ZeuS crimeware variant targets Symbian and BlackBerry users
A ZeuS crimeware variant known as ZeuS Mitmo, has began targeting the two-factor authentication solution offered by the Polish ING bank.
UPDATE: Devices running Windows Mobile are also targeted.
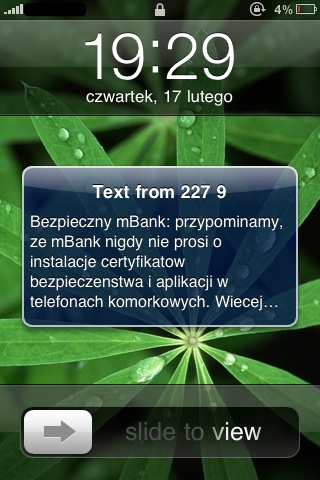
The variant, currently targeting Symbian and BlackBerry users works as follows. Upon successful infection, the crimeware injects a legitimately looking field into the web page. The aim is to trick end users into giving out their mTANs, which stands for mobile transaction authentication numbers. Now that the gang has obtained access to their cell phone number, including the type of the device, a SMS is sent back to the victim with a link to a mobile application targeting either Symbian or BlackBerry devices.
See also:
- Modern banker malware undermines two-factor authentication
- Report: ZeuS crimeware kit, malicious PDFs drive growth of cybercrime
According to the security researcher Piotr Konieczny, the reason why Apple's iPhone was excluded is due to the fact that Apple has more control over the Apple Store, compared to Symbian or RIM (Research in Motion).
These relatively sophisticated attempts on behalf of cybercriminals, wouldn't be possible to execute if the user didn't get infected in the first place.
As always, users are advised to use least privilege accounts, browse the web in isolated environment, and ensure their hosts are free of outdated 3rd party software, browser plugins or OS-specific flaws.