Who keeps failing their FISMA compliance?
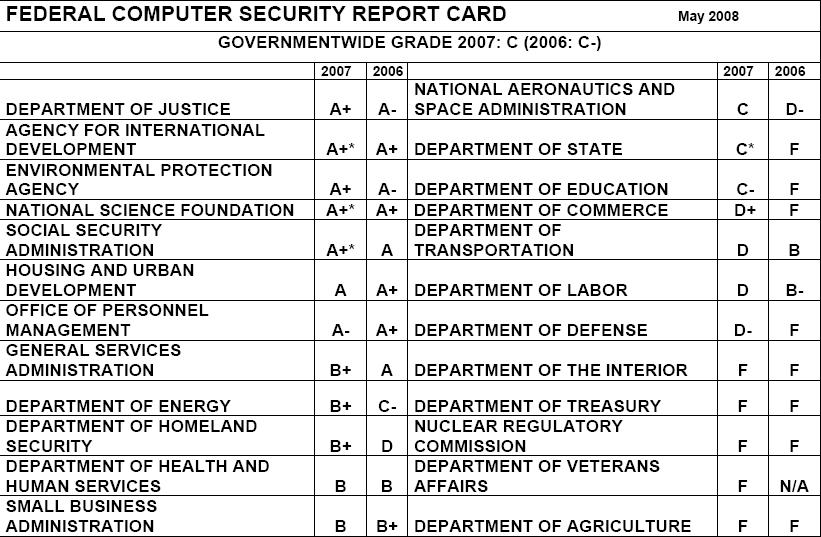
The recently released U.S Federal Computer Security Report Card for 2008, indicates that several critical to national security departments continue failing to implement the Federal Information Security Management Act (FISMA).
From a cyber espionage perspective, the lack of prioritization of departments that must be audited first, often results in anecdotal cases.
Case in point, who cares if the Environmental Protection Agency scored A+ when the Nuclear Regulatory Commission and the Department of the Interior have been failing for 2006 and 2007 altogether? And isn't it disturbing to know that Housing and Urban Development scores higher than the Department of Defense? Secured by default through the use of (outdated) information security acts isn't perfect, and the results of such assessments shouldn't be taken for granted. That's mostly because the threatscape and the dynamic development of a department's infrastructure is prone to grow faster than a standard can keep up with the threats and insecurities posed by the new technologies. Here are some more opinions about FISMA's applicability in real-life threatscape situations :
“Some argue that FISMA does not adequately measure information security,” said Tim Bennett, president at the Cyber Security Industry Alliance. “A high FISMA grade doesn’t mean the agency is secure and vice versa. That is because FISMA grades reflect compliance with mandated processes: they do not, in my view, measure how much these process have actually increased security.” Despite an obvious need to improve security, no one suggested scrapping FISMA.
“The bill itself is fine with the way the framework is set up,” said Karen Evans, OMB’s administrator for electronic government and IT. FISMA is a tool that provides metrics for reporting efforts, and with independent IG evaluations it does not rely on self-reporting. Whether or not it is a paperwork drill or a genuine enhancement to security “depends on how the agency goes about doing the work.”
FISMA is currently revisited, and therefore an updated framework is definitely in the works.