U.S. Emergency Alert System open to more 'zombie' hackers after accidental SSH key disclosure

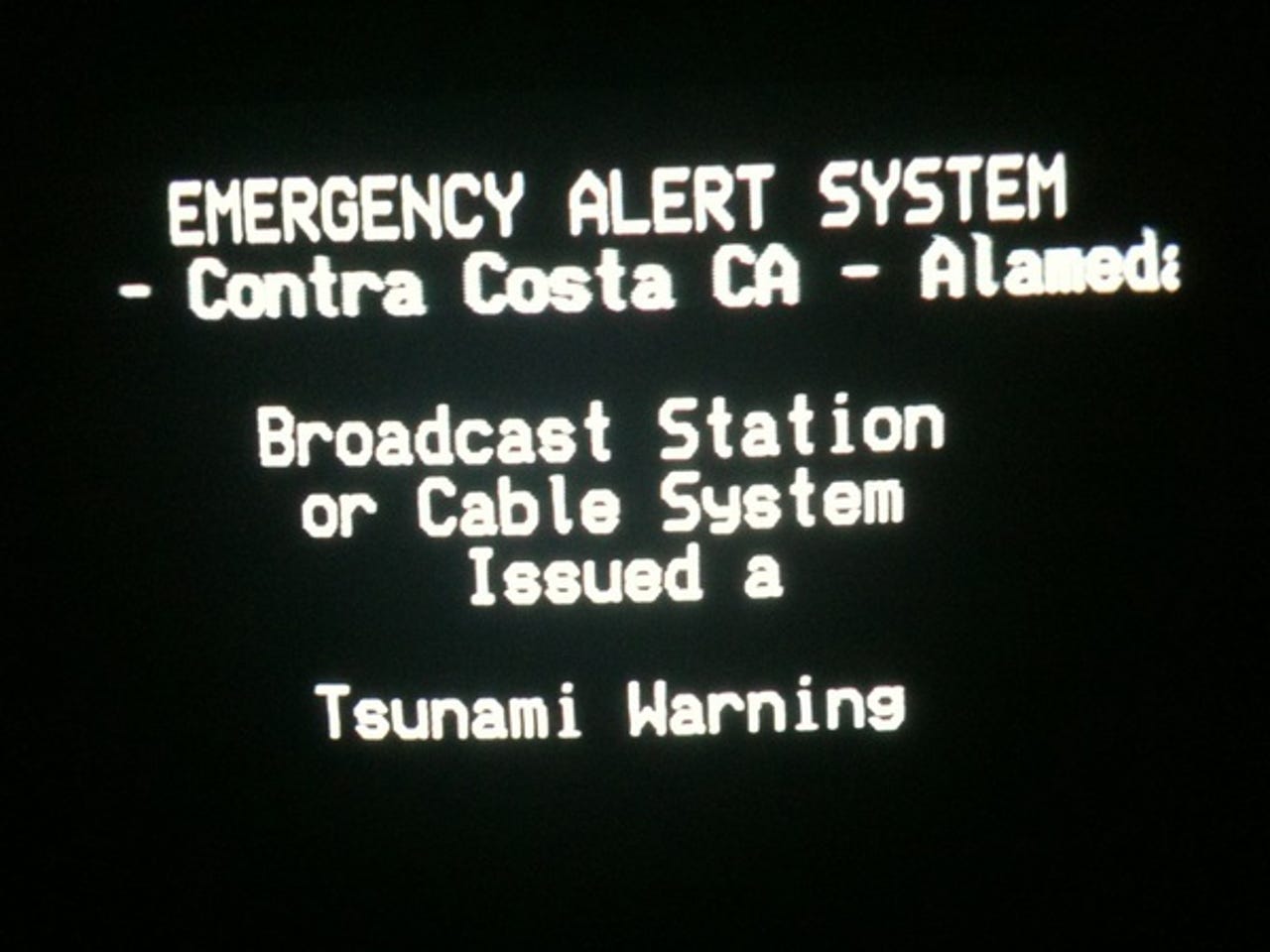
It's fair to say that should you see one of these warnings on your television as you're drinking your wake-up coffee, you're probably not going to have the best of days. Though, when you're told that the "bodies of the dead are rising from their graves and attacking the living," one might meet such reports — despite the official standing of such interruptions — with some skepticism.
That's exactly what happened in Montana in February, when hackers broke in to the U.S. Emergency Alert System (EAS), which interrupts television and radio broadcasts in times of local and national warnings. The default password wasn't changed, allowing the hackers to walk in to the Internet-connected appliance.
But a new security advisory warning warns that the EAS system is wide open to remote attacks by hackers, who can broadcast fake reports and materials.
The "critical" rating from IOActive [PDF] warns that DASDEC-I and DASDEC-II application servers, made by Digital Alert Systems, are left wide open to attackers, following a recent firmware update that also disseminated the secure-shell (SSH) key.
The key allows anyone with limited knowledge to log in at the root level of the server and "manipulate any system function," including browse key directories and access its peering arrangement.
From the advisory, an attacker who gains control of one or more DASDEC systems "can disrupt these stations' ability to transmit and could disseminate false emergency information over a large geographic area," which in some cases could be "forwarded to and mirrored" by other systems, spreading false information over a wider area.
The key is now in the public domain, and "cannot be easily removed except by a root privileged user on the server." The security advisory warns the maker of these appliances to "re-evaluate their firmware and push updates to all appliances."
Other advisories were published, including one by the U.S. CERT team, which notes that firmware version 2.0-2 resolves this vulnerability.