributing Locky, with over 35 thousand emails sent in just a few hours. This surge in distribution is being attributed to the Necurs botnet, which until recently focused on spamming pump-and-dump stockmarket scams.
This time, however, the Locky campaign is harnessing an infection technique associated with the Dridex botnet, in an effort to boost the chance of compromising targets.
As noted by cybersecurity researchers at PhishMe, this new form of Locky begins by using a familiar tactic -- a phishing email with an attached file the message claims is a document detailing a payment or scanned documents. But rather than the more common practice of attaching a compromised Office document, an infected-PDF is sent instead.
Locky phishing email
It's not the first time this technique has been used, with infected PDF documents commonly used to distribute the Dridex malware botnet. Cybersecurity researchers say Locky is leveraging PDF documents for one simple reason: more cyberattackers are exploiting Office macros to distribute malware, raising awareness of potential threats.
Upon opening the infected document, the victim is prompted to give the PDF reader permission to open a second file.
This second file is a Word document that asks for permission to run macros, which it uses to download the Locky ransomware. This two-step infection process is a simple evasion technique, but increases the chances of victims installing ransomware.
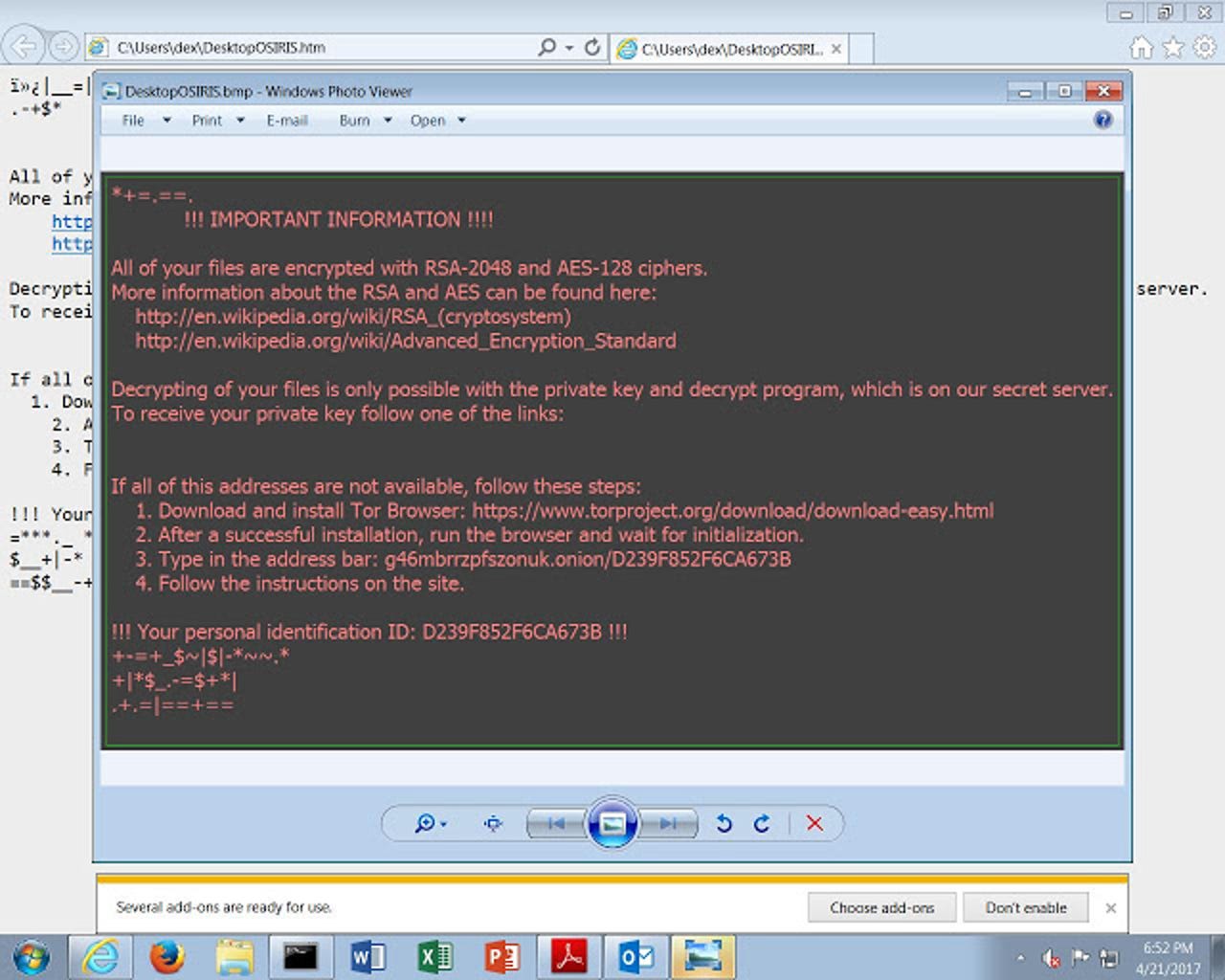
The Locky payload still operates much as it always has, seeking out and encrypting critical files on victims' machines and demanding a Bitcoin ransom in exchange for restoring the system.
One difference from previous Locky versions is that the ransomware asks victims to install the Tor browser in order to view the ransom payment site, which researchers suggest is down to Tor proxy services frequently being blocked and the burden of maintaining a dedicated Tor2Web proxy site.
Currently, this version of Locky is demanding a ransom of one Bitcoin, which equates to $1200, €1100 or £935. It's a much more ambitious ransom demand, but cybercriminals are aware that many organisations are willing to give in and pay to avoid losing business-critical files.
Ransomware has become one of the biggest menaces on the web. A ZDNet guide contains everything you need to know about it: how it started, why it's booming, how to protect against it, and what to do if your PC suffers an attack.
READ MORE ON CYBERCRIME
- Ransomware: Why it's a really big problem for small businesses
- New dark web scheme lets wannabe cybercriminals get in on ransomware - for free
- Report: Ransomware attacks grew 600% in 2016, costing businesses $1B [TechRepublic]
- Tell Bart and other ransomware families to 'Eat my shorts' with new, free decryption tools
- The horror! Mac users must beware of ransomware (like everyone else) [CNET]