A crypto-mining botnet has been hijacking MSSQL servers for almost two years

Since May 2018, a malware botnet has been launching brute-force attacks against Microsoft SQL (MSSQL) databases to take over admin accounts and then install cryptocurrency mining scripts on the underlying operating system.
The botnet, detailed in a report published today by cyber-security firm Guardicore and shared with ZDNet, is still active and infecting roughly 3,000 new MSSQL databases each day.
Guardicore named the botnet Vollgar based on its predisposition to mine the Vollar (VDS) cryptocurrency alongside Monero (XMR), the de-facto alt-coin mined by most of today's botnets.
"During its two years of activity, the campaign's attack flow has remained similar - thorough, well-planned and noisy," said Ophir Harpaz, a cybersecurity researcher for Guardicore.
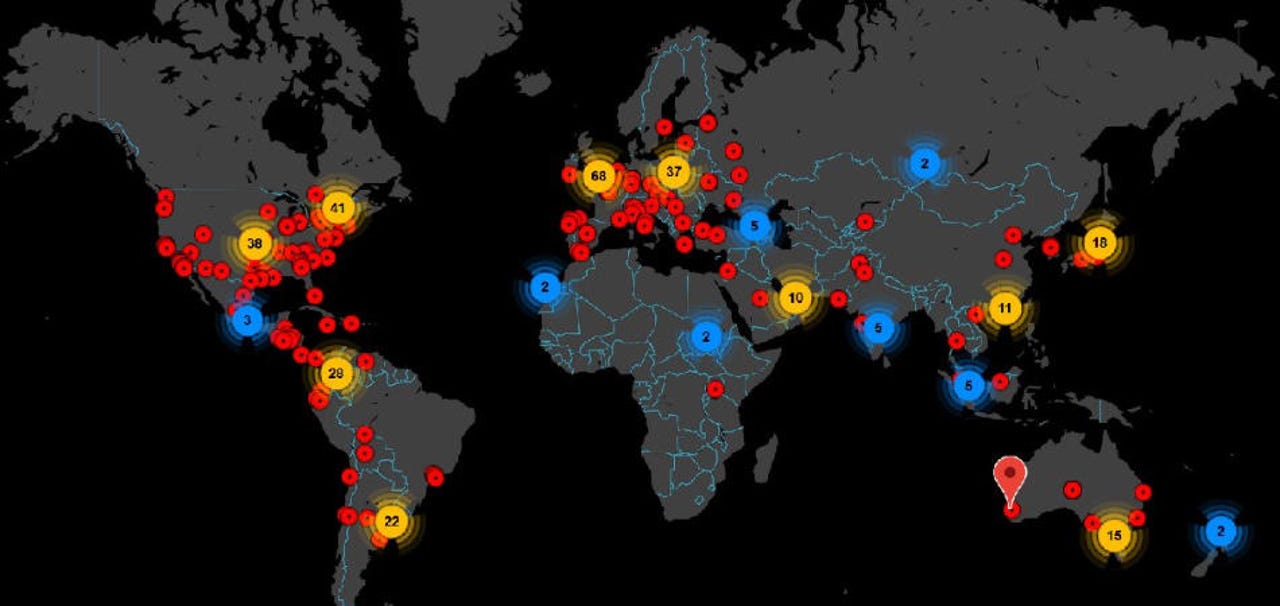
The brute-force attacks that seek to guess the password of MSSQL servers have sprayed the entire internet. Guardicore says that since May 2018, they've more than 120 IP addresses used to launch attacks, with most IPs coming from China.
"These are most likely compromised machines, repurposed to scan and infect new victims," Harpaz said. "While some of them were short-lived and responsible for only several incidents, a couple of source IPs were active for over three months."
Detection scripts are available on GitHub
Harpaz said that the botnet has been in a constant churn, with the botnet losing servers and adding new ones daily. Per Guardicore, more than 60% of all hijacked MSSQL servers remain infected with the Vollgar crypto-mining malware only for short periods of up to two days.
Harpaz said that almost 20% of all MSSQL systems, however, remain infected for more than a week, and even longer. Harpaz believes this is because either the Vollgar malware manages to disguise itself from the local security software, or the database isn't running one in the first place.
However, the Guardicore researcher also points out another interesting statistic -- that 10% of all victims get reinfected with the malware.
Harpaz says this usually happens either because administrators do not remove all of the malware's modules properly, leaving the door for the malware to reinstall itself.
To help victims MSSQL administrators, Guardicore has published a GitHub repository with scripts to detect files and backdoor accounts created by the Vollgar malware on infected hosts.
Guardicore is tracking more than 30 crypto-mining botnets
This marks the fifth cryptocurrency mining botnets that specifically target MSSQL databases that Guardicore has discovered since May 2017. Previous botnets include the likes of Bondnet, Hex-Men, Smominru, and Nansh0u.
However, in an interview with ZDNet this week, Harpaz puts the number of crypto-mining botnets at well over 30. All in all, the Guardicore researchers said that these botnets control between thousands and even tens of thousands of machines worldwide, on a daily basis.
Most of these crypto-mining botnets don't pigeon-hole themselves to specific server tech -- like the Vollgar botnet, which targets primarily MSSQL databases.
Botnet scans target a broad spectrum of server software, which they use as entry points to plant their malware. Harpaz says that based on data from Guardicore's Global Sensors Network, the top 5 most scanned ports/protocols are SSH, SMB, FTP, HTTP, and MS-SQL.
"It is hard to say whether each and every one of these scans develops into a cryptomining attack -- but our experience shows that this type of campaign makes the most immediate attack vector for threat actors to make a profit," Harpaz told ZDNet.
"Cryptomining groups are looking for two things: resourceful machines, and targets in mass-scale," the researcher added.
"Database servers, as well as RDP servers, tend to run on machines with higher compute power, making them better workers for the cryptomining task.
"Attackers crave these machines so much that they put significant effort into destroying other attack groups' processes and files to obtain full control of the precious resource," Harpaz told ZDNet. A feature that removed the scripts of competing botnets is also present in Vollgar's code.
Harpaz told ZDNet that most botnets still focus on mining the Monero cryptocurrency. However, as Monero is slowly becoming harder to mine, groups have experimented with lesser-known coins, such as Vollar (Vollgar botnet) and TurtleCoin (Nansh0u).
Going forward, Harpaz said that Guardicore plans to publish more data on the botnets it's been tracking, in an attempt to improve detection across the industry.
"We are currently working on a new Botnet Encyclopedia to share our unique data with the security community," Harpaz told ZDNet. "This will include active and past campaigns, their time spans and their associated IOCs and more."