WannaCry reportedly hitting speed cameras in Victoria

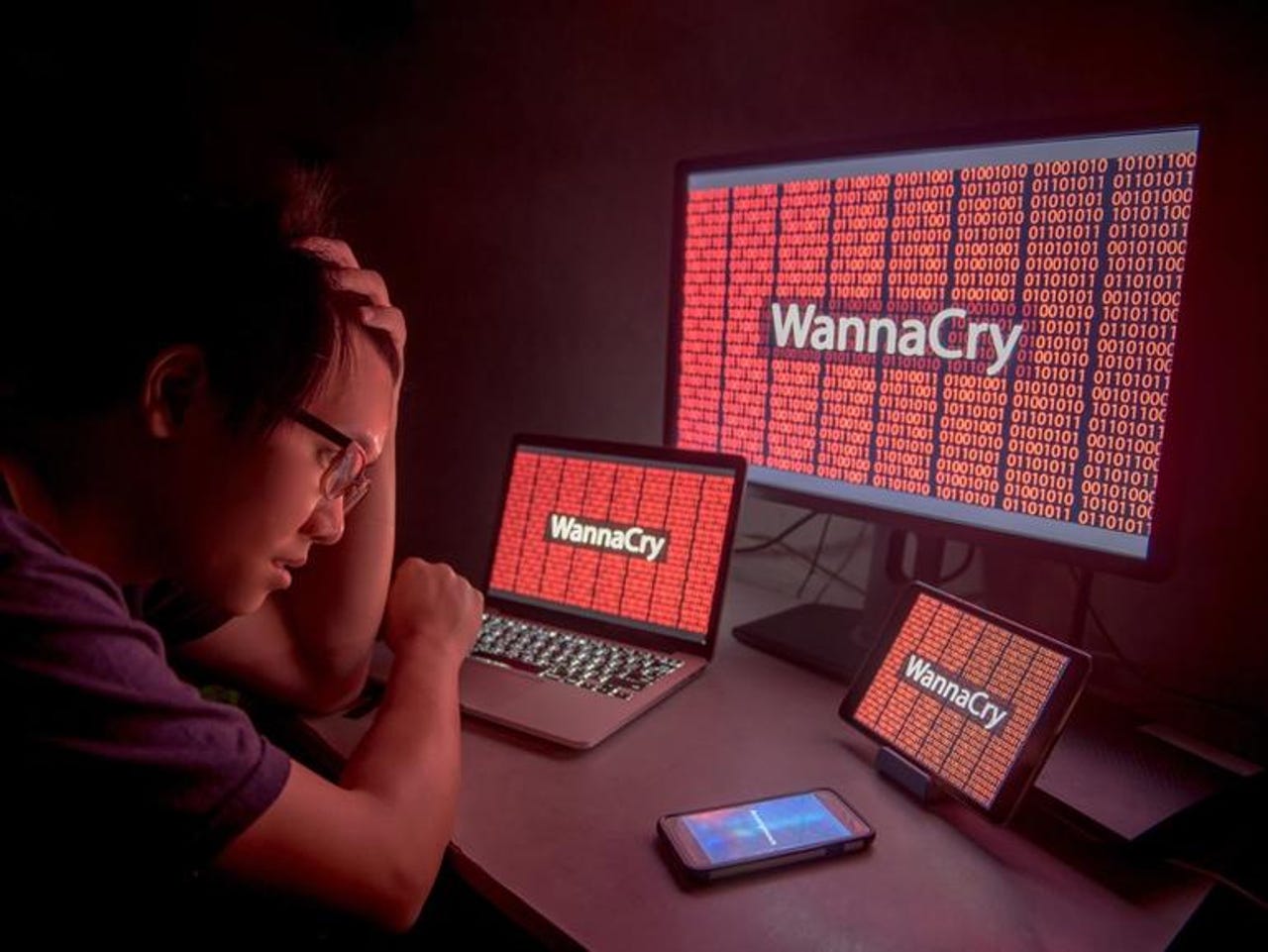
The WannaCry ransomware that claimed hundreds of thousands of victims across 150 countries has hit speed and intersection cameras in Victoria, Radio 3AW has reported.
According to the radio station, 55 cameras in the state belonging to vehicle monitoring and enforcement service Redflex were infected with the ransomware after a rogue USB was inserted by someone performing maintenance on the now-infected cameras.
It is understood that the infection came as a result of "human error" rather than a targeted attack aimed at holding the Australian state to ransom.
The cameras are not connected to the internet, however, which means the ransomware has not been spread throughout the field, 3AW told its listeners on Thursday.
Redflex Traffic Systems -- which has its Australian head office located in Melbourne -- said it has a patch to fix the infected devices, according to the report.
"The department is in the process of removing the virus from the affected cameras. The remaining sites will be rectified in the next couple of days," a Justice and Regulation spokesperson is quoted as telling 3AW.
"The software virus has not impacted the accuracy of the camera system. All infringements during this period have been captured correctly, and no infringements have been affected by the virus."
WannaCry has caused the cameras to intermittently reboot, however,
While WannaCry hit over 300,000 organisations around the world, only a tiny percentage of victims have given in to the demands of hackers.
According to a bot watching the Bitcoin wallets tied to the ransomware attack, just 335 payments had been made as of June 20, 2017, netting the perpetrators 51.9 bitcoins -- a figure worth approximately $140,326.
It is unknown how long the cameras have been infected and how long Redflex has known about the issue.
ZDNet has reached out to the local arm of Redflex Traffic Systems for comment.