Who wants to be a hacking millionaire?

Google is well known for rewarding those that provide information that will help the company make its products more secure, but after no one stepped up to try their hand at a US$20,000 hacking challenge last year, Google has upped the ante to up to US$1 million.
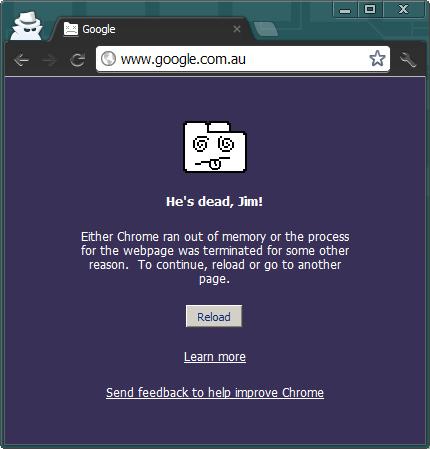
(Screenshot by Michael Lee/ZDNet Australia)
Last year, Google featured in the Pwn2Own contest held by TippingPoint's Zero Day Initiative (ZDI) team. The web giant submitted its Chrome web browser for scrutiny, offering hackers US$20,000 and a Google Cr-48 Chromebook if they were able to escape the browser's built-in sandbox by exploiting Google's own code.
After criticisms that this unrealistically limited the scope of the challenge, the second and third days of the challenge were made less restrictive with ZDI additionally offering US$10,000 if hackers used non-Google code to break out of the sandbox, matched by Google's own contribution of US$10,000.
However, no one was able to successfully demonstrate an attack and the prize money went uncollected.
As a result, Google has increased the kitty this year to up to US$1 million and further opened up the scope of the challenge.
At the CanSecWest security conference in Vancouver, British Columbia, next week, Google will award the full US$20,000 to successful hackers, even if they use non-Google code or if the bugs they submit are not specific to Chrome.
"Although not specifically Chrome's issue, we've decided to offer consolation prizes because these findings still help us toward our mission of making the entire web safer," Google wrote on the Chromium blog.
For bugs that exploit Chrome by using non-Google code as a stepping stone, Google will reward hackers with US$40,000. As an example, the company said this could include a WebKit bug (which forms part of Chrome) combined with a Windows bug.
Google will reward the purists that manage to exploit Chrome using only Google's own code with US$60,000.
Google will reward hackers for multiple bugs in each category, up to a maximum of US$1 million, and provide all winners with a Chromebook.
While last year's competition was run through Pwn2Own, Google has decided to go it alone after discovering that this year's competition rules had changed. According to Google, contestants would not be required to reveal the full exploit or even what bugs were used to penetrate Chrome. This would hinder the ability of Google to patch and improve its product.
In addition, Google has pledged to send all non-Chrome bugs it receives to the appropriate vendor.
Hunting for bugs has become a way for some hackers to legitimately earn money on the side. One such hacker is Sergey Glazunov, who to date has been rewarded with close to US$80,000 from Google for submitting bugs through Google's Chromium Security Rewards Program. In many cases, hackers have used their skills for the benefit of others, donating the reward money to charity. In recognition of this, Google often increases the donated amount beyond the standard bounty.