Zero Days, film review: Stuxnet, secrecy and the new era of cyber war

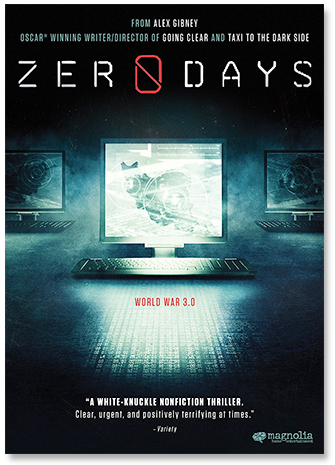
Zero Days • Written and directed by Alex Gibney • Magnolia Pictures • 116 minutes
There's a simple but obvious principle that makes cyber attacks different from nuclear attacks: if we can do it to them, they can do it to us. Very few countries would have had the expertise to write Stuxnet, the malware that was discovered to be infecting Iranian uranium centrifuges in 2010. But once it's out there...it can be copied and reused by any country that cares to act like a 'script kiddie'.
According to the evidence presented in Alex Gibney's film Zero Days, this wasn't the risk US President George W. Bush was focused on in 2005. At that time, the world looked like this to him: either Israel would attack Iran with the US's help, or Israel would attack Iran on its own and the US would be forced to join the fray. What if there were an alternative that would knock out Iran's nuclear program without anyone knowing?
So much we already knew from Kim Zetter's detailed 2013 account, Countdown to Zero Day: Stuxnet and the Launch of the World's First Digital Weapon. Three years later, however, Gibney couldn't get this question out of his head: why to this day has no-one admitted responsibility?
Accordingly, the movie opens with a montage of many of his sources explaining that they "can't talk about it" beyond what's already known about the malware and how it works. But Gibney eventually found a small band of angry NSA operatives who agreed to allow their comments to be pooled and presented by an actress.
An act of cyber war
The gist: in 2009 the Israelis changed the code to make it spread more aggressively, with the result that the malware got noticed. The result, ultimately, is that the project failed on all counts: the malware got out; the countries responsible were identified; and it didn't stop the Iranian nuclear program, but just delayed it for a year or so. If the positions had been reversed, the US would certainly have viewed the attack as an act of cyber war and sought to retaliate. Cyber attacks that interfere with physical systems -- railroads, power grids, gas pipelines -- do not stay safely in cyberspace: instead, real people die real deaths.
Many of Gibney's sources agree on one thing: the secrecy should end. Nuclear, biological, and chemical weapons all looked equally difficult to regulate at first, but over a few decades of negotiation ways were found to agree on a doctrine -- principles to govern their use. The same, they argue, must happen with cyber weapons.
Unfortunately the public debate that's needed is not possible as long as the entire subject is, as former CIA director Michael Hayden puts it in the film, "hideously overclassified". He has a simple explanation for why this is: these weapons come out of the secretive intelligence community rather than military operations. The NSA-representing actress concludes: "We should talk about it."
Read more book and film reviews