Protecting against identity theft

perspective As our engagement with the online world grows, identity theft becomes a real and fast emerging threat. Anything from your name, address or credit card data can be stolen and used.
However, as a user, there are certain steps you can take to minimize the risk to yourself, your family and your business. Here are some basic and easy to implement best practices when navigating the World Wide Web.
Protect your PC
Update the virus protection software on your PC regularly. Do not open files from strangers, or company or e-mail IDs you don't know. Install and periodically update antispyware, virus protection and firewall software. There are several antivirus or spyware protection software from players such as Microsoft and McAfee.
Use firewall programs if your PC is connected to high-speed Internet connections like cable or DSL. If your computer is connected almost 24-hours a day to the Internet, it can invite unauthorized guests to hack into your system.
1. Think of a sentence that you can remember. This will be the basis of your strong password or pass phrase. Use a memorable sentence, such as "My son Mayank is three years old."
2. Check if the computer or online system supports the pass phrase directly. If you can use a pass phrase (with spaces between characters) on your computer or online system, do so.
3. If the computer or online system does not support pass phrases, convert it to a password. Take the first letter of each word of the sentence that you've created to create a new, nonsensical word. Using the example above, you'd get: "msmityo".
4. Add complexity by mixing uppercase and lowercase letters and numbers. For instance, in the pass phrase above, consider misspelling Mayank’s name, or substituting the number 3 for word three. So your password may become "msMi3yo".
5. Substitute some special characters. For instance, you can use symbols that look like letters, and other ways to make the password more complex: "m$Mi3yo.
6. Test your new password. Password Checker is a non-recording site that helps determine your password's strength as you type.
Be careful what you store on personal laptops as they can be stolen. If you have your personal banking and other information on your laptop, you run the risk of having your identity stolen along with your laptop.
Always log in and change passwords regularly
Make sure you use the password login feature on your computer. Remember your user IDs and passwords.
For passwords, do not use common things like any part of your birth date, spouse's name, child's name, address, etc. Names of children, family pets, favorite sports teams and the like are obvious choices and are easily guessed by thieves. Instead, use something unique that only you know. Use a combination of letters and numbers.
When engaged in online banking activity, avoid using short or obvious passwords. Many scammers now use dictionary attacks to obtain passwords, which will try every word in the dictionary until the password is cracked. If you use a common name or word, you are vulnerable.
Keep an eye on your e-mail
Keep a close watch on your e-mail--if you receive an e-mail asking you to give your personal information by clicking on a particular link, do not do so. Instead, go directly to the sender’s Web site by typing in the sender’s Web site address.
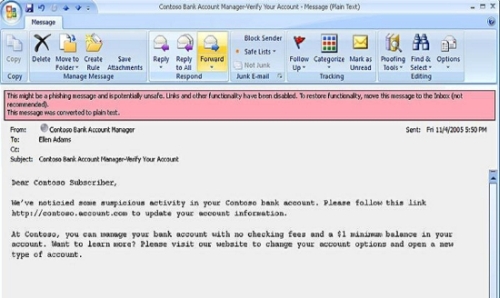
The image below is an example of how an e-mail, which looks genuine in nature, could be a case of phishing. In the example, Microsoft Outlook alerts a user that the e-mail content is suspect.
Be guarded against promotional offers
What sounds too good to be true, are generally too good to be true. E-mail scams such as quick money, gifts and lotteries, are indications of scams.
Adjust privacy settings
Never assume that the default settings are safe and make sure that you change them in such a way that you do not share any information inadvertently.
Sharing personal photographs
Make sure you are extra careful about sharing your personal moments on the net. There is always a possibility that they may be misused. A photograph can be easily morphed and could be used in places you would least like it to.
Use reputable and secure Web Sites for online transactions
The Internet has become one of the most popular fronts for scamming individuals for getting ID information such as by exploiting programming weaknesses found in Web sites. What appears to be a professional, secured Web site may in reality be a front used to collect personal information for identity theft purposes.
The basic rules here are to use a secure Web browser and check the Web site’s business reputation.
Sanjay Bahl is the chief security officer at Microsoft India.