440 million Android users installed apps with an aggressive advertising plugin

Over the past year, roughly 440 million Android users have downloaded apps from the official Google Play Store that contained an advertising library that showed aggressive, out-of-app ads.
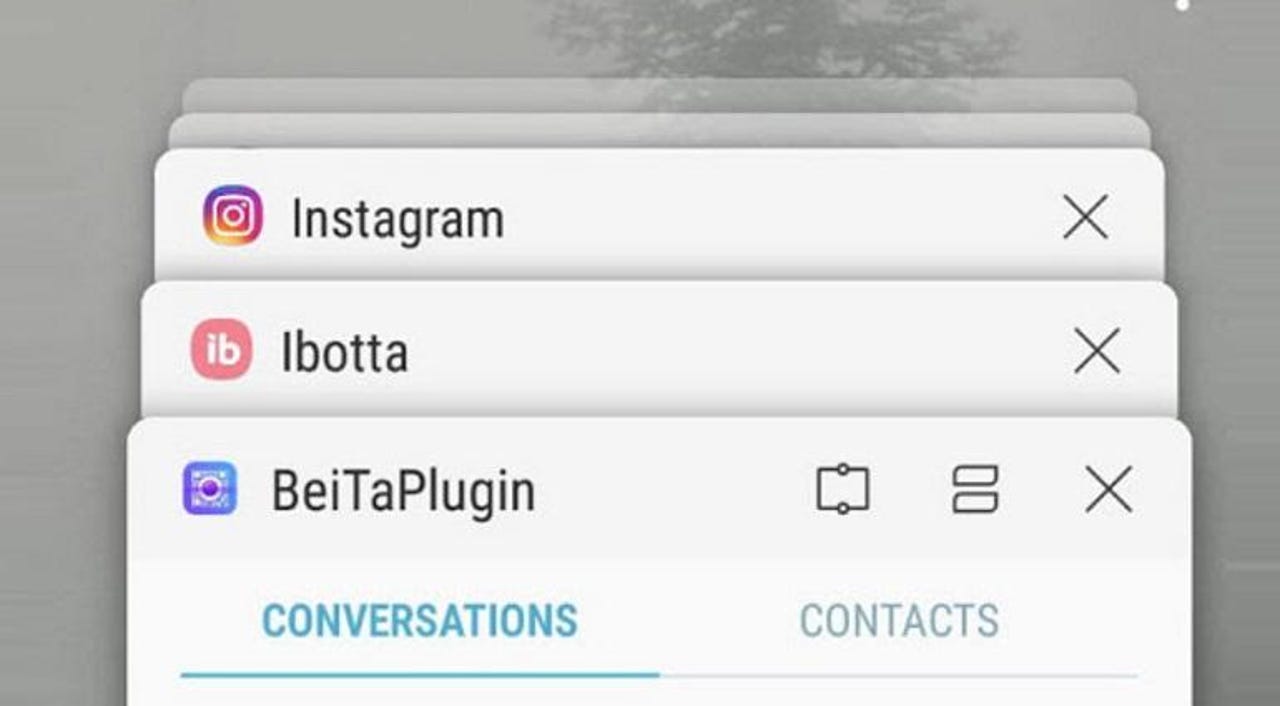
This advertising library, called the BeiTaPlugin, was found embedded in 238 applications, Kristina Balaam, Security Intelligence Engineer at Lookout said in a report published today.
Balaam said Lookout notified Google of the library's intrusive behavior, and Google notified all the affected apps' developers, in turn.
"As of May 23rd, 2019, the 230+ affected applications on Google Play have either been removed or updated to versions without the BeiTa Plugin," Balaam said.
How the BeiTaAd adware worked
Over the past few months, the official Google Play Store has faced a rash of adware infestations [1, 2, 3, 4, 5]. The BeiTaPlugin is just the latest software developer kit (SDK) in a long line of advertising libraries that have been caught misbehaving inside legitimate apps.
But this wasn't the case in the beginning. The BeiTaPlugin has been around since the start of 2018, and for the most of it, the SDK has worked as intended, providing app developers with a simple package that automated the display of online ads inside their apps.
The SDK was trusted in developer circles because it came from a legitimate company -- Chinese mobile internet company CooTek -- who used it as the advertising component for its TouchPal app, a custom keyboard app installed by over 100 million users.
But some time this year, the SDK began misbehaving and abusing the trust that other developers had put into it.
Starting somewhere in February and March, users of apps that used the BeiTaPlugin started noticing an influx of ads and popups that were being shown out of the blue, outside of running apps, and blocking access to the phone's screen and features.
"While out-of-app ads are not particularly novel, those served by this plugin render the phones nearly unusable," Balaam said. "Users have reported being unable to answer calls or interact with other apps, due to the persistent and pervasive nature of the ads displayed."
The BeiTaPlugin developers appear to have known this behavior wouldn't sit well with their users and tried hiding the SDK's aggressive new advertising practices by heavily obfuscating their code.
Furthermore, they also delayed any ad and popup displays by 24 hours after a user first opened a tainted app, a trick that made it incredibly difficult for users to pinpoint the source of the ads.
However, the SDK's shady behavior was eventually discovered when its aggressive popups caught the eye of trained mobile security researchers, who were quick to identify the source of all of users' problems.
Balaam's report on the BeiTaAd adware includes the full list of 238 applications that once used to contain the BeiTaPlugin code. Users can check this list to see if they've installed any of these apps in the past, and update them to newer versions that do not include the BeiTaPlugin code, or remove the appps from their devices.
How to switch from iPhone to Android without losing too much time, sleep, and your data!
Related malware and cybercrime coverage:
- Hollywood lie: Bank hacks take months, not seconds
- CEO who sold encrypted phones to criminal gangs gets nine years in prison
- New HiddenWasp malware found targeting Linux systems
- GandCrab ransomware operation says it's shutting down
- I2P network proposed as the next hiding spot for criminal operations
- New Iranian hacking tool leaked on Telegram
- The dark web is smaller, and may be less dangerous, than we think TechRepublic
- Game of Thrones has the most malware of any pirated TV show CNET