Photos: How Google protects its datacentres

Behind the scenes peek inside search giant's datacentre
Google has opened the doors to one of its datacentres to show how it protects customer data.
A video released by Google on YouTube shows how it guards its datacentres using a range of security measures - from biometric IDs for staff to the complete destruction of defunct hard drives.
Google's datacentres handle information relating to everything from a search on Google.com to an e-commerce transaction through Google Checkout.
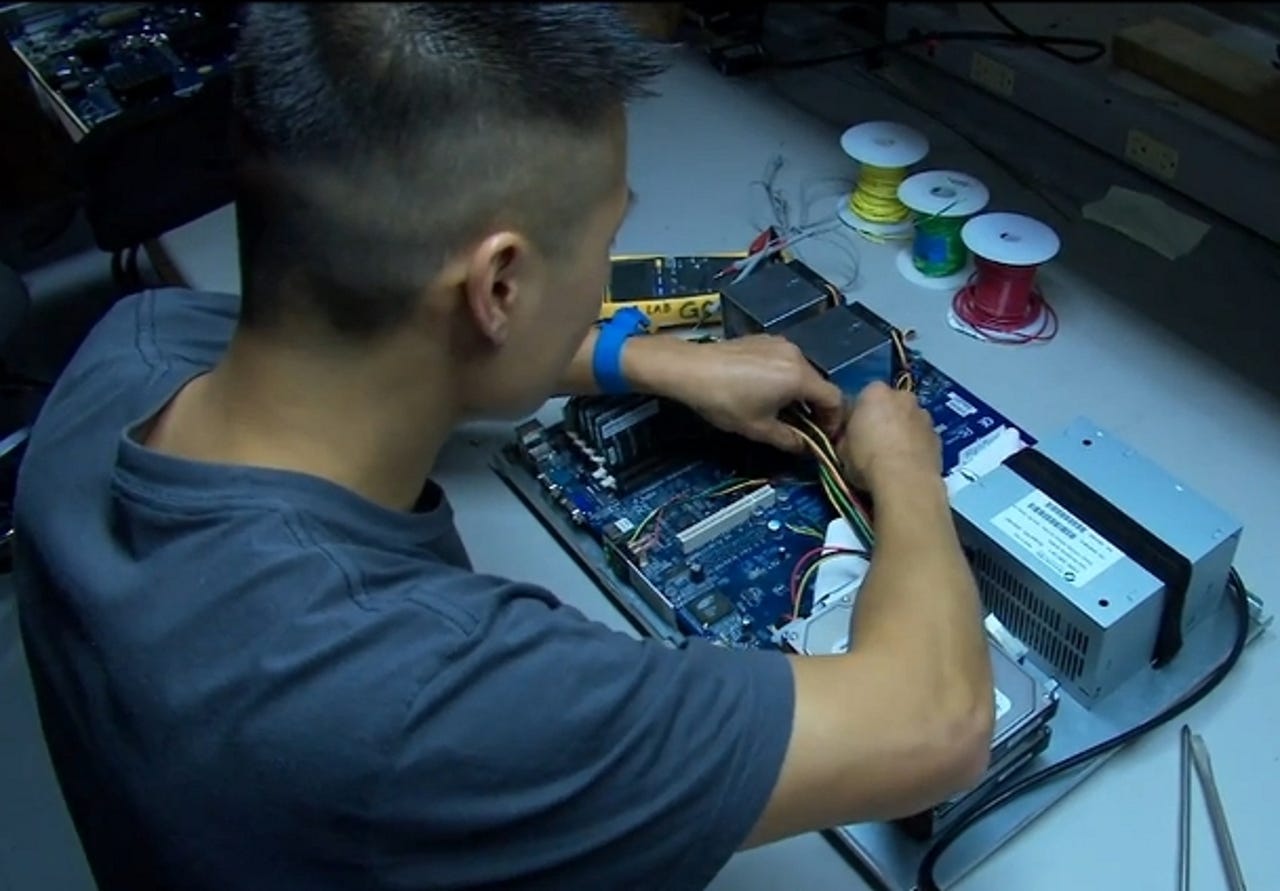
The security process starts with the design of Google's servers - with the machines custom-built to Google's specifications and running a specialised, stripped-down version of the Linux OS.
Google claims that the customised hardware and software limits the vulnerabilities of the machines.
Google staff have to go through a series of identity checks to gain access to the datacentre building and different parts of the facility.
Staff at the datacentres carry identity badges that are made using lenticular printing, which makes them difficult to forge.
In some of Google's datacentres, staff identity is checked by scanning their irises, as seen here.
Google takes a variety of steps to protect customer data stored on its datacentre hard drives, a rack of which are seen here.
Customer data is stored in multiple locations, the files that store the data are given random file names and are not written in clear text, so they are not easily readable by people.
If there is a fire or any other disruption at the datacentre, customers are able to access their data from another datacentre location.
Google tracks the location and status of each hard drive in its datacentres.
If there is a problem with a hard drive, it's reformatted and retested. If the drive does not pass these tests it's then removed, and the data on the drive is overwritten and verified to make sure it contains no customer data.
Drives that are no longer in use at the datacentre are destroyed in a multistep process to ensure that the data they contained is not recoverable.
The first step is putting drives into the crusher, where a steel piston is pushed through the drive deforming the drive's platters and making them unreadable.
The next stage of the destruction process is putting the drives through a shredder that reduces the drives into fragments.
Information stored on hard drives inside the datacentres is also backed up on magnetic tapes, such as the banks of tapes seen here.
Video surveillance allows Google staff to monitor datacentres, with the help of video analytics software that can detect anomalies in the video and tip off security staff.
Some datacentres also have thermal imaging cameras to identify the heat signature of potential intruders.
Each datacentre has emergency back-up generators, which are capable of powering the datacentres in the event of a power failure.
Datacentres are connected to the internet via high-speed fibre optic cable, with multiple redundant connections to provide access to the datacentre in the event of the failure of a single connection.