'Psyb0t' worm infects Linksys, Netgear home routers, modems

It was first observed infecting a Netcomm NB5 modem/router in Australia.
Members of the website DroneBL, a real-time IP tracker that scans for and botnets and vulnerable machines, came to the conclusion that the "psyb0t" (or "Network Bluepill") botnet was a test run to prove the technology. After the botnet's discovery and public outing, the botnet operator swiftly shut it down, APC reports.
[Read more: Stealthy router-based botnet worm squirming]
However, the most recently discovered generation (dubbed 'version 18' in the code) targets a wide range of devices, and contains the shellcode for over 30 different Linksys models, 10 Netgear models, and 15 other models of cable and DSL modems, APC reports. It did not specify which models.
APC:
A list of 6000 usernames and 13,000 passwords were also included, to be used for brute force entry to Telnet and SSH logins which are open to the LAN and sometimes even the public WAN side of the routers. Generally, routers do not lock a user out after a number of incorrect password attempts, making brute force attacks possible.
According to DroneBL, any router that uses a MIPS processor and runs the Linux Mipsel operating system (a simple operating system for MIPS Processors) is vulnerable if they have the router administration interface, or sshd/telnetd in a DMZ, with weak username/passwords. DroneBL noted this includes devices flashed with the open-source firmwares openwrt and dd-wrt, and the group also said that other routers may be vulnerable, as it had observed the bot running on routers based on the Vxworks operating system.
Clearly, exploiting a home network -- which are growing in popularity -- has its benefits: they rarely power down, and a router attack enables hackers to exploit a network with greater levels of stealth, since there's no affect on individual PCs on the network, APC writes.
In fact, the staff of DroneBL wrote that the exploit is very difficult to detect, and the only way to discover it is to monitor traffic going in and out of the router itself --beyond the reach of desktop computer software.
In the past, exploits on professional-grade Cisco routers were easier to detect, as Cisco provides dedicated ports for connecting to the router, monitoring internal performance and configuring them. However, the vast majority of home routers sacrifice these features for the sake of cost savings.
DroneBL says that the botnet is capable of scanning for vulnerable PHPMyAdmin and MySQL installations, and can also disable access to the control interfaces of a router, (meaning a factory reset is necessary to clear the worm).
DroneBL was successful in shutting down the Command & Control channel that the botnet utilized, and the DNS that was hosted with afraid.org was also nullrouted. The Command & Control channel is now defunct, but at the height of its penetration, the botnet was suspected to control 100,000 hosts.
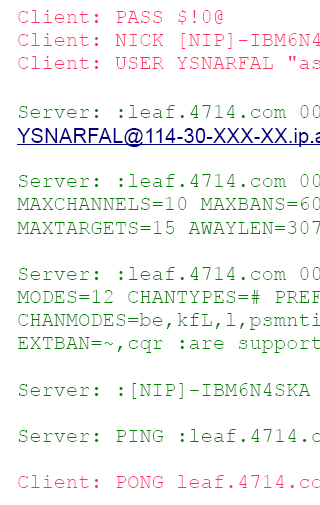
Worse, the author of the botnet claimed to have infected 80,000 routers at one point while chatting anonymously on an IRC channel.
WHAT DEVICES ARE AFFECTED
We don't know. There are so many devices out there that we could not possibly know.
Your best bet would be to take action to upgrade the device firmware and secure any passwords if there is concern that the device may be vulnerable. Such actions will help to avoid exploitation by the worm.
WHAT TO DO
According to DroneBL:
Ports 22, 23 and 80 are blocked as part of the infection process (but NOT as part of the rootkit itself, running the rootkit itself will not alter your iptables configuration).
If these ports are blocked, you should perform a hard reset on your device, change the administrative passwords, and update to the latest firmware. These steps will remove the rootkit and ensure that your device is not reinfected.