The Neosploit cybercrime group abandons its web malware exploitation kit
The end of the Neosploit web malware exploitation kit? RSA's FraudAction Research Labs recent monitoring of ongoing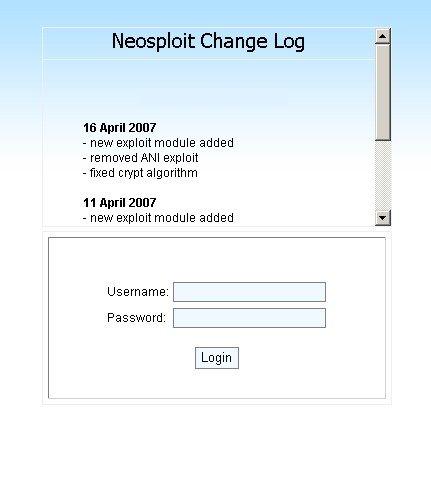
Is this really the end of Neosploit? Could be, but it's definitely not the end of web malware exploitation kits in general :
"In mid-July, however, evidence showed that Neosploit's successful business was running into problems. It is likely that Neosploit was finding it difficult to sustain its new customer acquisition rate, and that its existing customers were not generating enough revenue to sustain the prior rate of development. These problems appear to have been too much of a burden, and we now believe that the Neosploit development team has been forced to abandon its product. Like any responsible business, the Neosploit team is trying to be remembered as a good business that might one day return. Our sources reported that they took the time and effort to part properly with an "out of business" announcement. Or as the translation goes:
"Unfortunately, supporting our product is no longer possible. We apologize for any inconvenience, but business is business since the amount of time spent on this project does not justify itself. We tried hard to satisfy our clients' needs during the last few months, but the support had to end at some point. We were 1.5 years with you and hope that this was a good time for your business."
Let's discuss their business model, how other cybercriminals disintermediated it thereby ruining it, and most importantly, how is it possible that such a popular web malware exploitation kit cannot seem to achieve a positive return on investment (ROI).
The short answer is - piracy in the IT underground, and their over-optimistic assumption that high-profit margins can
You cannot pitch an open source malware kit as a proprietary one
Neosploit, just like the majority of other web malware kits, are open source, which means the customer can add new functions and exploits, enjoying the malware kit's modularity. Neosploit Team's business model was relying on the wrong assumption that charging thousands of dollars for a proprietary malware kit with the idea to position it as exclusive one could result in a high-growth business model. Moreover, according to their statement that the amount of time spend on the "product" isn't justifying itself wrongly implies that it takes a great deal of time to embedd a publicly available exploit code for a recent vulnerability into the while, while in reality it doesn't.
Furthermore, the coders of crimeware kits like Zeus for instance, have tried to enforce "licensing agreements", ironically by doing so they claim ownership over the crimeware kit in general. In fact, coders of malware for hire are taking advantage of the same end user agreements, forbidding the customer of reverse engineering the malware they've just coded, and also sharing it with others. And so, the Neosploit kit leaked into the wild, for script kiddies and sophisticated attackers to take advantage of, from here no one was bothering to purchase a copy of the malware kit, and started persinally embedding new exploits within.
Localization to foreign languages is done on behalf of the customers, not the malware kit's coders
One would logically assume that if a Russian malware coder wants to target potential customers from Chine, he'd bother translating the entire command and control interface next to the documentation of the malware kit into the local language. In reality through, this localization has been done mainly on behalf of users who've obtained leaked copies of the malware kits and localized them into their native languages, thereby allowing easier entry into cybercrime in general. For instance, the originally Russian MPack and IcePack malware kits were localized to Chinese by Chinese hackers last year, the same localization of the Firepack malware kit to Chinese took place this May, and suprisingly, IcePack got localized to French the same month.
Web malware exploitation kits are a commodity
The again, when you have 637 million Google users surfing with insecure browser and getting exploited with "last quarter's critical browser vulnerability", why bother introducing zero day vulnerabilities within your kit when outdated and already patched ones seems to achieve such a high success rate of infection anyway?
Today's international script kiddies are empowered with localized versions of sophisticated web malware exploitation kits courtesy of Russian hackers, seems like globalization in action. The Neosploit Team may be abandoning support for their malware kit, but they're so not abandoning the current malware campaigns they manage using it.