Cybersecurity reads for every hacker's bookshelf

A Bug Hunter's Diary: A Guided Tour Through the Wilds of Software Security
Author: Tobias Klein
It isn't all about black-hat activities -- the white-hat work can be exciting, too. In A Bug Hunter's Diary, security expert Tobias Klein describes how he became involved in tracking down exploits and vulnerabilities, how vendors view the bug bounty industry, and all of the happiness and frustration which is part of the job.
The Art of Intrusion: The Real Stories Behind the Exploits of Hackers, Intruders and Deceivers
Author: Kevin Mitnick
In The Art of Intrusion, Kevin Mitnick tells us through real-life examples how hacking is not just about breaking into large corporations, but also infiltrate other areas of live. Tales include how a group of friends reverse-engineered slot machines to win big and how computer hacking entered a Texas prison.
Black Hat Python: Python Programming for Hackers and Pentesters
Author: Justin Seitz
Python is a programming language which takes hackers beyond the basics and into the realm of the professional security expert. Black Hat Python is an excellent way to start by fully investigating how the language can be used for both the light -- and dark -- sides of hacking.
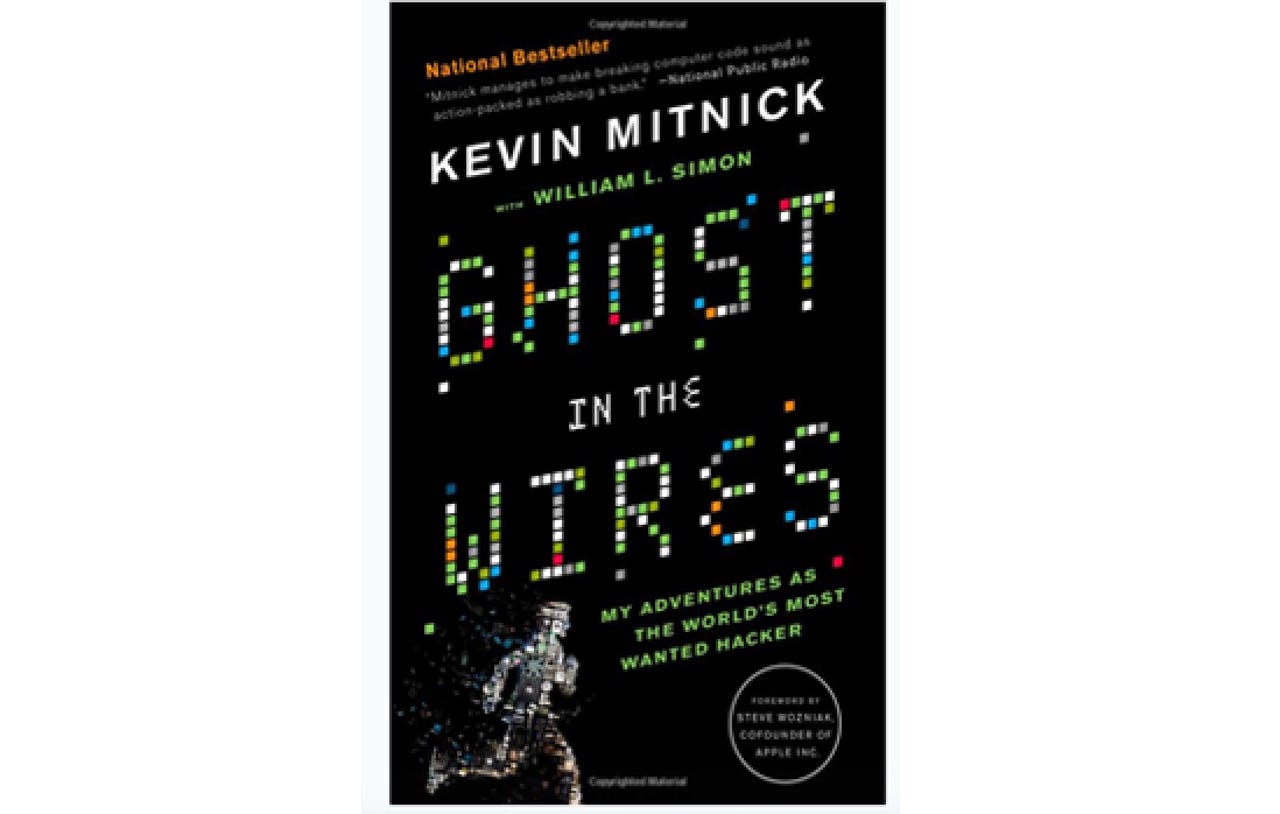
Ghost in the Wires: My Adventures as the World's Most Wanted Hacker
Author: Kevin Mirnick
Kevin Mirnick's autobiography, Ghost in the Wires: My Adventures as the World's Most Wanted Hacker, speaks about the now-security consultant's time as a hacker led FBI agents a merry chase in his capture after hacking into some of the world's largest firms.
The Hacker Playbook 2: Practical Guide To Penetration Testing
Author: Peter Kim
For a practical guide to penetration testing right from the beginning, The Hacker Playbook is likely not just to appeal to beginners, but to professionals who might appreciate a reference guide to hand. The book covers everything from network infiltration to sandboxing, how to circumvent antivirus software and what damage can be caused when a system is breached.
Secrets and Lies: Digital Security in a Networked World
Author: Bruce Schneier
Bruce Schneier's Secrets and Lies: Digital Security in a Networked World focuses on how networks operate and the security themes and concepts important in today's world; especially useful for those in the field, and very interesting to any tech enthusiast.
Countdown to Zero Day
Author: Kim Zetter
Countdown to Zero Day: Stuxnet and the Launch of the World's First Digital Weapon follows the discovery of Stuxnet, a worm designed to attack industrial sectors.
Ketter's story is a fascinating insight into how cybersecurity firms operate and introduces the reader to a number of key themes and topics which can be applied to the threat landscape today.
Data and Goliath: The Hidden Battles to Collect Your Data and Control Your World
Author: Bruce Schneier
Bruce Schneier's latest offering, Data and Goliath: The Hidden Battles to Collect Your Data and Control Your World, expands beyond network security to how our information is protected -- or left exposed. The main thrust of the book is a discussion of whether mass surveillance has a place in our world when it comes to security, and whether a balance between surveillance and privacy is possible.
We Are Anonymous
Author: Parmy Olson
Anonymous, a loose, global hacktivist collective which often targets groups online for political motives, has made the news many times in recent years. The group does not hide their activities but rather taunts their victims -- more often than not in order to promote a political message. If you would like to read up on them and their motives, We Are Anonymous is a fantastic read which follows the stories of four key members.
Kingpin: How One Hacker Took Over the Billion-Dollar Cybercrime Underground
Author: Kevin Poulsen
In this book, former hacker Kevin Poulsen takes us on a journey through modern-day cybercriminal rings and operations by following the story of an unlikely kingpin of the criminal world. If you want to know how a nondescript programmer managed to avoid authorities, hack fellow hackers and steal credit card data in the millions, check out the story.
Social Engineering: The Art of Human Hacking
Author: Kevin Mitnick
If you have an interest in social engineering -- the way that threat actors can utilize human behavior rather than software for their own ends -- this read is for you. The book delves into the science and behavioral patterns behind the concept, as well as ways to protect yourself from such manipulation.
Spam Nation
Author: Brian Krebs
Spam Nation: The Inside Story of Organized Cybercrime is a detailed look at spam and hacking operations today. Spam may be little more than a nuisance to most, but behind the scenes, such campaigns can mask vast underground cybercriminal operations, the flow of illegal cash, and the malware marketplace.
The Art of Invisibility: The World's Most Famous Hacker Teaches You How to Be Safe in the Age of Big Brother and Big Data
Author: Kevin Mitnick
In this book, former most-wanted hacker and now security consultant Kevin Mitnick takes us on a journey using real-life examples of how your data is collected -- and how to fight back. From staying invisible online to keeping your accounts safe, Mitnick offers a variety of tactics to keep your privacy intact.