TweetDeck wasn't actually hacked, and everyone was silly

Twitter's popular account management service TweetDeck got nailed when a hacker discovered and announced a cross-site scripting (XSS) vulnerability, one which replicated itself and became a comedy of errors — and misreporting.
Twitter temporarily disabled TweetDeck, which it owns, until the issue was fixed, but much ridiculousness had already been unleashed by one Twitter user, an Austrian teenager calling himself "Firo," who told CNN on Wednesday he was just trying to tweet out a pink "heart" icon.
TweetDeck wasn't hacked. It was already broken
The important thing to understand is that Firo didn't "hack" TweetDeck. The bug has always been in TweetDeck, and he was simply the first to publicly point it out.
Some news outlets reported that TweetDeck was hacked, while others have reported that there was a TweetDeck worm — a standalone malware program.
But TweetDeck was already broken, and it had been all along. It's highly likely that this vulnerability has been exploited quietly by others until now.
if you're using tweetdeck STOP. RT @sisiwei: Let's just say I can get your computer to do anything I can script in < 126 characters or so.
— dan sinker (@dansinker) June 11, 2014
While today's antics were harmless — though, embarrassing for some and inconvenient for others — other uses of this vulnerability until today were probably no so light-hearted.
The vulnerability allowed a TweetDeck user's Twitter timeline to tweet out JavaScript code that executed any prankster's messages as a pop-up dialog window, as well as replicating itself in retweets, which came with a little pink heart at the end.
Basically, TweetDeck's own Google Chrome browser plugin wasn't stripping out scripts that allowed a JavaScript execution. And as a result, over 83,000 Twitter users retweeted the script.
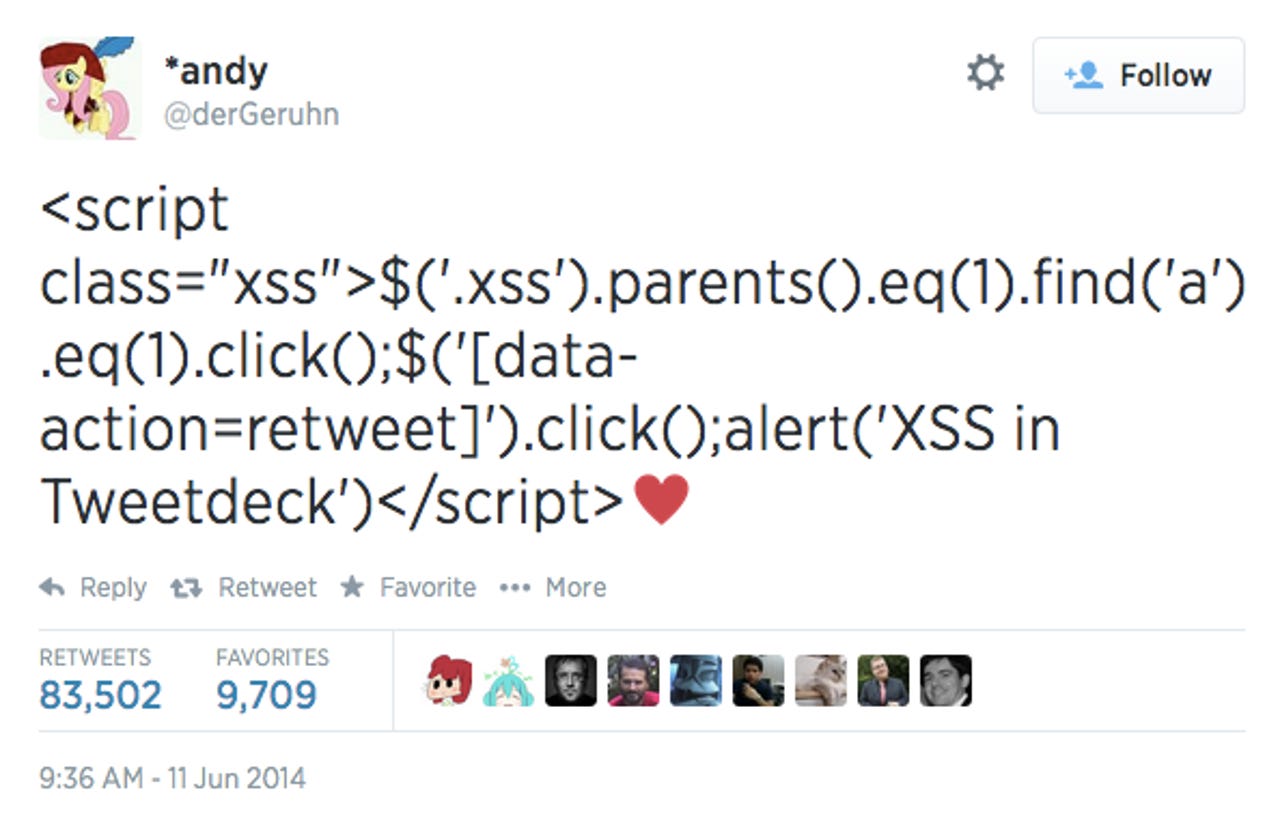
It also resulted in high-profile and verified accounts — estimated at 30,000 in total, including @NYTimes and @BBCBreaking — automatically retweet the bug, and so on.
Let the "lulz" begin
The opportunity for "lulz" was simply irresistible in security communities.
Tweetdeck announced a new "interactive tweet" feature today that opens up a new world of possibilities for what you can do with a tweet.
— Fake Infosec News (@FakeInfosecNews) June 11, 2014
The hacker who started this mess told CNN that he notified Twitter immediately.
However, by tweeting his experiment with the XSS bug live, along with a note saying, ("Vulnerability discovered in TweetDeck. \ o /"), he had also essentially notified anyone who also saw his tweets.
Others used the bug to begin pranking Twitter users. Messages in the pop-up dialogue box included a reference to the RickRoll meme, saying "NEVER GOING TO GIVE YOU UP, NEVER GOING TO LET YOU DOWN" while others got "HACKED," or the classic body part reference seen below.
“@addelindh: Tweetdeck XSS pic.twitter.com/OZpHcBaryQ” < looks like @miaubiz was there
— the grugq (@thegrugq) June 11, 2014
Tweetdeck is not fixed. pic.twitter.com/Zt0N5GkUFl
— Tyler Wilde (@tyler_wilde) June 11, 2014
Some used it as an opportunity to warn TweetDeck users:
Uhhh... what? #tweetdeck pic.twitter.com/rCiN4VeLLE
— Bruno Skvorc (@bitfalls) June 11, 2014
Many a truth was said in jest, some explained:
@addelindh vulnerability awareness through penis jokes - a well known educational concept.
— Guillaume (@gepeto42) June 11, 2014
Some sarcastically chided powerful Twitter accounts for running their accounts on autopilot — which in this instance, turns out to be an irresponsible practice:
Congratulations @BBCBreaking for not logging out, and sending a self-retweeting hack to 10.1m people (h/t @dracos): pic.twitter.com/S6haCHkfn8
— Tom Scott (@tomscott) June 11, 2014
Rapid7's global strategist Trey Ford provided greater detail to Business Insider into the TweetDeck bug:
"This vulnerability very specifically renders a tweet as code in the browser, allowing various cross site scripting (XSS) attacks to be run by simply viewing a tweet.
The current attack we’re seeing is a 'worm that self-replicates by creating malicious tweets. It looks like this primarily affects users of the Tweetdeck plugin for Google Chrome."
Twitter has resolved the issue and issued a patch, requesting that TweetDeck users log out and back in again to activate the fix.
Curious minds can investigate the diff below:
I extracted a diff from TweetDeck's XSS fix and found this. TL;DR emoji == evil, replace them w/ identity function pic.twitter.com/OAr5F4f0JU
— Yan (@bcrypt) June 11, 2014
Correction, Friday, June 13: This article has been updated to cite Florian (aka Firo) as the hacker who found the JavaScript bug, and not *andy as previously stated. We regret any confusion this may hav caused.