Threema joins the ranks of E2EE chat apps that support encrypted video calls

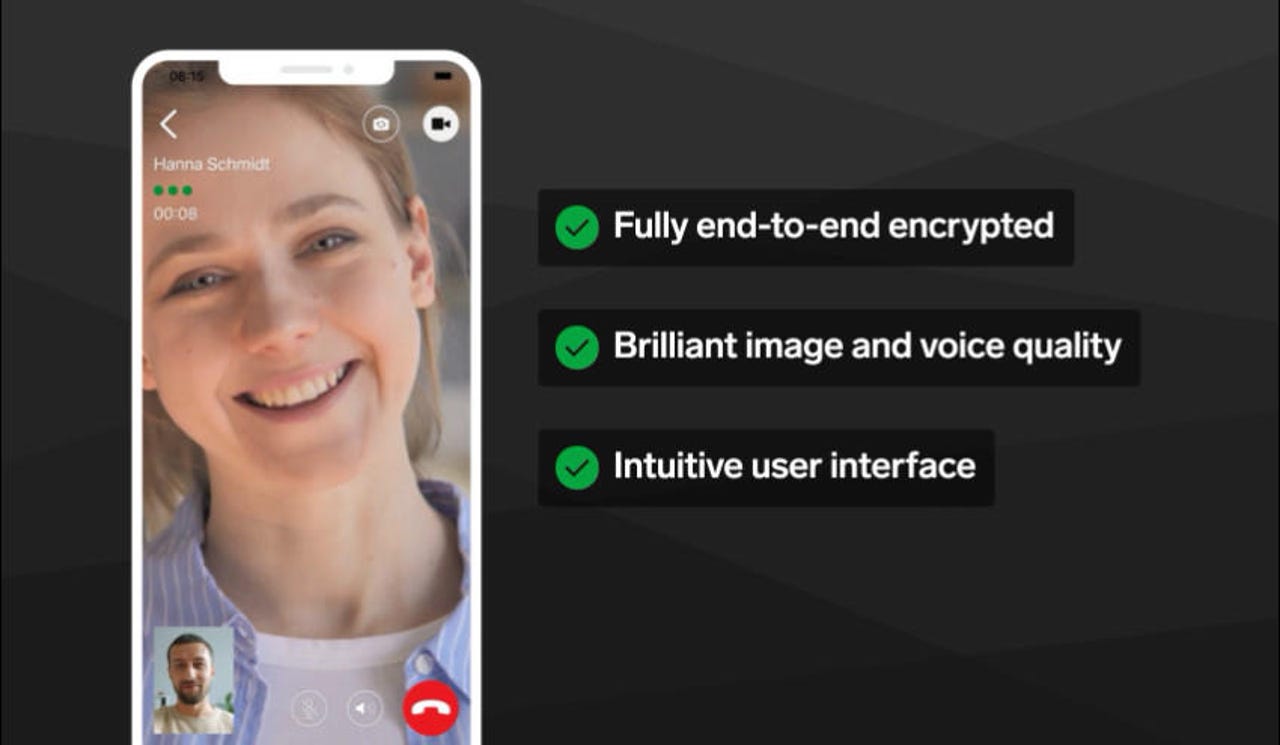
Secure instant messaging app Threema has rolled out support this week for end-to-end encrypted (E2EE) video calls for its mobile applications.
Monday's update brings the app in the elite echelon of instant messaging applications that support secure encrypted video calls, together with the likes of Signal, WhatsApp, Wickr, and Wire.
Secure E2EE instant messaging applications still lacking support for this feature include Keybase (recently acquired by Zoom) and Telegram (which promised to have it ready by the end of 2020).
Threema said the new E2EE video calling feature is based on the WebRTC streaming protocol, the same technology that's also included with all major browsers today, and which is also at the base of many video streaming applications.
The difference is that Threema's implementation encrypts video calls between users' devices, using locally stored encryption keys.
This prevents man-in-the-middle attacks, where attackers might want to intercept calls.
Furthermore, the company said that its role in the E2EE video calls is also very limited. Threema says that all E2EE video calls are established directly between users, so traffic flows between the two users directly, without passing through Threema's servers.
The only situation when Threema servers are involved is when Threema users are starting a call with an unverified user, a special case where the connection is proxied through Threema's server in order to avoid having a verified user's IP address "exposed to dubious contacts."
Further, Threema also said that its new E2EE video calling feature doesn't only encrypt the video stream itself, but also its metadata; a design decision that blocks network observers from inferring any type of details about the video call.
Because companies like Threema are always looked at with distrust when announcing new encryption-based features, the Threema dev team also published the technical details behind the video calling feature's cryptography protocols.
Threema began working in its E2EE video calling feature last year, and the feature went into a beta testing phase in April. Users can update their Android and iOS apps to take advantage of the new feature.
Also today, the Threema team said that while working on the new feature, its developers also found and helped patch a major security issue in WebRTC.