Use 1Password to mitigate damage from Gawker breach

If you're unaware, TechCrunch best describes the fiasco that surfaced on Sunday night:
In the modern media equivalent of a Greek myth, the Gawker empire was hit hard over the weekend when it was revealed that a hacker group had infiltrated its commenter database via a vulnerability in its source code, exposing the user names and encrypted passwords for over 1.3 million commenters. To further drive the moral of this story home, the group, which goes by the name Gnosis, pulled a dictionary attack and unencrypted about 188K of the easiest ones like “password” or “qwerty” releasing the whole database and source code package in a torrent on Pirate Bay.
The blog network which includes major sites like Gawker, Gizmodo, Jalopnik, Jezebel, Kotaku, Lifehacker, Deadspin, io9 and Fleshbot was believed to be targeted by hacker group Gnosis because of Gawker’s public flaunting of 4Chan. You can read all the blow-by-blow details on Mediaite.com.
1) Determine if you've been victimized.
If you've posted a comment on any of the Gawker media sites above then you're probably one of the 1.3 million affected. If you password is longer than six characters (note to self) then you're ok. However, 188,000 commenters with passwords of six characters or less were decrypted by a brute-force dictionary attack (second note to self) and posted in a tidy torrent file for anyone to download. You can find out if you're login credentials were exposed by searching for your email address or username in this handy widget from Slate.
The risk isn't that someone's going to impersonate you and spam Gawker's comment system, it's that many stupid people use the same password to comment on blogs that they use on financial institution Web sites like Bank of America, Wells Fargo, PayPal and Paytrust. Cyber thieves are already trying the exposed accounts on other systems. Currently, they're using hacker Gawker accounts to tweet about Acai Berries.
2) Take action.
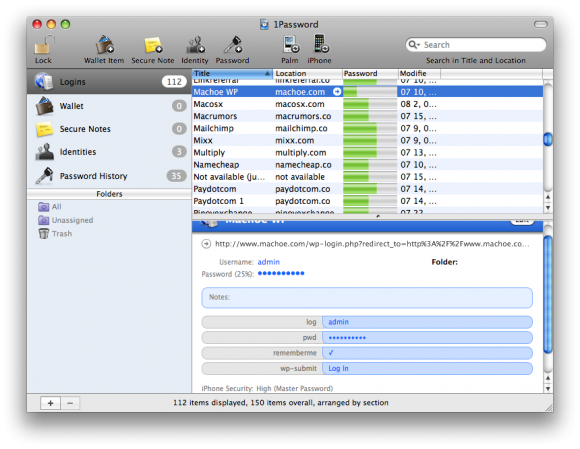
If you have been victimized and you use 1Password you can make quick work of finding all the sites where you used the exposed credentials and help you change all of them relatively painlessly. Simply create a New Smart Folder in 1Password with the username and password in question, then methodically go down the found list and change all your passwords at the affected sites. While you're at it, use 1PW's strong password generator to create a new and unique password for each site.
If you did fall prey to the attack, don't fret. Just get smart and learn from your mistakes. Let software (like 1PW) help keep your passwords secure and -- repeat after me -- use only strongpasswords.