Why one Norwegian security firm is stepping into international encryption limelight

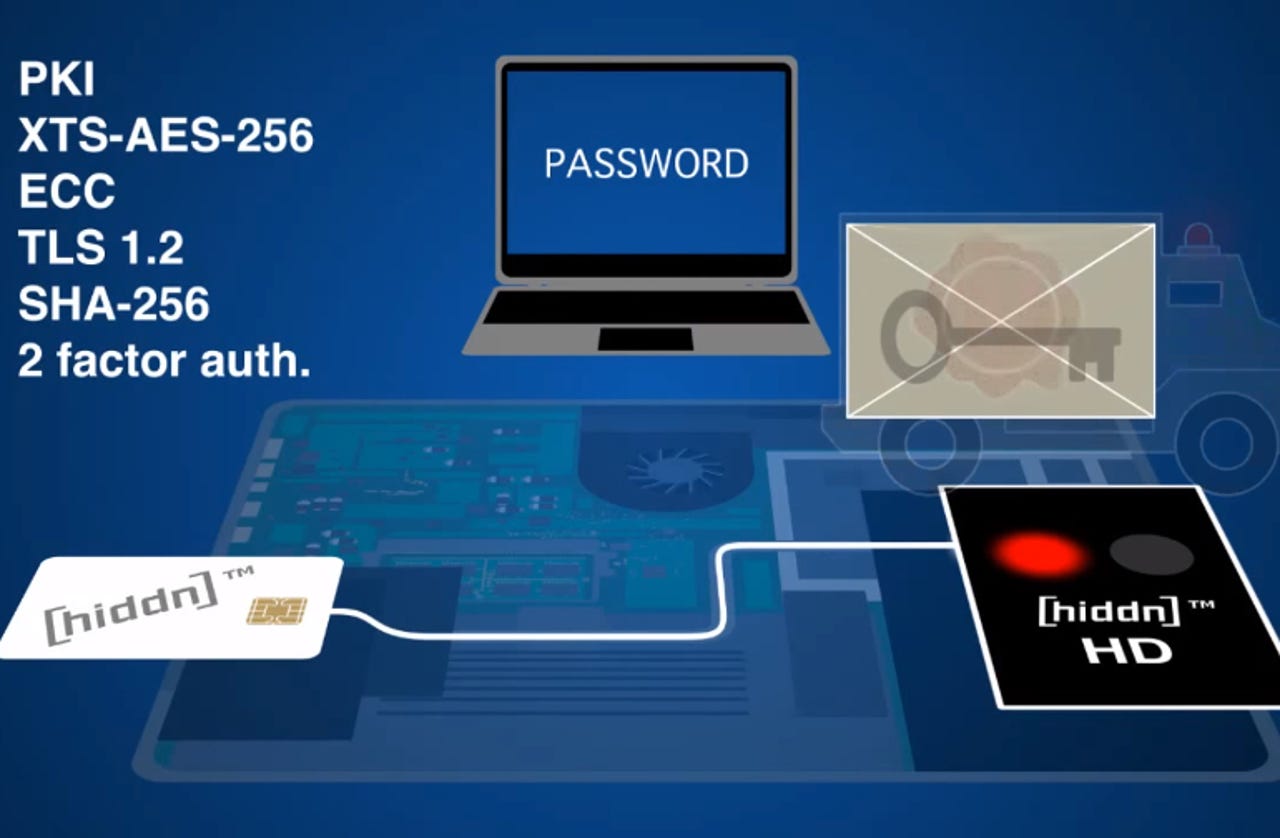
Hiddn Security provides devices with an encrypted SSD and a smartcard containing the keys.
Norwegian security vendor Hiddn Security has just had a couple of international breakthroughs. First, its technology has been chosen by the Netherlands government to encrypt laptops and desktop PCs in the country's public sector.
And second, the American National Institute of Standards and Technology (NIST) awarded the company FIPS 140-2 Level 3 certification, which could open the door for its products to be used by US government and military markets.
"The FIPS 140-2 Level 3 certification is probably among the highest quality-assurance hurdles we'll ever have to clear. We've worked many years for this, and now users can carry their PCs and USB sticks around in a secure manner. This opens new, exciting possibilities," Hiddn Security CEO Gudmundur Einarsson said in a statement.
Hiddn's products and patented technology revolve around encryption. In a PC or laptop, the Hiddn product is a drop-in replacement for a device's internal disk, an encrypted SSD, currently with 128GB, 256GB or 512GB of storage capacity.
Integrated on this encrypted disk unit is a tamper-proof encryption chip, which provides strong AES 256 hardware-based encryption.
Together with the SSD, the company also provides a smartcard, where the encryption keys are stored, external to the machine itself, so there are no keys stored on the system while powered off. This card, in conjunction with a pass phrase, provides the solution with a two-factor authentication scheme.
All the data on the SSD is encrypted, included master boot record, or MBR, operating system and temporary files. Thus, the encryption is the outermost layer of the system, and no processing will happen until the SSD has received its encryption keys for use. This step happens once the user has provided the password, and only after this has happened will the system boot up.
When the system is shutting down, it erases the encryption keys from the system, thus rendering it impossible to start up again, until the user provides the smart card with the keys, as well as the correct pass phrase.