First IPv6 Distributed Denial of Service Internet attacks seen

The clock is running out on IPv4 on the Internet, but even so the next generation of Internet traffic protocols, IPv6, is being adopted very slowly. But, it seems IPv6 is finally making it to broad acceptance. Arbor Networks reports that the "latest milestone in IPv6 development: the first observations of IPv6 Distributed Denial of Service (DDoS) attacks.
This can only be happening because the number of IPv6-based end-points have grown large enough that possible injection points for IPv6-based attacks is now large enough for attackers to use it. At the same, time they're finding targets on the IPv6-enabled Internet worthy of the effort needed to craft and execute attacks.
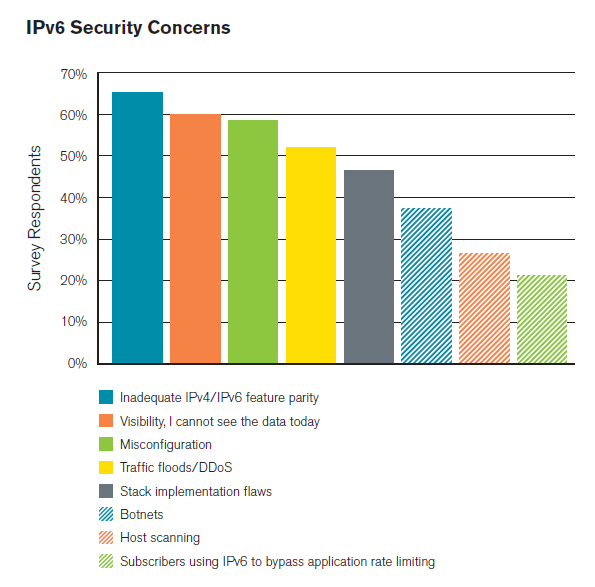
We could have expected this. Besides human nature, Arbor Network's Worldwide Infrastructure Security Report had predicted IPv6 DDoS attacks. "This is a significant milestone in the arms race between attackers and defenders," stated the report. "We believe that the scope and prevalence of IPv6 DDoS attacks will gradually increase over time as IPv6 is more widely deployed." And, now, they've started.
According to Arbor Networks' Senior Software Quality Assurance Engineer Bill Cerveny, "Gone are the days when a network failure on the IPv6 Internet would be ignored and undetected because, well, no one noticed (or cared). … The same thing that has made the IPv6-enabled Internet 'valuable' has also made it an increasingly valuable venue for attacks. While the frequency of attacks is relatively modest on IPv6 today, we expect that accelerated adoption will be followed in-kind by an accelerated pace of attacks."
Another problem with these attacks is the myth that IPv6 is somehow more secure than IPv4. Indeed, Cerveny cites the sad case of a "network security group within a large US government organization went so far as to declare that since IPv6 is more secure, that the group decided to disband because they alleged that the next generation Internet protocol's inherent security capabilities would address their security concerns."
They were, and many people still are, so wrong about this. True, IPv6 incorporates Internet Protocol Security (IPsec), but by itself that doesn't buy you any more security. IPv6's header design also lends itself to better security since it can be used to provide to a cleaner division between encryption meta-data and the encrypted payload. In addition IPv6's huge address space can be deployed to scanning attacks harder by allocating random addresses within subnets. But, those are all matters on how you deploy IPv6. In and of itself, IPv6 won't make you any more secure than your childhood blue blanket.
As John Spence, of Nephos6, a cloud and IPv6 integration company, says : "Much of the early thinking around IPv6 security being better than IPv4 security was based on the RFC requirement that IPv6 stacks include IPsec support, but that is clearly too simplistic a view (and that strict requirement has been removed in recently-released RFC 6434." So, moving ahead you won't even be certain that IPsec will be in some IPv6 software and hardware.
Spence also observed that, "Because of the way IPv6 automatic transition mechanisms work hard to self-provision IPv6 services for dual-stack nodes (like Windows Vista or 7), IPv6 security vulnerabilities often exist in apparent IPv4-only deployments. I call these 'accidental IPv6 deployments' because they are by definition unmanaged, and latent - but still very exploitable. So, because of the state of IPv6 default configurations on many devices, even an organization without an IPv6 deployment needs an IPv6 security program."
This is all too true. Fortunately, this problem will soon be addressed by the Internet Engineering Task Force (IETF) draft, Implementation Advice on IPv6 Router Advertisement (RA) Guard, but this is still a work in progress.
For now, as the Washington DC beltway network company Tachyon Dynamics points out, operating systems "like Windows XP, 2003, Vista, 7, and 2008 don't set a limit on the amount of routers they like to listen to. Whereas in Linux and Mac they set their limit at right around 15. If there are more than 15 different RAs coming at them, they stop configuring the address and routes. This is not the case with Windows, and that's what the exploit in the awesome exploitation toolkit called flood_router6 inside The Hacker's Choice IPv6 tool-kit (THC-IPv6) shows. Flood_router6 will basically pound the subnet with millions of RAs with different IPv6 source addresses with different IPv6 prefixes. In a matter of seconds, you can turn a fully functioning Windows machine into a brick."
With trouble like that awaiting IPv6 systems on the Internet, it's clearly time to move from simply making sure that IPv6 works to making sure that IPv6 works securely on your networks. And, Windows users need to make certain that they're not already running IPv6 without even knowing they're making themselves vulnerable to IPv6 attacks.
Related Stories:
DDoS attacks spreading to IPv6 Internet
DDoS Attacks: Size doesn't matter
All IPv6 Internet, All the time
How Anonymous took down the DoJ, RIAA, MPAA and Universal Music Websites