Canonical GitHub account hacked, Ubuntu source code safe

The GitHub account of Canonical Ltd., the company behind the Ubuntu Linux distribution, was hacked on Saturday, July 6.
"We can confirm that on 2019-07-06 there was a Canonical owned account on GitHub whose credentials were compromised and used to create repositories and issues among other activities," the Ubuntu security team said in a statement.
"Canonical has removed the compromised account from the Canonical organisation in GitHub and is still investigating the extent of the breach, but there is no indication at this point that any source code or PII was affected," it said.
"Furthermore, the Launchpad infrastructure where the Ubuntu distribution is built and maintained is disconnected from GitHub and there is also no indication that it has been affected."
The Ubuntu security team said it plans to publish another public update once it finishes its investigation into the incident, and after it carries out an audit and carries out any other needed remediations.
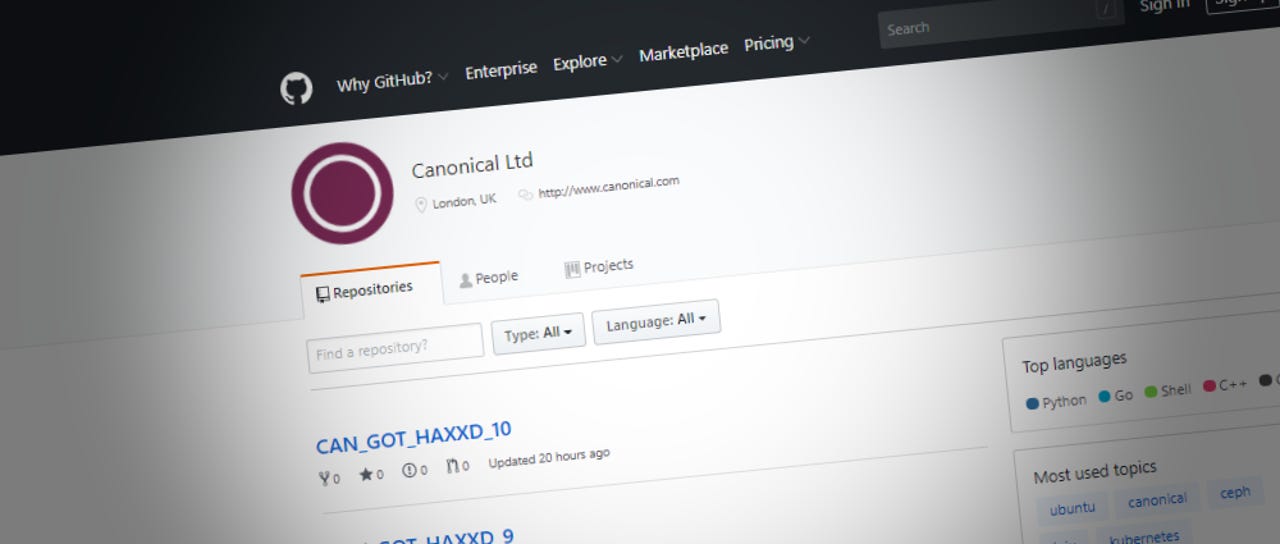
According to a mirror of the hacked Canonical GitHub account, the hacker created 11 new GitHub repositories in the official Canonical account. The repositories were empty.
Two days before the incident, cyber-security firm Bad Packets detected internet-wide scans for Git configuration files. Such files can often contain credentials for Git accounts, like the ones used to manage code on GitHub.com.
I'm interested if there's any correlation with the recent mass scanning for exposed git config files. https://t.co/ckGt158CXc
— Bad Packets Report (@bad_packets) July 7, 2019
Canonical hacked in the past, loads of times
This weekend's Canonical security incident is not the first one through which the company goes through.
The official Ubuntu forums had been hacked on three different occasions -- in July 2013, in July 2016, and December 2016. Hackers stole the details of 1.82 million users in the July 2013 incident, the data of two million users in July 2016, and the forum was only defaced in the third incident.
A malicious Ubuntu package containing a cryptocurrency miner was also found on the official Ubuntu Store in May 2018.
But all these Ubuntu security incidents pale in comparison to what happened to Linux Mint in February 2016 when hackers breached the site and tainted the operating system's source code with a backdoor. A similar incident happened to the Gentoo Linux distro in June 2018 when hackers gained access to the distro's GitHub repo and poisoned some GitHub downloads with an OS version containing a backdoor.
Currently, this weekend's incident appears to be benign. If the hacker had added malicious code to Canonical projects, then he wouldn't have drawn attention to himself by creating new repositories in the Canonical GitHub account.
10 super sweet laptops that come with Linux pre-installed
Related cybersecurity coverage:
- US Cyber Command issues alert about hackers exploiting Outlook vulnerability
- Tor Project to fix bug used for DDoS attacks on Onion sites for years
- D-Link to undergo security audits for 10 years as part of FTC settlement
- UK ISP group names Mozilla 'Internet Villain' for supporting 'DNS-over-HTTPS'
- Croatian government targeted by mysterious hackers
- US wants to isolate power grids with 'retro' technology to limit cyber-attacks
- iOS developers still failing to build end-to-end encryption into apps TechRepublic
- The best identity theft monitoring services for 2019 CNET